North Korea Used AI Malware to Attack Devs & Engineering
North Korea-aligned hackers have launched a novel campaign, transforming artificial intelligence into a weapon to attack software teams. Using AI-written PowerShell code, the group known as KONNI is...
North Korea-aligned hackers have launched a novel campaign, transforming artificial intelligence into a weapon to attack software teams.
Using AI-written PowerShell code, the group known as KONNI is delivering a stealthy backdoor that blends real project content with malicious scripts.
This operation shows how fast threat actors are adopting AI tools to speed up development and hide their tracks.
In the latest wave, KONNI is targeting developers and engineering teams working on blockchain and crypto projects across the Asia‑Pacific region, including Japan, Australia, and India.
The attackers craft detailed requirement papers that look like real product briefs, describing trading bots, credential systems, and delivery roadmaps, then deliver them as PDF lures.
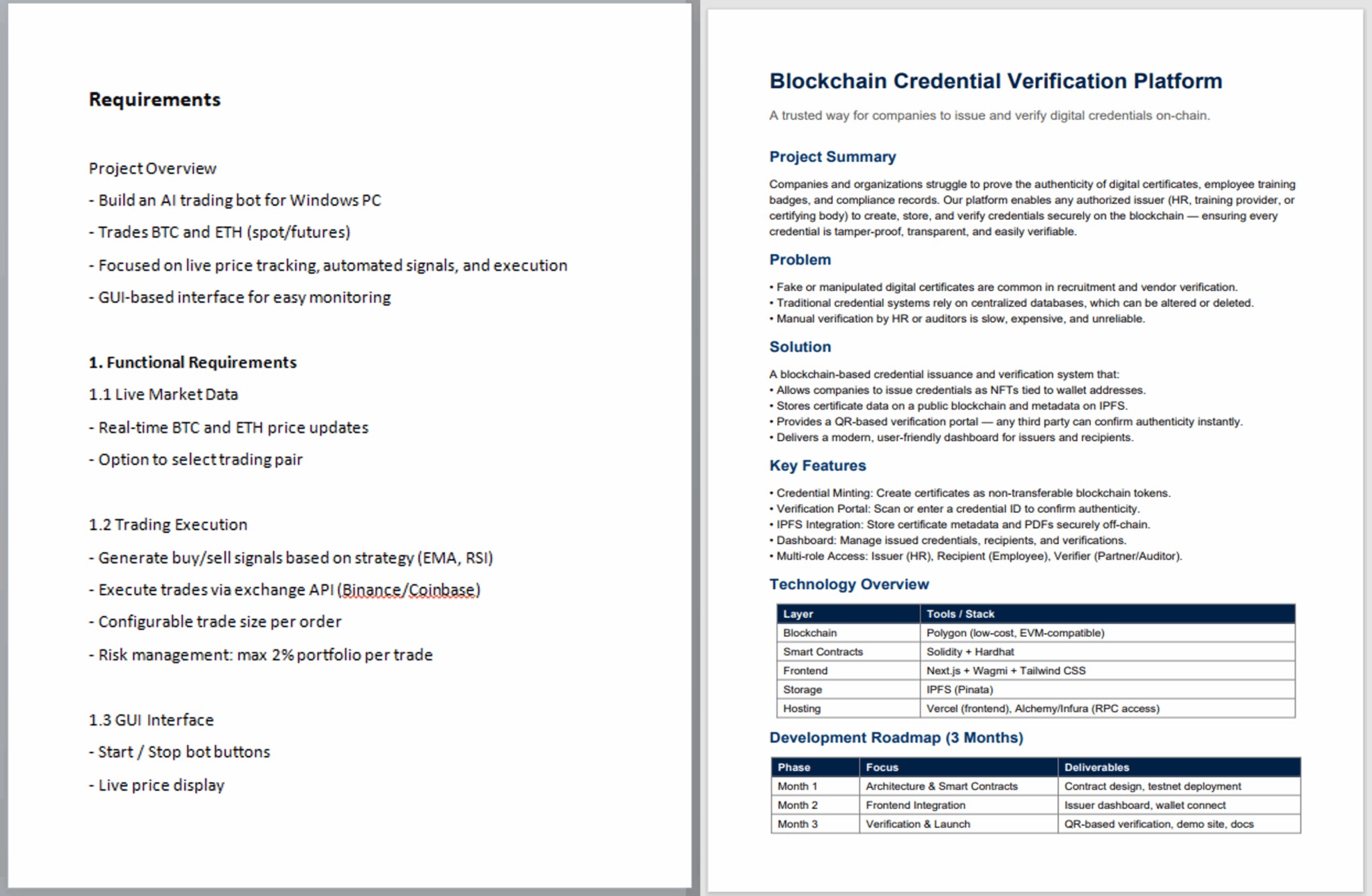
These documents are designed to win the trust of technical staff and draw them into opening attached shortcut files that silently start the infection chain.
