ErrTraffic Breaks ClickFix Visually, Turning Attack to
GlitchFix, a new social engineering technique, has emerged, leveraging ErrTraffic—a specialized traffic distribution system. This method is designed to trick website visitors into downloading malware...
GlitchFix, a new social engineering technique, has emerged, leveraging ErrTraffic—a specialized traffic distribution system. This method is designed to trick website visitors into downloading malware by presenting visually broken web pages.
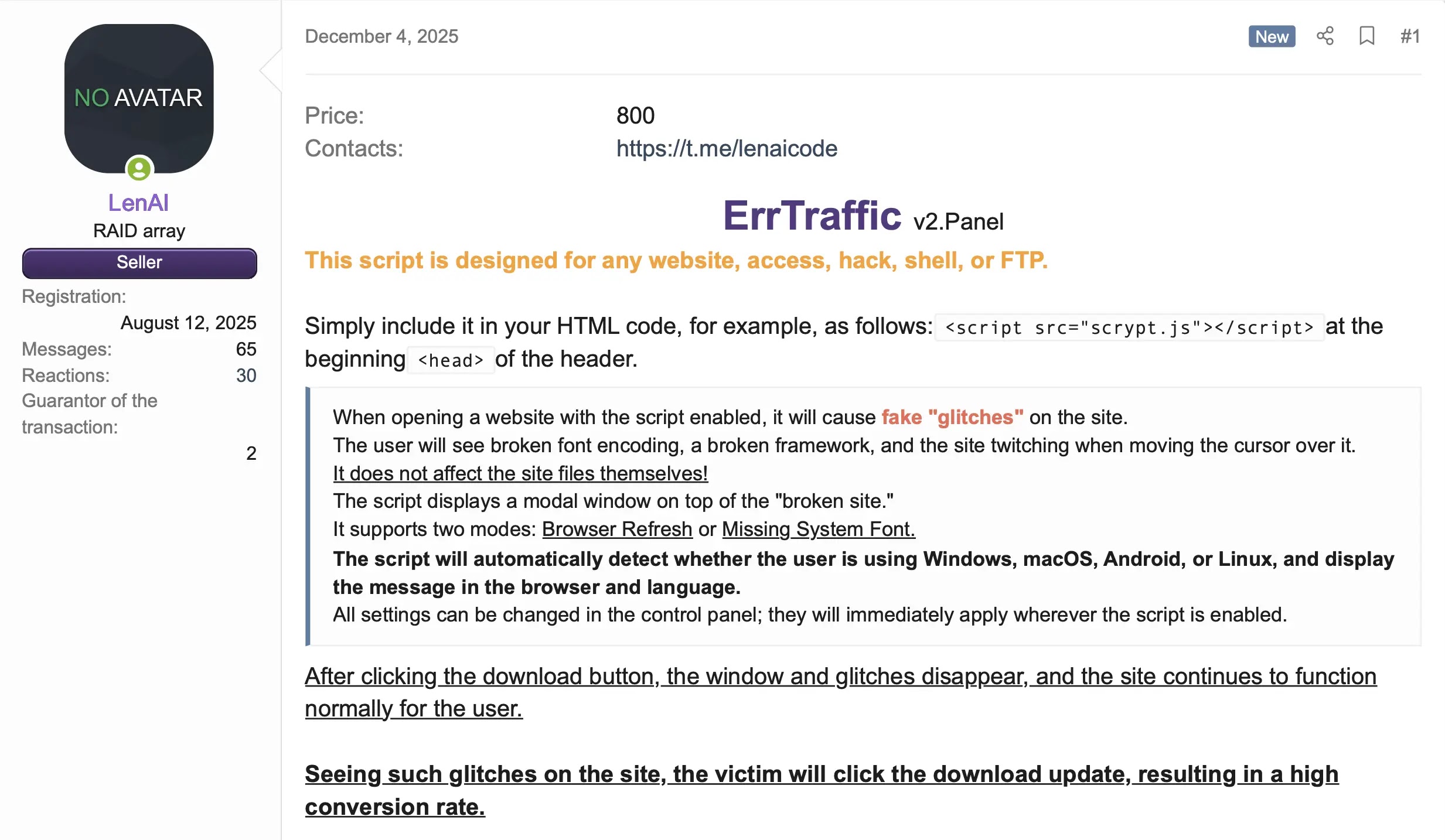
The attack platform costs around $800 and offers cybercriminals a complete solution for running deceptive campaigns across multiple operating systems.
