pkr_mtsi Windows Packer Drives Widespread Powers Malvertising
A sophisticated Windows packer known as pkr_mtsi has emerged as a powerful tool for delivering multiple malware families through widespread malvertising campaigns. First detected on April 24, 2025,...
A sophisticated Windows packer known as pkr_mtsi has emerged as a powerful tool for delivering multiple malware families through widespread malvertising campaigns.
First detected on April 24, 2025, this malicious packer continues to operate actively, distributing trojanized installers disguised as legitimate software applications.
The packer targets popular tools including PuTTY, Rufus, and Microsoft Teams, using fake download websites that achieve high search engine rankings through malvertising and SEO poisoning techniques.
The pkr_mtsi Windows Packer serves as a general-purpose loader rather than a single-payload wrapper, delivering diverse malware families such as Oyster, Vidar, Vanguard Stealer, and Supper.
Distribution occurs when unsuspecting users download what appears to be legitimate software from counterfeit websites. These sites are not the result of supply chain attacks but rather carefully crafted imitation platforms designed to deceive users searching for trusted utilities.
Over the past eight months, ReversingLabs researchers noted that pkr_mtsi has evolved significantly, incorporating increasingly complex obfuscation methods and anti-analysis techniques.
Despite this evolution, the packer maintains consistent structural and behavioral characteristics that enable reliable detection.
ReversingLabs analysts identified that antivirus products frequently flag the packer using substrings like “oyster” or “shellcoderunner,” though detection coverage remains inconsistent across security tools.
Technical Execution and Memory Allocation
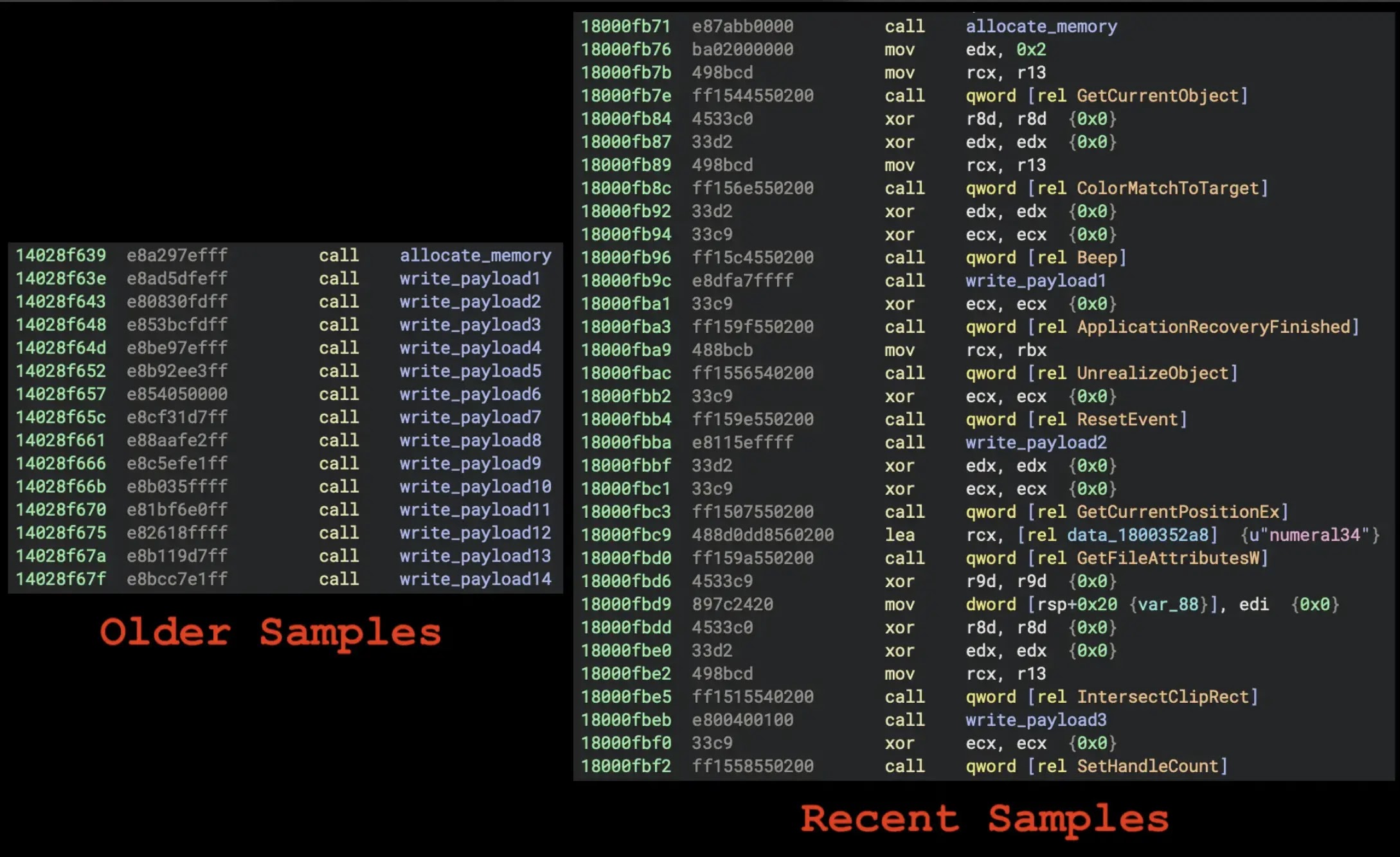
