Open VSX Sleeper Extensions Activate New GlassWorm Malware
An additional 73 “sleeper” extensions have been discovered, escalating the GlassWorm supply chain attack against the Open VSX marketplace. Identified in April 2026, this cluster marks a dangerous...
An additional 73 “sleeper” extensions have been discovered, escalating the GlassWorm supply chain attack against the Open VSX marketplace.
Identified in April 2026, this cluster marks a dangerous shift in how threat actors distribute malware to software developers.
This activity follows a major wave discovered in March 2026, where researchers documented 72 malicious Open VSX extensions tied to the GlassWorm operation.
Earlier variants abused extension dependency features to install malicious loaders silently. However, the new April 2026 cluster shows that attackers are evolving their tactics to evade security scans.
The Sleeper Extension Strategy
A sleeper extension is a fake package published by threat actors before it is weaponized. These extensions initially appear harmless to build visual trust, gain credibility, and gather downloads.
Attackers use newly created GitHub accounts to publish cloned versions of popular tools.
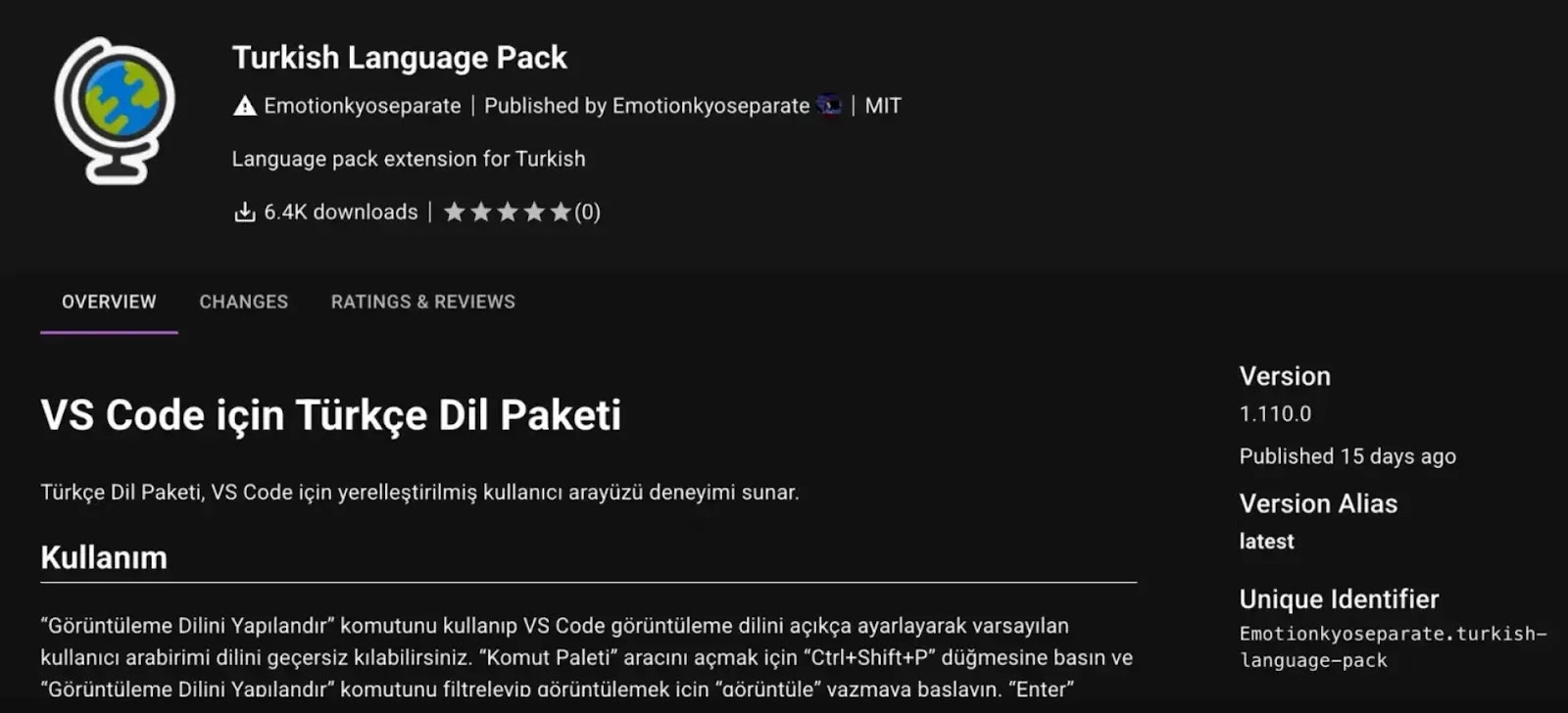
For example, attackers created a fake Turkish Language Pack for Visual Studio Code that closely mimicked the legitimate version. They copied the globe icon and the description, while simply swapping the publisher name.
Once developers install these cloned tools, the attackers wait before pushing a software update that delivers the malware. At least six of the 73 new extensions have already been activated to deliver payloads.
Evolving Delivery Mechanisms
In this latest wave, the extension acts only as a thin loader to fetch external payloads.
The malicious code is no longer directly visible in the extension’s source code, increasing the likelihood of evading detection.
The campaign uses two primary execution methods:
- Native Binaries: Bundled .node files are hidden inside the extension code. A simple JavaScript file runs the binary, which contains embedded URLs that download malicious .vsix files for IDEs such as VS Code and Cursor.
- Obfuscated JavaScript: The malicious logic is heavily obfuscated and does not rely on bundled binary files. The code decodes itself at runtime, retrieves a malicious .vsix payload from a GitHub release, and installs it through command-line paths.
Indicators of Compromise
Security teams should monitor for the following indicators:
- Native Installer Binaries (SHA256): 1b62b7c2ed7cc296ce821f977ef7b22bae59ef1dcdb9a34ae19467ee39bcf168.
- Downloaded VSIX Payload (SHA256): 97c275e3406ad6576529f41604ad138c5bdc4297d195bf61b049e14f6b30adfd.
- Malicious GitHub Hosting: github[.]com/SquadMagistrate10/wnxtgkih.
- Confirmed Malicious Extensions: outsidestormcommand. monochromator-theme, boulderzitunnel. vscode-buddies.
According to Socket Research Team, developers must verify publisher namespaces and inspect download counts carefully before installing extensions from the Open VSX marketplace.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.