Check Point researchers identified the activity as part of the long‑running KONNI cluster and noted that the payload is an AI‑generated PowerShell backdoor with extensive comments and clean structure.
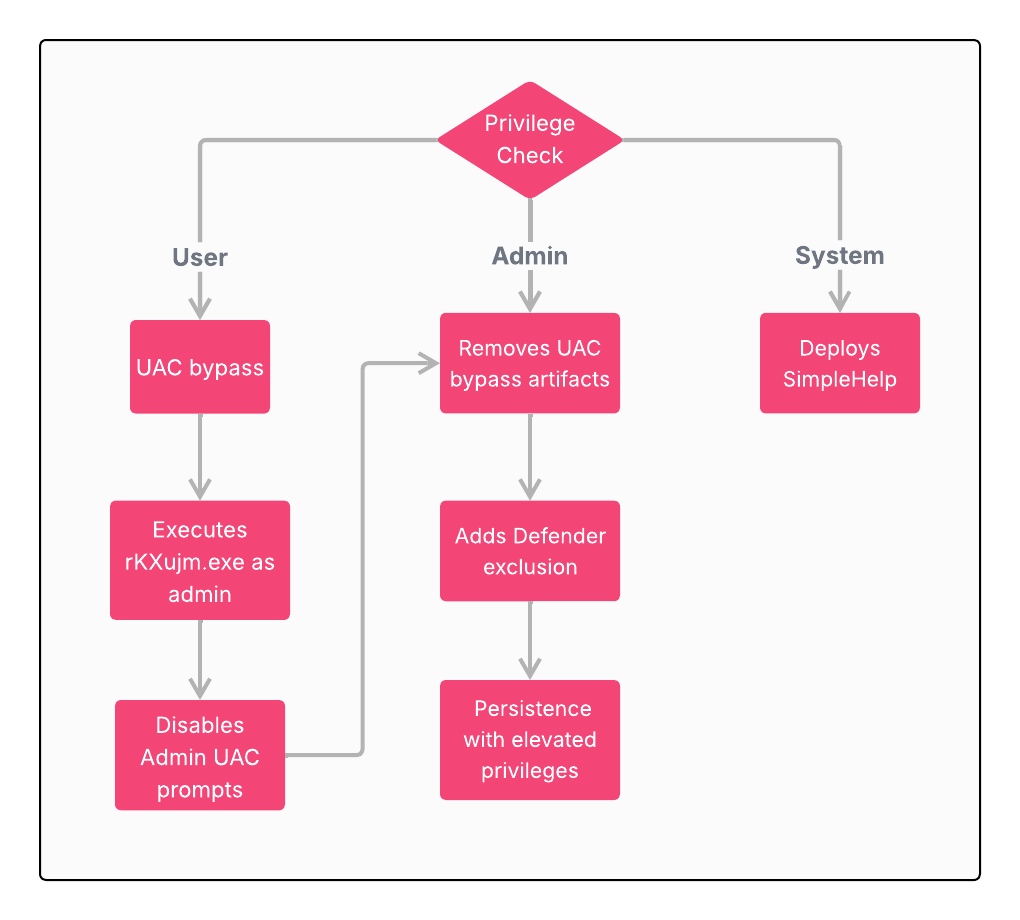
This backdoor does more than open a remote door; it gathers hardware details, checks for debugging tools, and ensures only one copy runs at a time, all while maintaining a professional, developer‑style layout.
