Sandworm Targets Critical OT Assets, Pivoting from
Russian state-sponsored hacking group Sandworm has made a calculated pivot, shifting its attacks from compromised IT networks into operational technology systems that control physical infrastructure....
Russian state-sponsored hacking group Sandworm has made a calculated pivot, shifting its attacks from compromised IT networks into operational technology systems that control physical infrastructure.
The campaign is alarming because it does not rely on cutting-edge exploits. Instead, Sandworm walks through doors that were already left open, turning unresolved vulnerabilities into launchpads for attacks on industrial control systems.
Sandworm, also tracked as APT44, Seashell Blizzard, and Voodoo Bear, is attributed to GRU Unit 74455, Russia’s military intelligence cyber sabotage unit.
The group has a long and destructive track record, responsible for the Ukrainian power grid attacks and the 2017 NotPetya malware outbreak.
Unlike financially motivated ransomware gangs, Sandworm operates with one mission: cause disruption and, when necessary, physical damage.
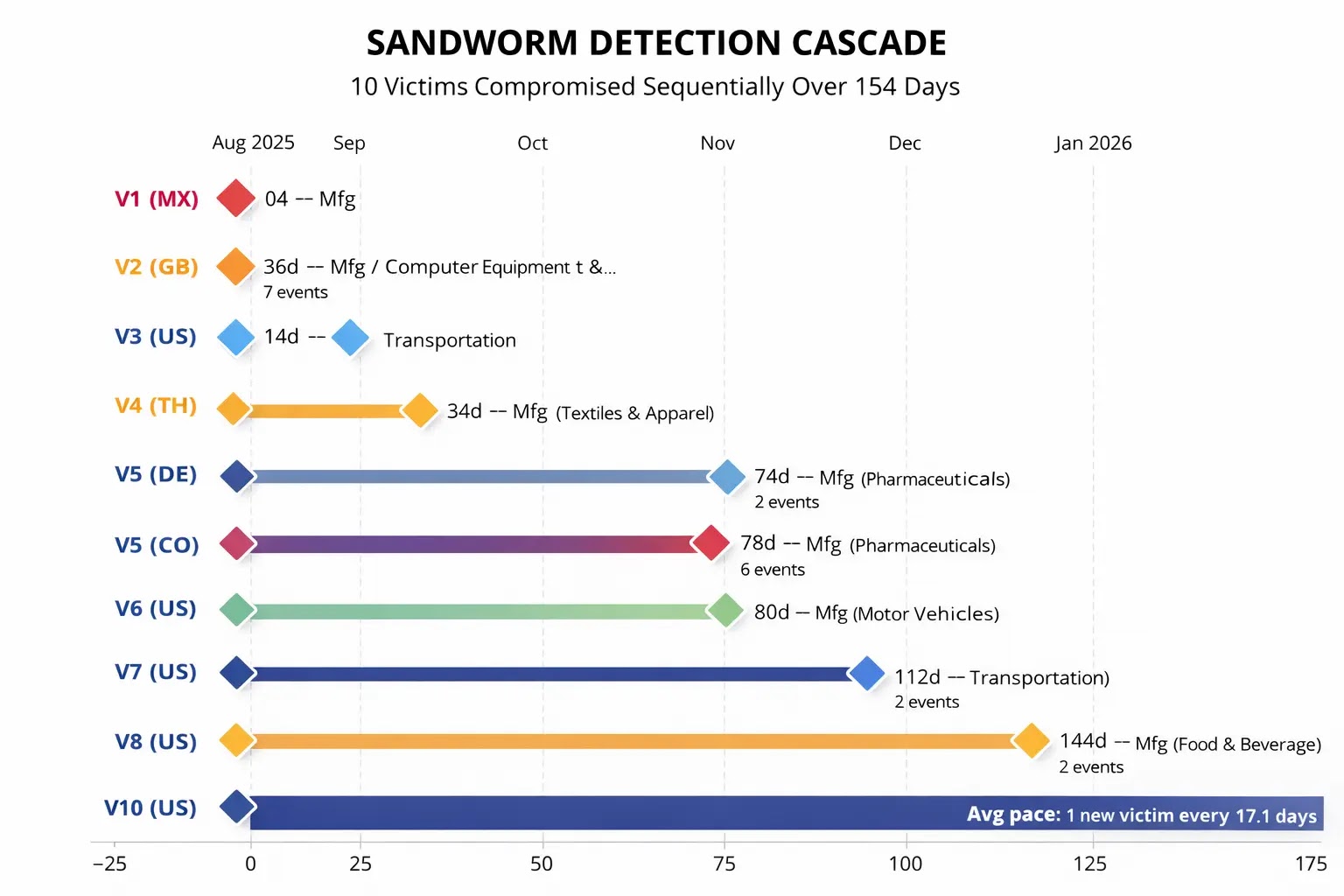
Researchers at Nozomi Networks analyzed anonymized telemetry from 10 industrial customers across seven countries, covering activity from July 2025 through January 2026.
