CrazyHunter Ransomware Attacks Healthcare with Advanced Evasion
Ransomware Attacks Healthcare organizations and sensitive medical infrastructure.
This Go-developed malware represents a significant escalation in ransomware sophistication, employing advanced encryption methods and delivery mechanisms designed to bypass modern security defenses.
Healthcare institutions in Taiwan have experienced repeated attacks, with at least six known organizations falling victim to this aggressive campaign.
The ransomware’s focus on the healthcare sector is particularly concerning due to the critical nature of medical services, where system downtime can directly impact patient care, and organizations hold vast quantities of sensitive patient information that makes them valuable targets for extortion.
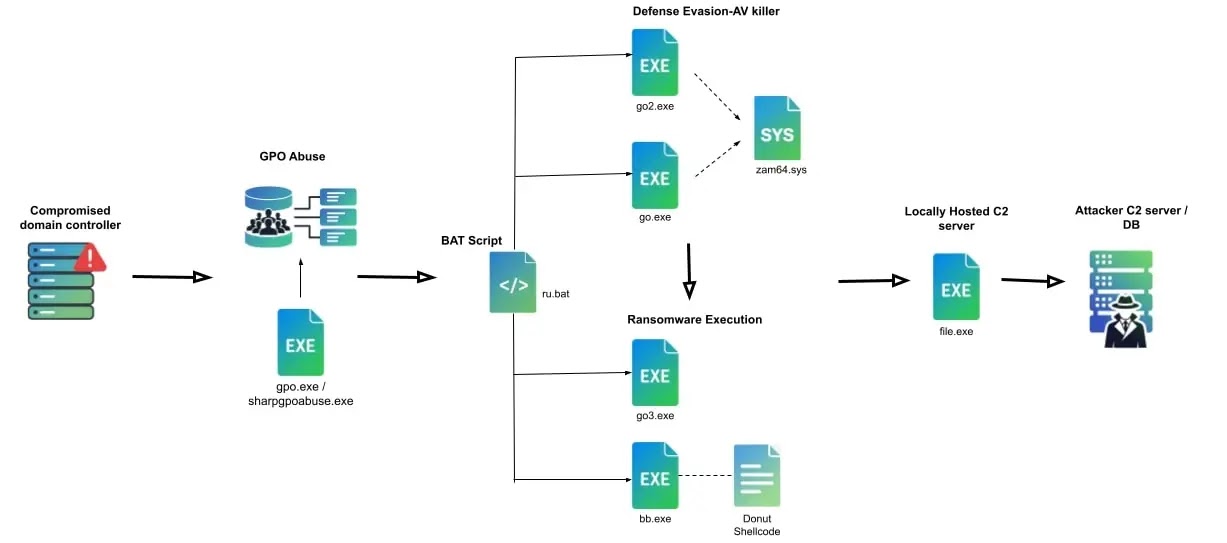
The attack methodology demonstrates tactical sophistication and operational maturity. CrazyHunter operates through a carefully orchestrated multi-stage process that begins with initial compromise through Active Directory exploitation, leveraging weak domain account passwords as the entry point.
Once inside a network, attackers employ SharpGPOAbuse to distribute the ransomware payload through Group Policy Objects, enabling rapid propagation across connected systems.
The malware then executes a coordinated sequence of operations designed to disable security systems, encrypt critical files, and maintain operational secrecy throughout the attack lifecycle.
What makes CrazyHunter particularly dangerous is its ability to evade traditional security solutions. The malware employs multiple antivirus disabling components, sophisticated memory-based execution techniques, and backup encryption mechanisms that ensure successful encryption even if primary deployment methods fail.
According to Trellix Threat Intelligence analysts, CrazyHunter ransomware was identified and tracked since its initial emergence, with security researchers noting its rapid development cycle and notable advancements in network compromise techniques.
The threat operates with structured ransom negotiation channels, including dedicated email addresses, Telegram communication channels, and anonymous network infrastructure, indicating an organized criminal operation with established victim engagement processes.
The technical infrastructure supporting CrazyHunter reveals intentional design decisions aimed at maximizing effectiveness while minimizing detection.
The malware utilizes a bring-your-own-vulnerable-driver approach, exploiting a legitimate but vulnerable Zemana antimalware driver version 2.18.371.0 to elevate privileges and terminate security software processes.
This technique allows attackers to register their malicious code as an authorized process caller using specific IOCTL codes, then systematically terminate known antivirus solutions through process termination requests.
The driver registration and termination operations use specific communication codes designed to bypass traditional security monitoring.
Encryption Mechanisms and Data Protection Strategy
CrazyHunter employs a hybrid encryption architecture combining symmetric and asymmetric cryptographic methods to ensure file protection and ransom effectiveness.
The malware uses ChaCha20 stream cipher as its primary encryption algorithm, operating with a distinctive partial encryption strategy rather than full file encryption.
Each encrypted file has one byte encrypted followed by two unencrypted bytes, creating a 1:2 encryption ratio.
This deliberate pattern significantly accelerates the encryption process, allowing rapid compromise of large file volumes while potentially evading detection from security solutions monitoring disk input-output activity patterns.
The encryption mechanism protects its cryptographic keys through Elliptic Curve Integrated Encryption Scheme, an asymmetric encryption method offering robust security with shorter key lengths compared to traditional RSA algorithms.
The malware generates unique ChaCha20 keys and nonces for every file, then encrypts these protection mechanisms using the attacker’s ECIES public key.
The encrypted key and nonce are prepended to each file, making decryption impossible without accessing the corresponding private key held exclusively by the criminal operators.
Encrypted files receive a .Hunter extension and structured format containing the ECIES-encrypted key, ECIES-encrypted nonce, and partially encrypted file content in sequential order.
This technical foundation ensures that victims cannot recover encrypted data through conventional means, creating the conditions for successful ransom negotiation and payment collection.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.