North Korean IT Worker Used Stolen ID & Allegedly Identity
A suspected North Korean operative attempted to secure a remote position at a cybersecurity firm, leveraging a stolen identity, a fake AI-generated resume, and a Voice over IP (VoIP) phone number....
A suspected North Korean operative attempted to secure a remote position at a cybersecurity firm, leveraging a stolen identity, a fake AI-generated resume, and a Voice over IP (VoIP) phone number.
The case, uncovered in June 2025, shows how North Korea’s state-sponsored IT worker scheme has grown more sophisticated and harder to spot without proper screening.
The operative applied for a Lead AI Architect position, claiming to be a Florida-based professional with over a decade of experience in AI architecture and full stack development.
The attempt failed, but it left behind a clear trail of red flags that paint a concerning picture of how these schemes operate today.
Since early 2023, North Korean, or DPRK, IT workers have been quietly infiltrating companies across the United States and other countries by pretending to be qualified remote workers.
These operatives earn wages that are then funneled back to the North Korean government, helping fund its weapons programs. The scheme is not limited to small companies.
It targets organizations of all sizes, including those in the technology, intelligence, and cybersecurity sectors. The fake candidates use stolen personal information from real people, create new email accounts, and build false online profiles to make themselves appear legitimate.
Nisos analysts identified the suspected DPRK operative after combining pre-employment Open-Source Intelligence, or OSINT, research with carefully crafted interview questions.
The operative used IP addresses 167.88.61.250 and 167.88.61.117, which are linked to the Astrill VPN anonymization network, a tool commonly associated with DPRK IT workers operating out of China.
The phone number provided, 850-308-4867, was traced as a Voice over Internet Protocol number, a common tactic used by these operatives to match their phone area code with their claimed U.S. location.
The stolen identity belonged to a real Florida resident who had lived in Palm Beach Gardens, West Palm Beach, and Greenacres.
The operative used this person’s name and address details to create multiple resume accounts across different platforms, each listing slightly different universities, employers, and locations.
All three resumes were traced back to the same real individual, who likely had no knowledge that his personal information was being misused. Nisos coordinated victim notification in connection with law enforcement following the discovery.
The impact of this kind of fraud goes well beyond one fake job application. Hiring someone tied to this scheme can expose a company to data theft, intellectual property loss, regulatory penalties, and serious damage to its reputation.
The operatives, once hired, use remote access tools to control company laptops from abroad while appearing to work locally, making detection extremely difficult for standard IT security teams.