ErrTraffic extends the traditional ClickFix approach by deliberately breaking web pages using visual distortions and chaos effects, making users believe their browser or system requires an urgent update.
The platform targets Windows, macOS, Android, and Linux devices while supporting eight languages, enabling global campaigns.
Unlike basic phishing attacks, this system creates a convincing sense of urgency by scrambling page content with garbage characters, applying CSS distortions, and triggering mouse jitter effects—all while keeping the fake update prompt perfectly readable.
Censys analysts identified the threat infrastructure after discovering five physical servers running ErrTraffic panels across three autonomous systems, hosting eleven unique domains.
The researchers found two distinct versions operating simultaneously: version 2 with unobfuscated JavaScript and Russian-only admin interfaces, and version 3 featuring XOR-based payload obfuscation and an advanced ClickFix mode.
One misconfigured instance exposed the complete source code, providing detailed visibility into the operation.
The attack delivers remote monitoring and management tools disguised as legitimate browser or font updates, including FleetDeck, ITarian MDM, and ConnectWise Control.
These digitally signed tools are commonly allowlisted by security products, making detection challenging for traditional defenses.
Infection Mechanism and Attack Workflow
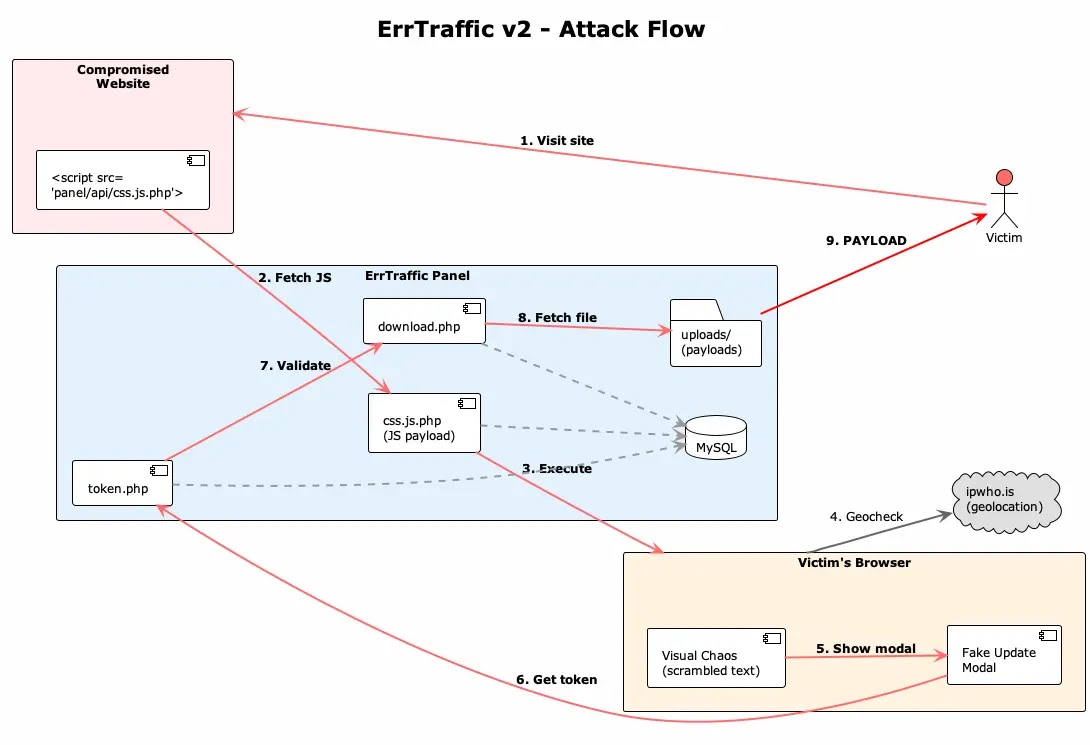
The ErrTraffic system operates through a multi-stage infection chain beginning when victims visit compromised websites containing injected script tags.
