Nike Allegedly Hacked by WorldLeaks Ransomware Group
Athletic footwear and apparel manufacturer Nike has become the latest victim of WorldLeaks, a ransomware group specializing in financially motivated data extortion. The group announced the breach on...
Athletic footwear and apparel manufacturer Nike has become the latest victim of WorldLeaks, a ransomware group specializing in financially motivated data extortion.
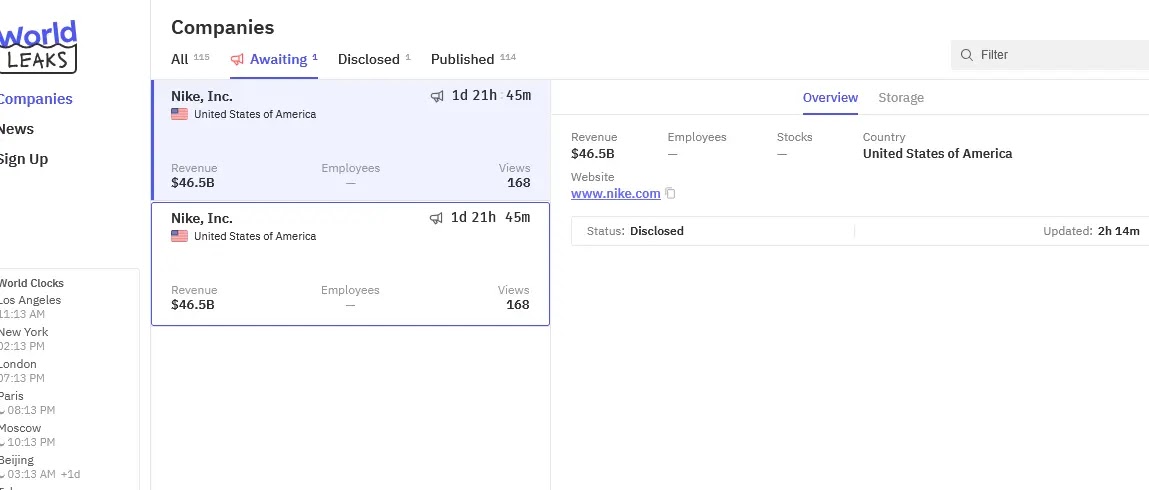
The group announced the breach on its darknet leak site on January 22, claiming responsibility for the incident and threatening to release stolen data on January 25, 2026, at 6 PM GMT.
WorldLeaks listed Nike as a victim on its leak platform with minimal accompanying details. However, the post reportedly received over 400 views within hours of publication.
According to a post on forums, the attack was discovered on January 22, 2026, with data exfiltration occurring on the same date.
Nike confirmed its awareness of the alleged incident in an official statement: “We are investigating a potential cybersecurity incident and are actively assessing the situation.”
The exact volume of exfiltrated data remains unconfirmed. However, industry analysts suggest it could potentially reach several terabytes based on WikiLeaks‘ historical attack patterns.
Nike reported approximately 481,183 compromised users, 220 compromised employees, and 444 third-party employee credentials exposed in the incident.
Available evidence suggests that multiple data categories may have been compromised during the attack.
Including internal company documentation, customer information, employee email addresses and phone numbers, business operational records, and human resources data.
The specific nature and scope of sensitive information exposed, including potential intellectual property, product development details, or financial records, remain undisclosed pending Nike’s ongoing investigation.
WorldLeaks Profile
WorldLeaks emerged as a strategic rebrand of Hunters International in January 2025, following the predecessor group’s cessation of operations.
The group operates using an extortion-only model, focusing exclusively on data theft rather than file encryption, enabling faster attack execution and reduced detection risk.
The group maintains a sophisticated four-platform infrastructure: a public leak site for victim showcase, a negotiation portal for ransom communications.
An “Insider” journalist platform providing 24-hour advance data access and an affiliate management system.
WorldLeaks has claimed over 116 victims since its formation, including high-profile targets such as Dell Technologies (1.3TB stolen) and L3Harris Technologies, a US defense contractor.
Intelligence reports indicate WikiLeaks typically gains initial access through compromised legitimate websites, phishing campaigns with malicious attachments, unpatched internet-exposed applications, or VPNs lacking multi-factor authentication.
Post-compromise, the group leverages credential theft, lateral movement through network shares, and custom-developed exfiltration tooling to catalog and extract sensitive data.
This incident marks the continuation of coordinated cyberattacks targeting the retail and athletic apparel sectors in recent months.
Security researchers note the pattern suggests deliberate targeting of high-value organizations with weak authentication infrastructure and significant intellectual property holdings.
Organizations should implement mandatory multi-factor authentication on all remote access points and conduct immediate network segmentation reviews.
Establish enhanced monitoring for unauthorized data exfiltration to external cloud services and anonymized networks.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.