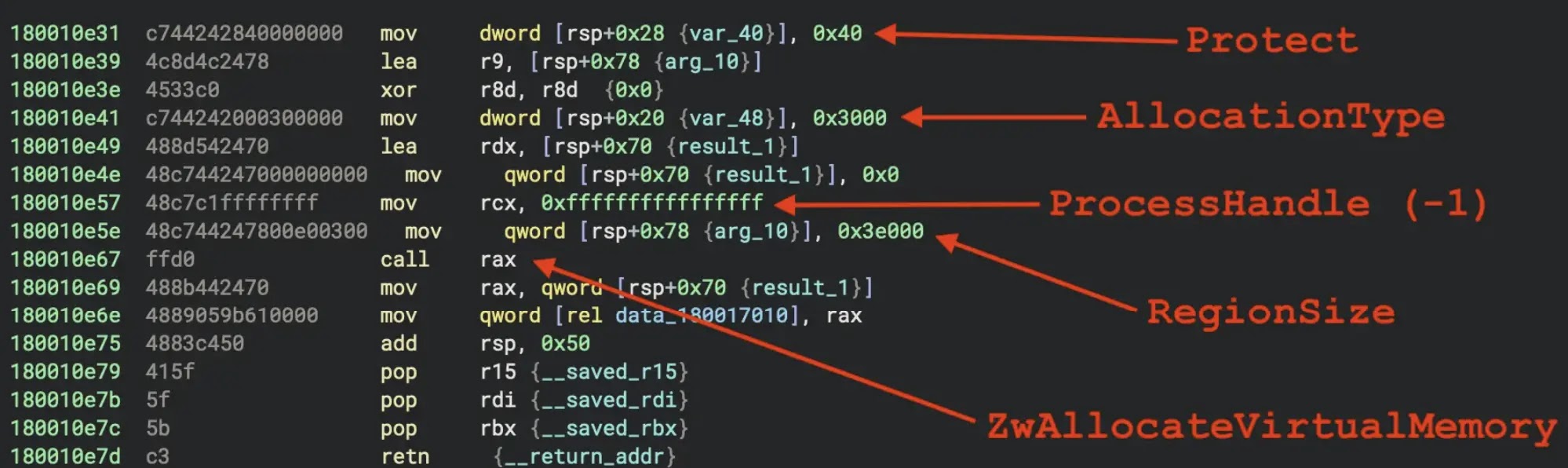
The packer operates by allocating memory regions where the next execution stage is written. Early versions used direct calls to VirtualAlloc, while recent variants employ obfuscated calls to ZwAllocateVirtualMemory.
Following memory allocation, the packer reconstructs payloads by dividing them into small chunks ranging from one to eight bytes, stored as immediate values within the instruction stream. Later variants pass these chunks through decoding routines before writing them to specific memory offsets.
ReversingLabs researchers identified that early pkr_mtsi variants resolved DLLs and API functions from plaintext strings, but newer versions now use hashed identifiers combined with Process Environment Block traversal.
The packer also employs extensive junk calls to GDI API functions, serving no functional purpose other than frustrating static and behavioral analysis efforts. These characteristics form reliable detection signatures.
The packer exists in both executable and dynamic-link library formats. DLL variants support multiple execution contexts, with one pathway triggering reliably on DLL load to unpack the next stage and final payload.
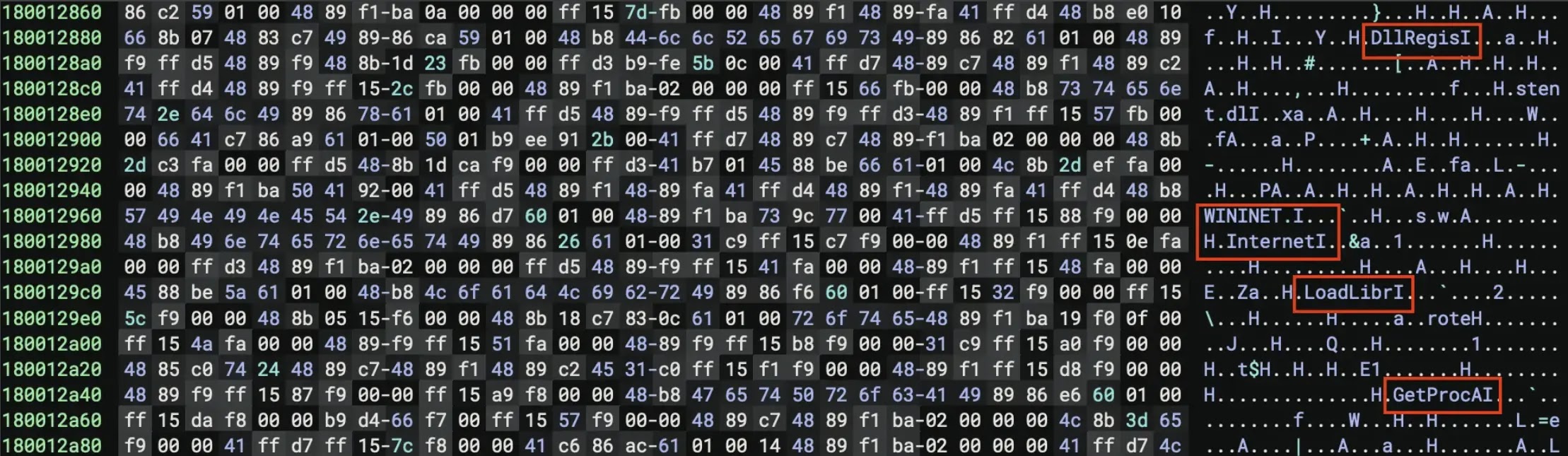
Several DLL samples export DllRegisterServer, enabling malware loading through regsvr32.exe and providing persistent execution through registry-based COM registration.
The intermediate stage consists of a modified UPX-packed module with identifying components selectively removed to evade detection. Headers, magic values, and ancillary metadata are stripped while maintaining execution capability.
This deliberate degradation complicates both static identification and automated unpacking processes, making analysis more challenging for security researchers.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.