Fake Identity Construction and the Use of AI in Job Fraud
One of the most telling aspects of this case was how the operative constructed and maintained a false identity using artificial intelligence tools and copied job description language.
The resume submitted for the Lead AI Architect role contained an unusually long list of technical skills, including programming languages, cloud platforms, agentic AI tools, and OSINT frameworks, many of which were pulled almost word-for-word from the job posting itself.
Nisos analysts noted that this pattern of mirroring job description language directly into a resume is a known tactic among DPRK IT workers, who use it to pass basic keyword screening filters used by hiring systems.
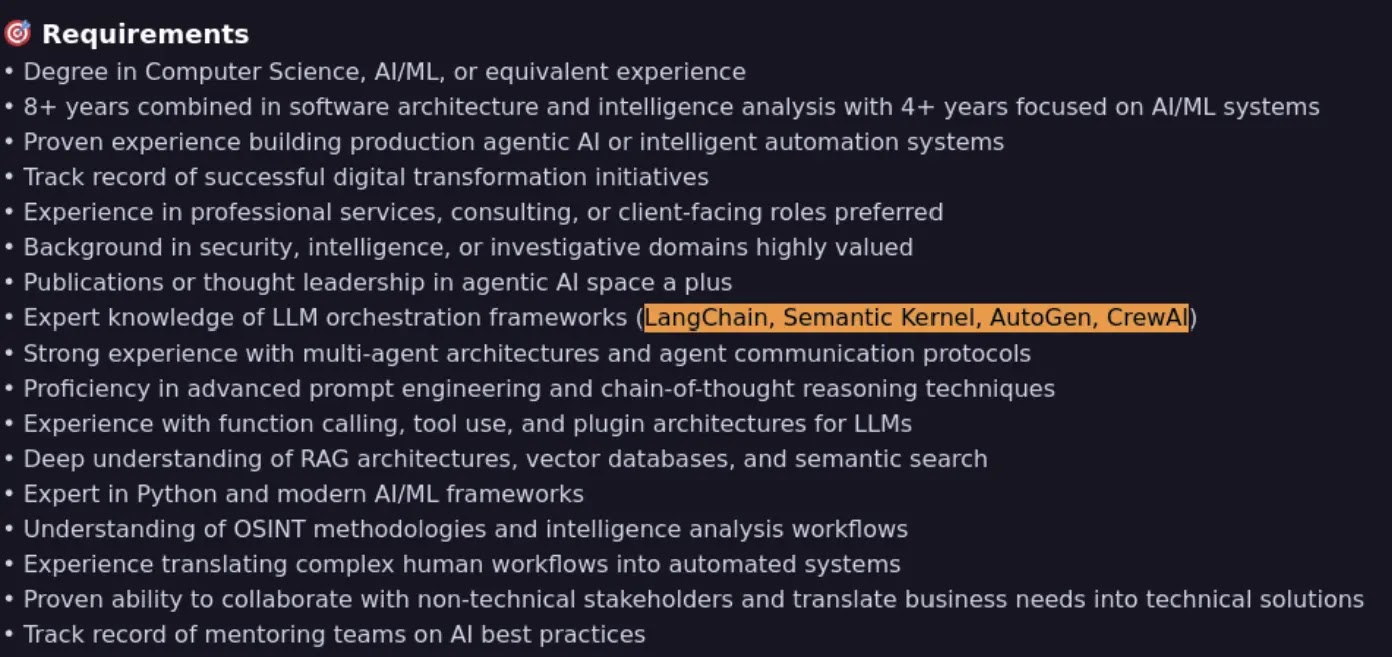
This show the overlap between the two documents was significant:-
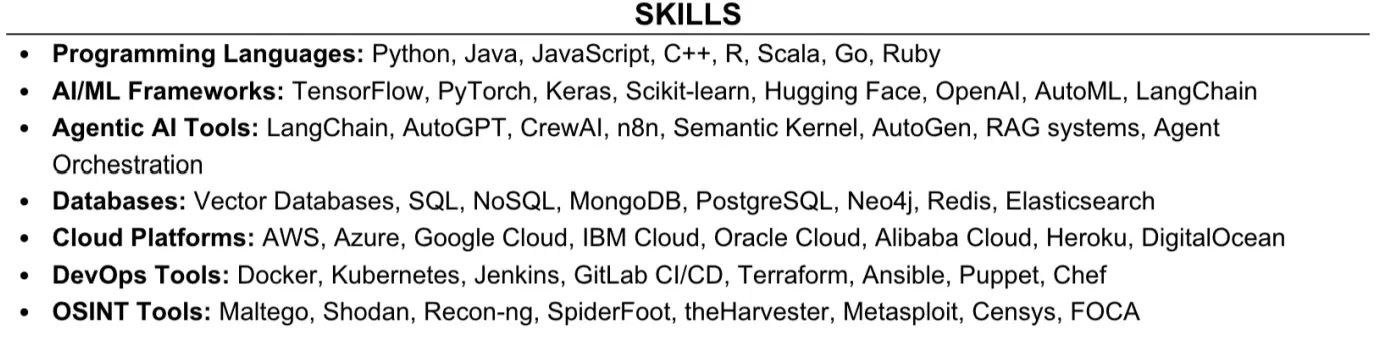
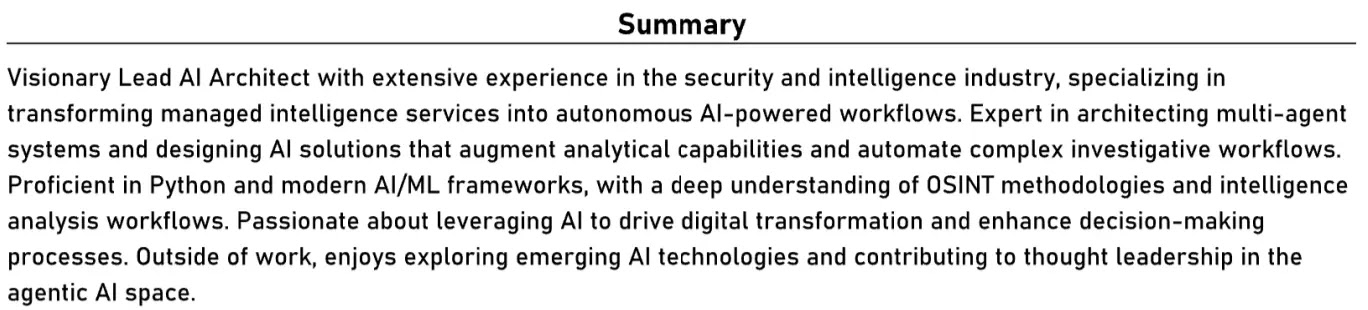
The resume’s summary section, also reused phrasing from the job description, particularly around researching and evaluating emerging agentic AI technologies.
During the virtual interview held on June 24, 2025, the operative’s behavior raised further alarms.
He frequently looked away from the camera, and when asked a deliberately fake question about a hurricane that never happened, he responded with “How can I say?” while glancing at another screen, a sign he was waiting for an AI chatbot to generate an answer for him.
When asked to share his screen and walk interviewers through past work, he abruptly closed browser tabs and ended the call. He had no GitHub portfolio and claimed all prior work was stored in private repositories he could not share.
Three separate resume accounts under the same name but with different employers, universities, and locations were uncovered across multiple platforms.
One account was created as recently as May 2025, suggesting the persona was newly built for this specific job application campaign.
The operative also provided a separate mailing address for the laptop, different from the one listed on the resume, which is consistent with how DPRK operatives redirect company devices to laptop farms.
This confirmed the device ended up in a closet alongside multiple other company-issued laptops, all controlled remotely through PiKVM devices and connected via the Tailscale mesh VPN service.
Organizations are strongly recommended to implement thorough pre-employment OSINT checks for all remote candidates, verify phone numbers and IP addresses during the application process, ask targeted questions during interviews that cannot be answered with scripted or AI-generated responses, require live screen sharing of verifiable past work, and monitor for newly created professional profiles with few connections.
Companies that lack the internal capacity to conduct these checks should work with qualified intelligence and investigations firms experienced in identifying employment fraud and insider threats.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.