For victim organizations, the risk goes far beyond a single compromised workstation. By targeting developers who hold access to repositories, cloud consoles, and signing keys, KONNI can pivot from one infected endpoint into entire build pipelines or production systems.
Infection Chain and Persistence Tactics
The attack begins when a target opens the ZIP archive and double‑clicks a Windows shortcut file that sits next to the PDF lure.
That shortcut runs an embedded PowerShell loader, which quietly drops a second lure document and a compressed CAB archive.
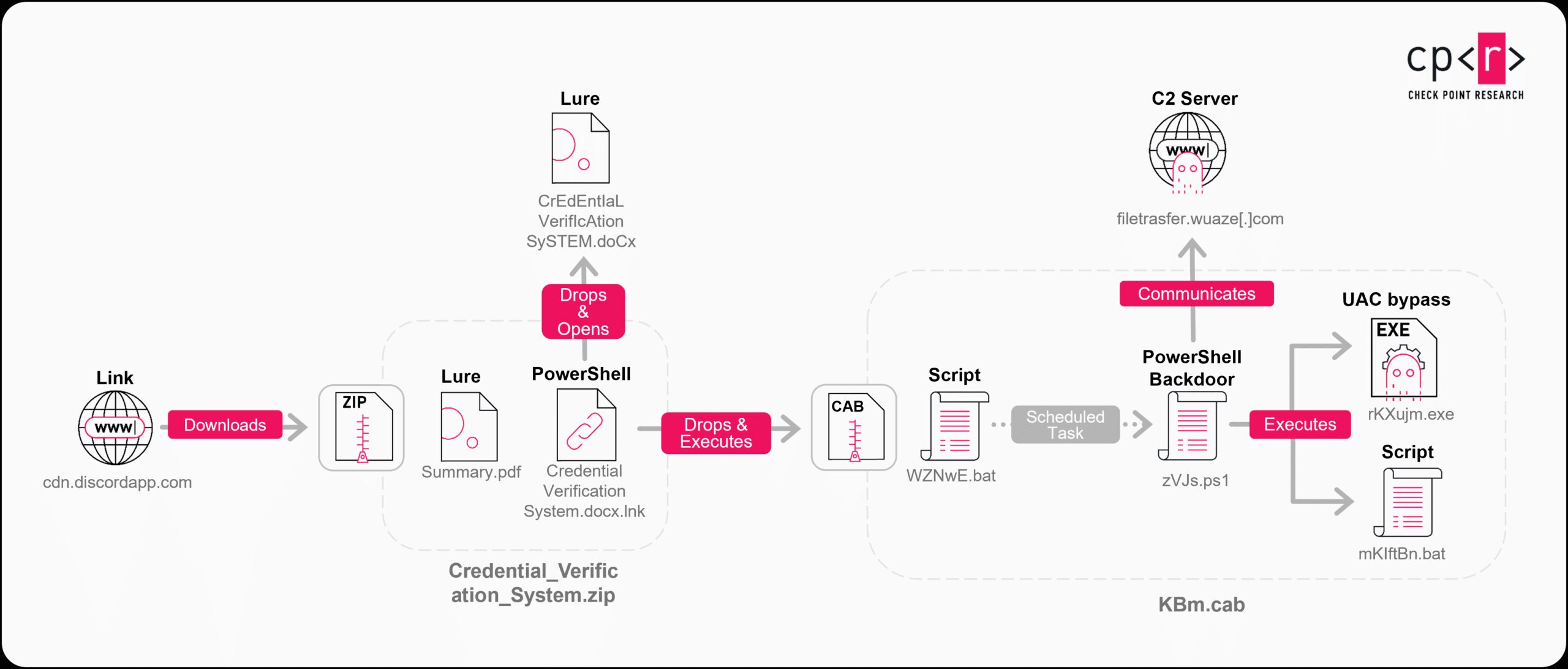
From there, batch files unpacked from the CAB archive move the backdoor into a hidden ProgramData folder and create a scheduled task that mimics a OneDrive startup entry.
This task runs every hour, decrypts the PowerShell payload from disk using a simple XOR key, and executes it directly in memory, keeping the core malware file‑less during runtime and making incident response far more difficult.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.