New RDP Alert After April 2026 Security Update Warns of Unknown
The April 2026 Patch Tuesday security update has brought a significant behavioral change to Microsoft’s Windows Remote Desktop Connection application (MSTSC), introducing new warning dialogs to...
The April 2026 Patch Tuesday security update has brought a significant behavioral change to Microsoft’s Windows Remote Desktop Connection application (MSTSC), introducing new warning dialogs to safeguard users against phishing attacks exploiting Remote Desktop Protocol (.rdp) files.
Remote Desktop (.rdp) files have increasingly been weaponized by threat actors to trick users into establishing connections that silently redirect sessions to attacker-controlled infrastructure.
One of the most notable campaigns involved Midnight Blizzard, a Russian state-sponsored threat group that distributed malicious RDP files as email attachments in large-scale spear-phishing operations.
These files appeared routine but quietly requested access to local resources, including drives, clipboards, and credential material, before the victim realized anything had gone wrong.
The United Kingdom’s National Cyber Security Center (NCSC) formally reported the issue to Microsoft as a spoofing vulnerability in Remote Desktop, prompting the remediation now shipping in the April 2026 update.
Microsoft’s April 14, 2026, Patch Tuesday update (KB5083769 for Windows 11 builds 26200.8246 and 26100.8246) introduces two distinct dialog experiences when a user opens an .rdp file.
First-time education dialog (one-time per account): The first time a user opens an .rdp file after the update, Windows displays an informational prompt that explains what RDP files are and why they can be dangerous.
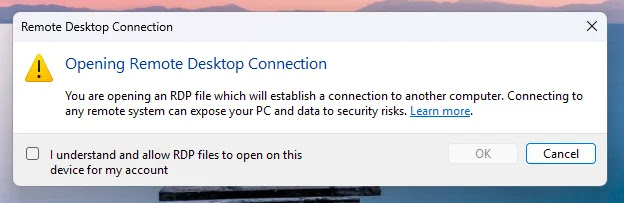
Once the user acknowledges and allows RDP file connections, this dialog does not reappear for that account unless Microsoft updates the dialog version in the future.
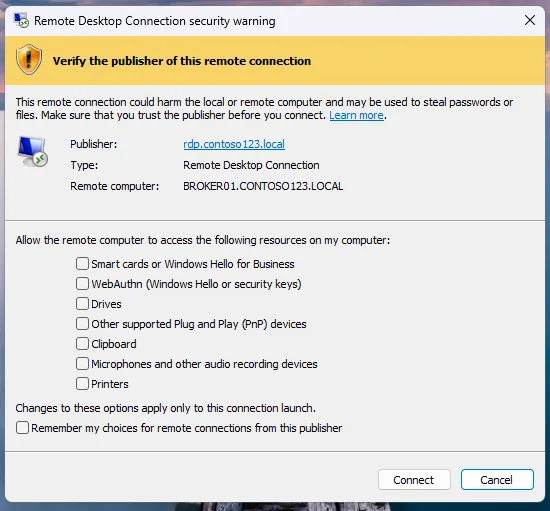
Per-connection security dialog (shown every time): Each subsequent time an RDP file is opened, a security warning dialog appears before any connection is established.
This dialog surfaces the remote computer’s address, indicates whether the file is digitally signed by a verified publisher, and lists all local resource redirections the file requests, such as drives, clipboards, printers, smart cards, and WebAuthn credentials. Critically, every resource redirect option is disabled (OFF) by default, requiring users to explicitly check and approve each item before connecting.
When an .rdp file is not digitally signed or when the publisher cannot be verified, the security dialog now prominently displays a “Caution: Unknown remote connection” banner with an orange warning highlight.
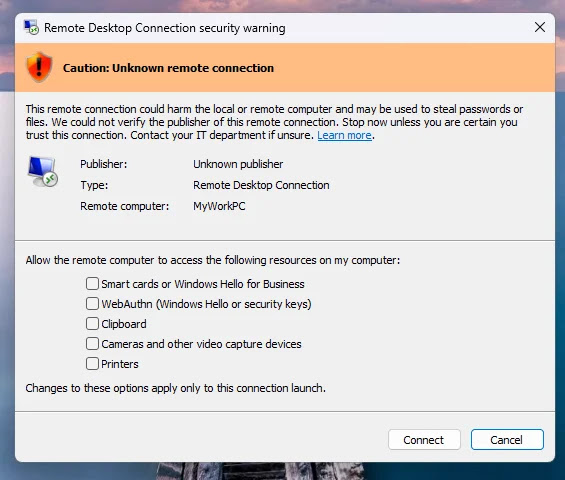
The publisher field shows “Unknown publisher,” flagging this as the highest-risk scenario for tampering or phishing. This is the precise attack surface that threat actors exploit: distributing unsigned RDP files that users open without scrutinizing the embedded connection parameters.
The overarching design philosophy behind this update is secure by default. Previously, users received no warning whatsoever when opening an RDP file, making it trivially easy for malicious files to request broad local access silently.
With the April 2026 update, unsafe resource sharing becomes an exception that requires active user consent, not an inherited default from the file itself.
Administrators who need to temporarily revert to legacy dialog behavior can do so by modifying the RedirectionWarningDialogVersion registry value under HKLMSoftwarePoliciesMicrosoftWindows NTTerminal ServicesClient and setting it to 1, though this is not recommended as a long-term solution.
Organizations are also advised to review their RDP file distribution practices and standardize the use of signed connection files to reduce the risk of “trusted attachment” abuse.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.