The malicious JavaScript loads from the ErrTraffic panel and immediately fingerprints the browser, operating system, and language settings.
Geographic filtering occurs next, using the ipwho.is API to block access from CIS countries including Russia, Ukraine, and Kazakhstan—a strong attribution indicator pointing to Russian-speaking threat actors.
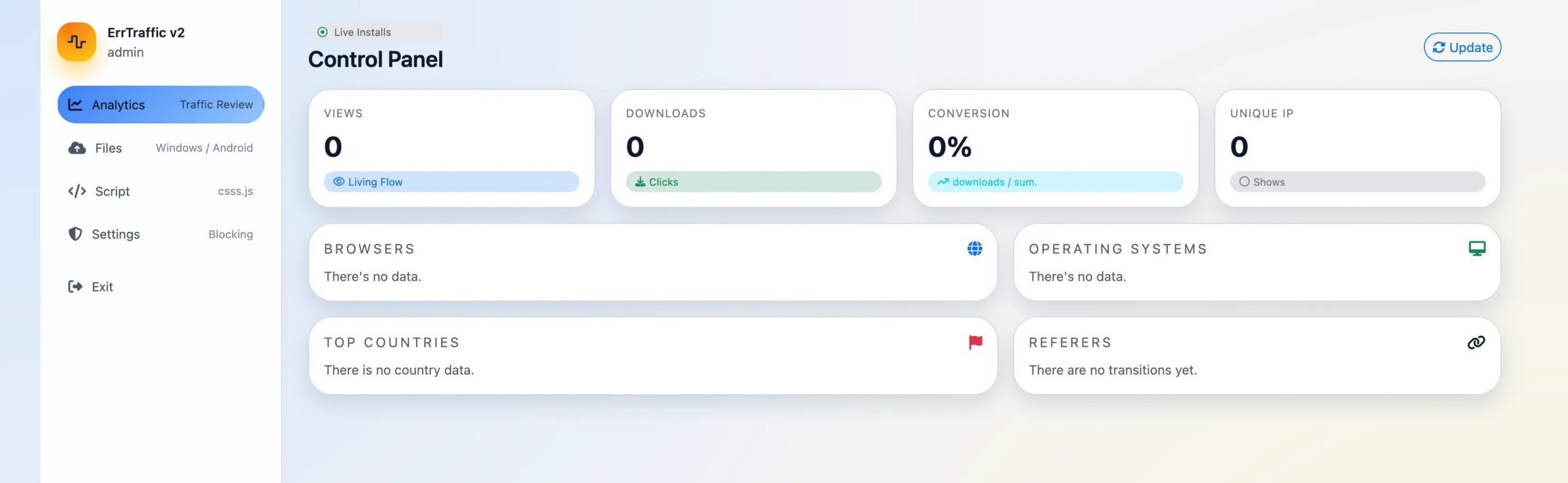
If the victim passes geolocation and bot detection checks, the page enters chaos mode. Text transforms into unreadable Unicode characters while CSS transformations skew and rotate page layouts.
The system monitors dynamic content using MutationObserver APIs, ensuring newly loaded elements receive the same corruption treatment.
After a configurable delay, typically one second, a clean modal appears offering browser updates, font installations, or in version 3, PowerShell command execution.
When victims click the update button, the script requests a one-time download token from the panel server.
The token-based delivery system prevents researchers from directly accessing payloads without completing the full attack workflow.
After validation, the system serves operating system-specific RMM installers through hidden iframes, establishing persistent remote access.
Version 3’s ClickFix mode bypasses traditional download protections entirely by copying obfuscated PowerShell commands to clipboards, instructing users to manually execute terminal commands.
The platform’s evasion capabilities include bot detection patterns targeting security scanners, headless browsers, and automated tools.
Detection signatures rely on errtraffic_session cookies and specific API paths like /api/css.js.php for version 2 and /api/css.js for version 3.
The infrastructure uses cheap top-level domains and free subdomain services, with some panels impersonating government agencies like update211.security-ssa-gov.com.
Defenders should focus on network monitoring for errtraffic_session cookies, educating users about fake update prompts, and tracking unusual RMM tool installations.
The malware-as-a-service model includes subscription features with rental expiration fields, suggesting ongoing development and operator support beyond the initial $800 purchase price.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.