The analysis confirmed 29 separate Sandworm events, revealing a threat actor that moves methodically, scales aggressively, and does not back down when discovered.
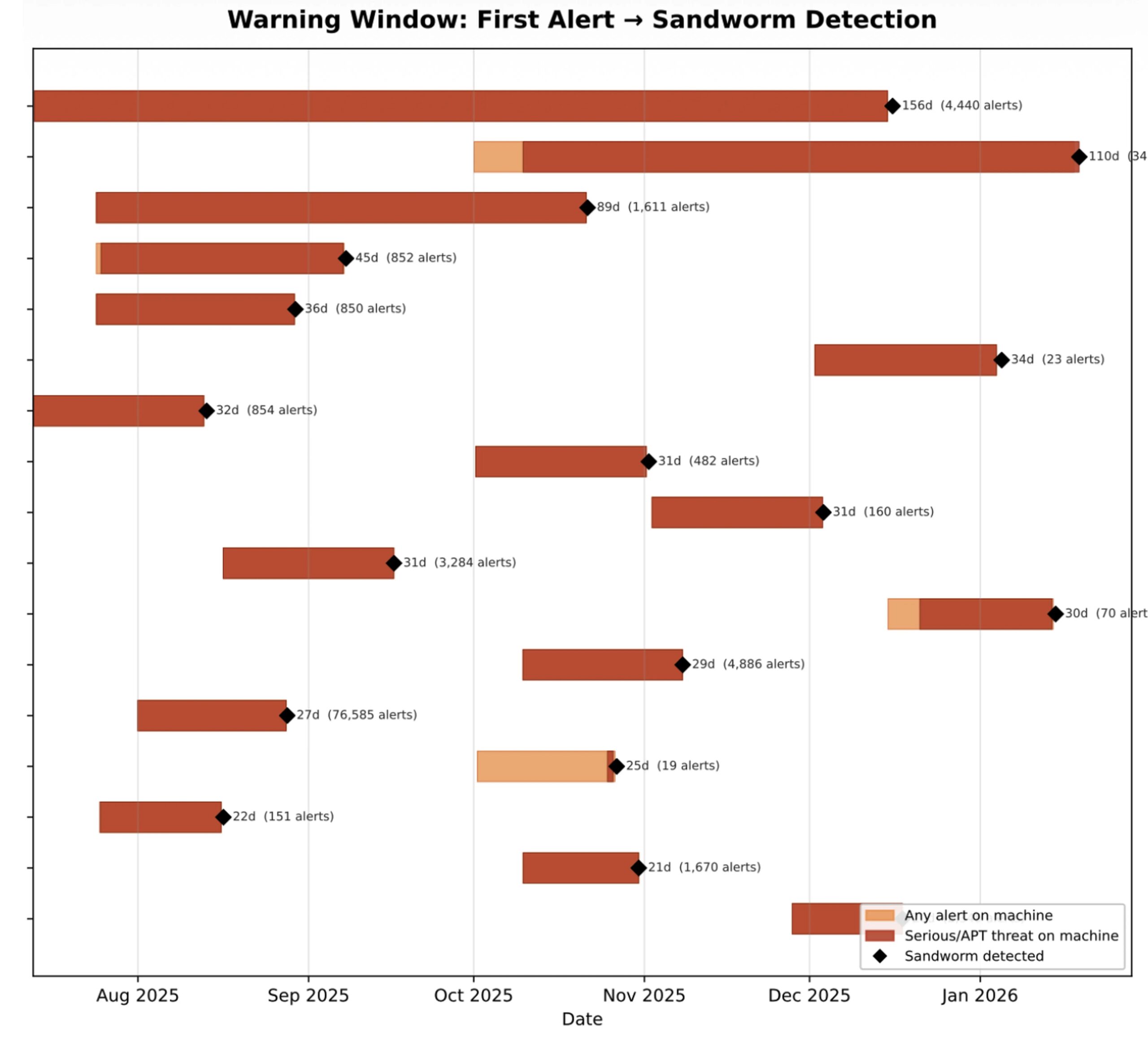
What makes this campaign particularly troubling is how preventable much of it was. Every single infected system had generated weeks or months of high-confidence security alerts long before Sandworm arrived.
From IT Footholds to OT Targets
On average, compromised systems had been sending warning signals for 43 days. These were not quiet intrusions. They were noisy, well-documented attacks that went uninvestigated.
The exploit chains in play included EternalBlue, DoublePulsar, and WannaCry, all tools that have been publicly known and patchable for years.
Sandworm did not need any new tricks. It moved into environments that other attackers had already taken over and used those footholds to push deeper into industrial territory.
Once Sandworm established a presence inside a network, it did not stay quiet. Seventeen infected machines launched lateral movement attacks against 923 unique internal targets.
In the most extreme case, a single compromised host targeted 405 internal systems on its own, and one infection event caused a 12-fold spike in alert volume. The targets were not random.
Sandworm showed clear intent to reach industrial control systems, directly hitting engineering workstations, human machine interfaces, and field controllers including remote terminal units, programmable logic controllers, and intelligent electronic devices.
At one victim site, 286 engineering workstations were targeted, while another saw 95 HMIs in the crosshairs. These are not just computers, as they manage physical equipment in factories, power plants, and transportation networks.
