PixelCode Attack: Malware Smuggled via Image Smuggles Encoding
A novel malware delivery technique, dubbed “PixelCode,” has been demonstrated, encoding malicious executables directly into video frames. The approach allows threat actors to host these...
A novel malware delivery technique, dubbed “PixelCode,” has been demonstrated, encoding malicious executables directly into video frames.
The approach allows threat actors to host these videos on legitimate platforms such as YouTube, helping the malware evade traditional detection mechanisms.
The PixelCode technique transforms binary executable files into visual pixel data, effectively disguising malware as harmless multimedia content.
By converting each byte of an executable into structured color matrices, attackers can embed entire payloads within image or video files without exposing their raw binary form.
According to S3N4T0R, the attack chain begins with a malicious C++ payload designed for command-and-control communication.
After compilation, the executable is processed through a Python-based encoder that converts the binary into a PixelCode MP4 video file.
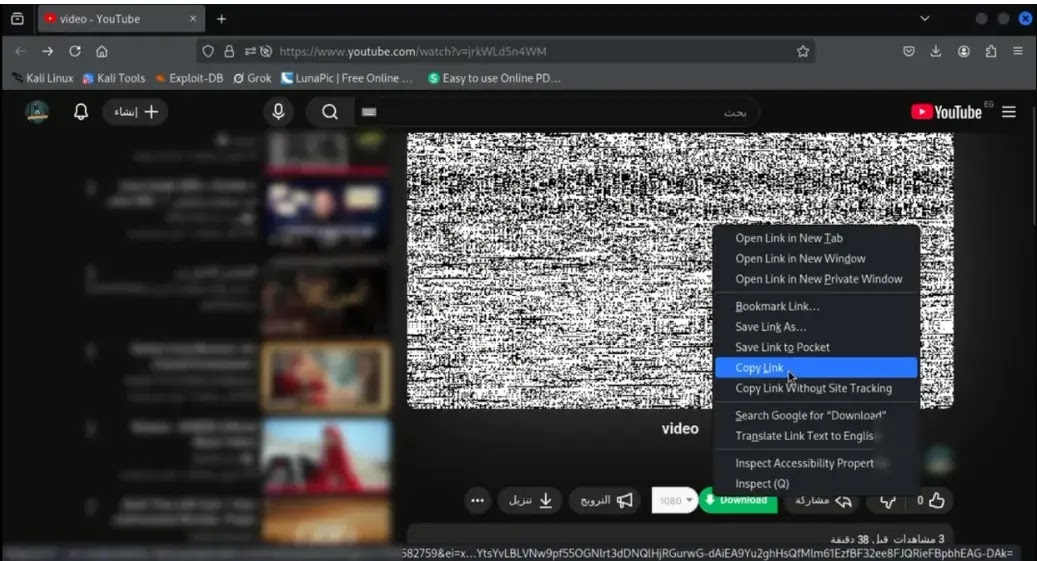
This encoded video is then uploaded to YouTube, allowing attackers to leverage a trusted platform’s infrastructure for payload hosting.
Multi-Stage Delivery Process
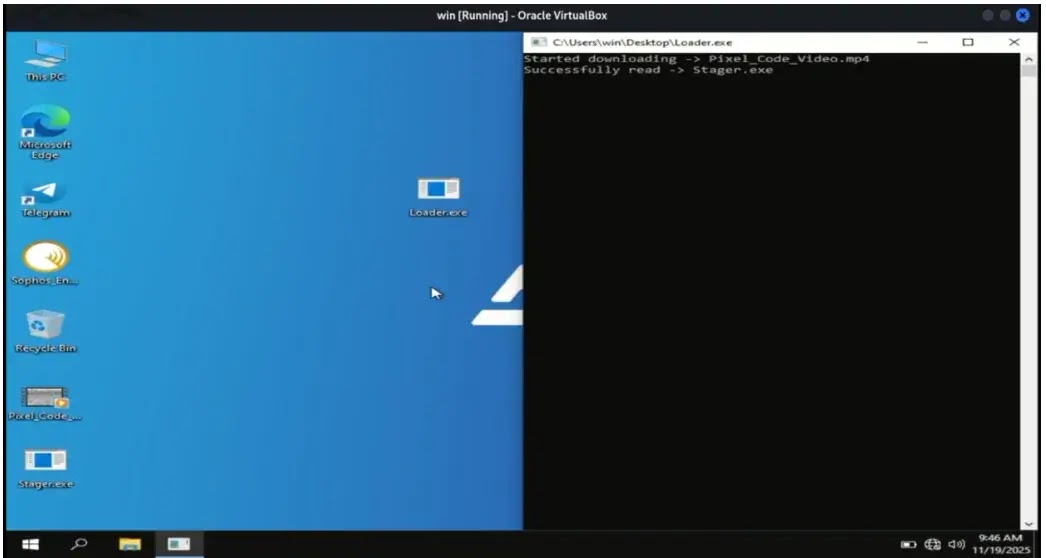
The delivery mechanism employs a sophisticated multi-stage approach. A custom C++ loader contains an embedded YouTube URL pointing to the PixelCode video.
