Over 1,800 Windows Servers Compromised by BADIIS Malware in
Over 1,800 Windows servers worldwide have been compromised by a sophisticated cyber campaign. This operation employs BADIIS, a potent malware strain. This operation targets Internet Information...
Over 1,800 Windows servers worldwide have been compromised by a sophisticated cyber campaign. This operation employs BADIIS, a potent malware strain.
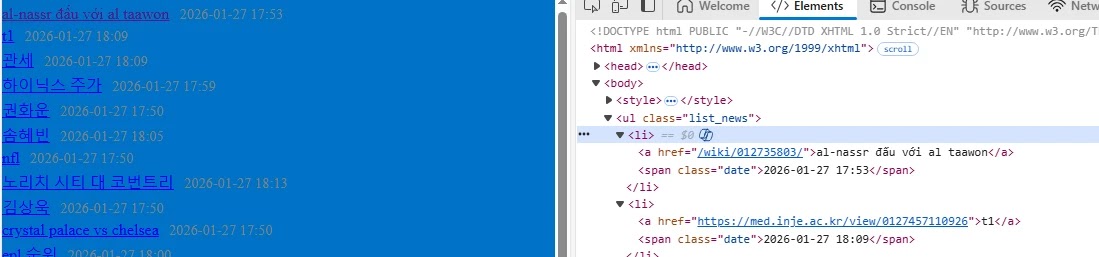
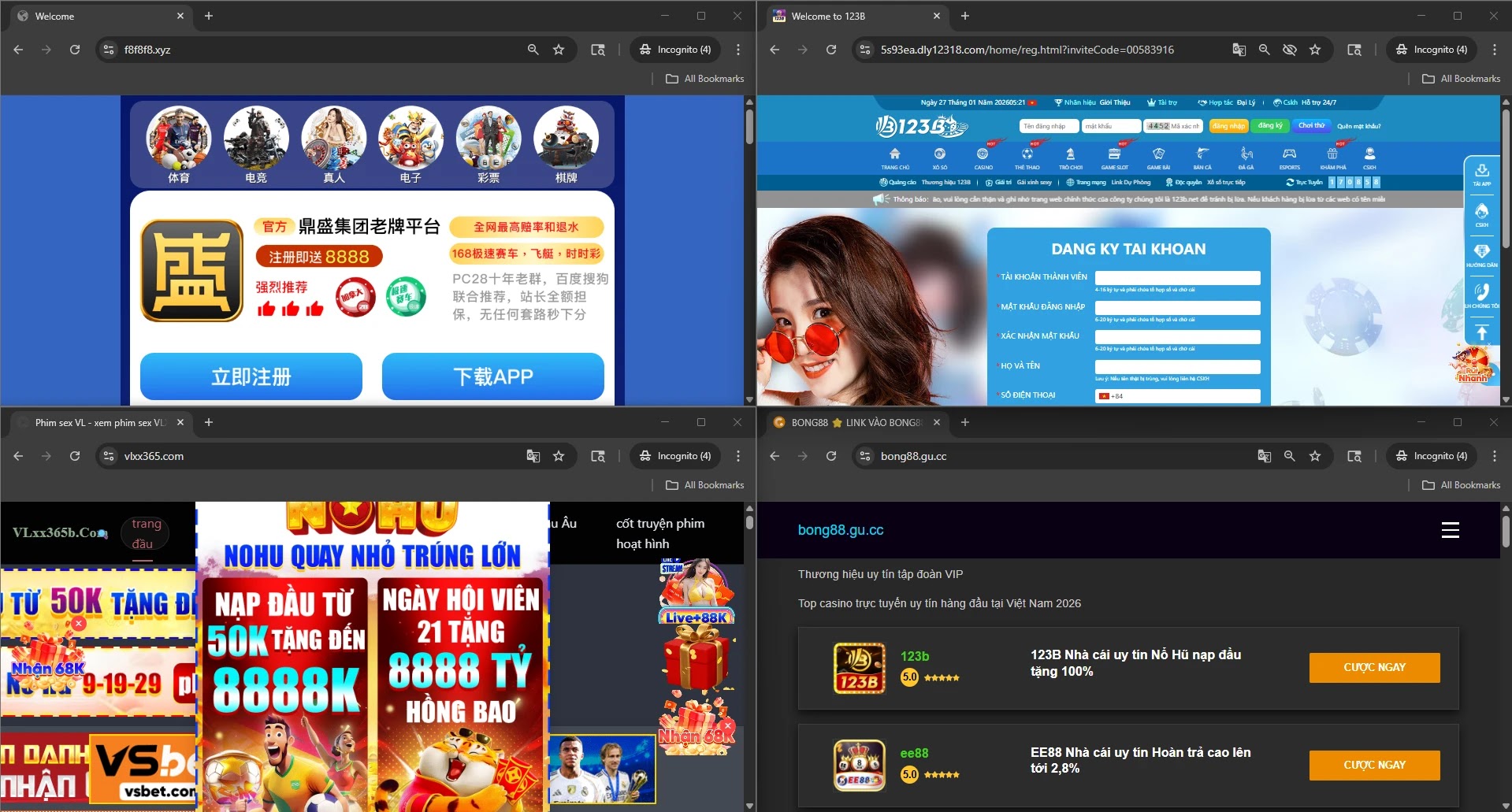
This operation targets Internet Information Services (IIS) environments, transforming legitimate infrastructure into a massive network for SEO poisoning.