Nozomi Networks researchers also noted that Sandworm activity follows a predictable schedule, peaking on Wednesdays around 2:00 PM Moscow time.
This bureaucratic rhythm points to a centrally organized operation. It aligns with how Russian government and military units structure their workweek.
Escalation After Detection and Defensive Steps
One of the most alarming findings is what happens when Sandworm gets caught. Rather than retreating, the group escalates.
Across all affected environments, activity intensified after detection, with alert volume rising, new attack types appearing, more systems being targeted, and focus shifting harder toward industrial control systems.
Most victims saw escalation across four to six of seven measurable dimensions at once. This means partial detection without full containment can make things worse.
Security teams must move from detection to isolation quickly, especially for any system with access to operational technology. Incident response plans should assume Sandworm will push harder once spotted, not pull back.
Nozomi Networks recommends treating even routine alerts, such as EternalBlue or Cobalt Strike detections, as serious strategic warnings rather than background noise.
Defenders should focus on baseline hygiene, remove legacy protocols, enforce network segmentation between IT and OT environments, and ensure past compromises are fully resolved rather than just contained.
Engineering workstations and ICS management systems should be treated as critical assets, kept offline from general internet access, and monitored closely.
Sandworm consistently exploited pre-compromised environments and long-standing security gaps, meaning strong fundamentals would have stopped many of these intrusions entirely.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.