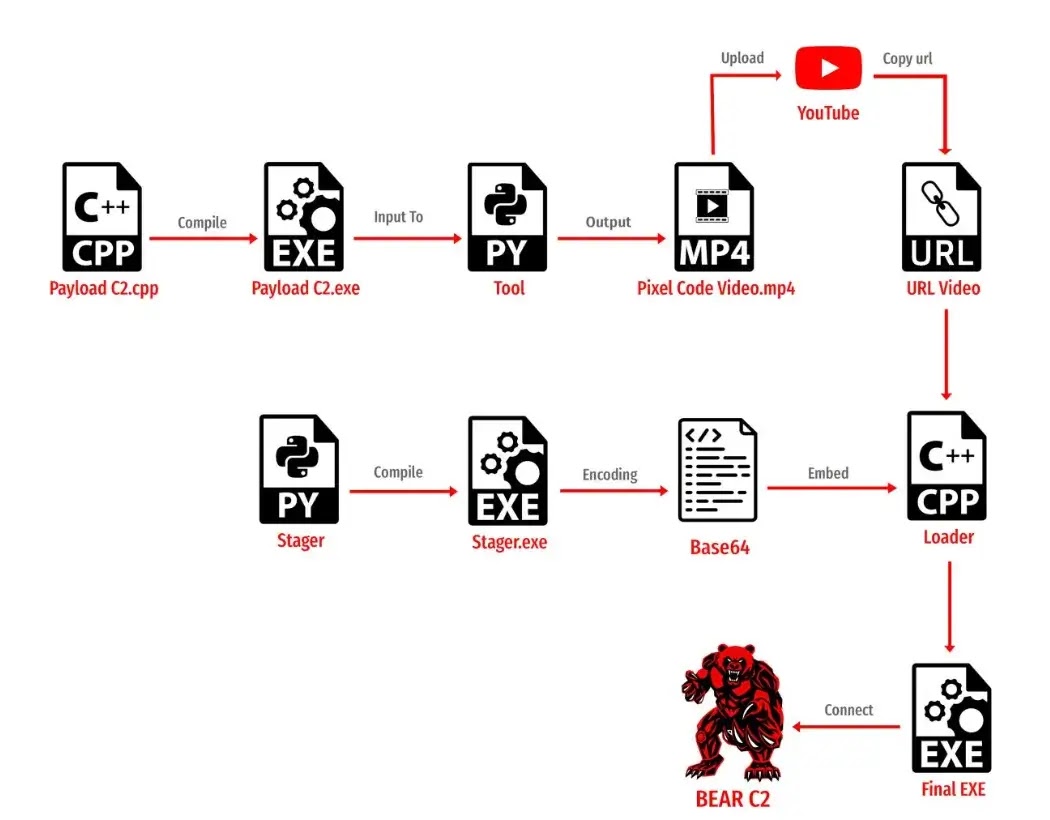
Because C++ lacks native multimedia decoding libraries, researchers embedded a Base64-encoded Python stager directly within the loader.
When executed on a target system, the loader downloads the PixelCode video from YouTube and deploys the embedded Python stager.
This stager processes the video frame by frame, extracting pixel data and reconstructing the original malicious executable in memory before execution.
The technique poses significant detection challenges for traditional security solutions. By disguising malware as legitimate video content hosted on trusted platforms, attackers can bypass conventional file-based scanning and network filtering mechanisms.
Security filters designed to inspect executable files may not scrutinize multimedia content with the same rigor.
An offensive security engineer, S3N4T0R, specializing in adversary simulation and defensive evasion, developed the proof-of-concept for research and educational purposes.
The researcher has previously created multiple APT simulation tools, including the BEAR C2 framework and adversary simulations mimicking APT28 and APT29 threat groups.
Organizations should implement behavioral analysis and memory-based detection capabilities to identify suspicious activities involving payload reconstruction.
Network monitoring for unusual video downloads followed by immediate execution patterns may help detect this attack vector.
Additionally, organizations should restrict the delivery of executable content from external video hosting platforms in high-security environments.
The PixelCode technique underscores the evolving sophistication of malware delivery methods and the importance of defense-in-depth strategies that extend beyond traditional signature-based detection.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.