By hijacking these servers, threat actors manipulate search engine results to promote illicit gambling platforms and fraudulent cryptocurrency sites, effectively monetizing compromised systems while evading traditional security defenses.
The attack vectors used in this campaign are concerning due to their ability to affect high-profile sectors, including government agencies, educational institutions, and financial organizations across multiple countries.
The malware integrates deeply into the web server’s core processes, allowing it to intercept and modify HTTP traffic in real-time.
This silent intrusion enables attackers to redirect specific visitors to malicious destinations without disrupting the server’s normal operations for regular users or administrators.
Elastic Security Labs analysts identified the malware after observing distinct post-compromise behaviors during a forensic investigation of a multinational organization.
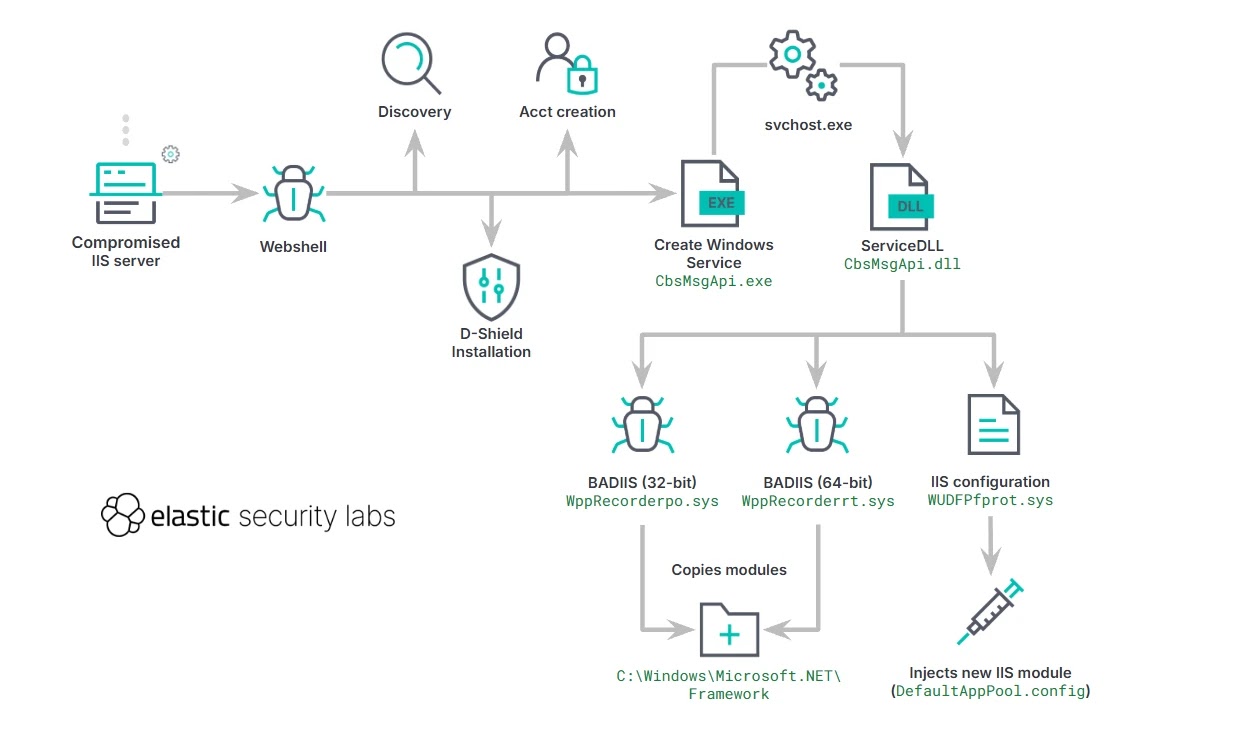
Their research links this activity to a threat group tracked as UAT-8099, noting that the campaign exhibits a high level of operational security.
The analysts discovered that the malware had been deployed across diverse industries, with a significant concentration of victims in the Asia-Pacific region, indicating a strategic effort to exploit regions with specific internet usage patterns.
Advanced Evasion and Persistence Tactics
BADIIS’s sophistication lies in its implementation as a malicious native IIS module, allowing it to achieve persistence and evade detection with remarkable efficiency.
Unlike malware running as separate processes, BADIIS loads directly into the IIS worker process, making it difficult to distinguish from legitimate server activities.
Once installed, the malware employs a “context-aware” filtering mechanism to determine how to handle incoming traffic.
It inspects the HTTP headers of every request, specifically looking for User-Agent strings associated with search engine crawlers like Googlebot.
When a crawler is detected, BADIIS injects SEO keywords and links into the server’s response, boosting the ranking of malicious sites.
Conversely, if a system administrator or regular user accesses the site, the malware serves the clean, original content. This split-view technique ensures that the compromise remains invisible to human operators while actively poisoning search results.
Furthermore, the use of direct system calls helps the malware bypass endpoint detection and response (EDR) hooks, securing its presence on the victim’s machine.
Organizations must regularly inspect installed IIS modules for unsigned or unrecognized components to detect potential infections.
It is also essential to monitor for unexpected network connections initiated by the IIS worker process and ensure all Windows Servers are patched against known vulnerabilities to prevent future compromises.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.