Hackers Use MiningDropper to Deliver Infostealers, RATs, and
A rapidly expanding The campaign reaches victims through phishing pages, social media links, and fraudulent websites that mimic trusted services, including transport portals, banks, telecom brands,...
The campaign reaches victims through phishing pages, social media links, and fraudulent websites that mimic trusted services, including transport portals, banks, telecom brands, and popular mobile applications.
That broad lure strategy gives attackers many ways to trick users into downloading malicious APK files before the hidden payload chain begins.
Cyble researchers said they observed a notable surge in MiningDropper activity and linked the malware to multiple campaigns now operating across India, Europe, Latin America, and Asia.
One cluster focused on Indian users with infostealer lures, while another delivered BTMOB RAT to wider regional targets through fake app download pages.
The impact is serious because MiningDropper is not just a single malicious app but a reusable framework that lets threat actors swap final payloads as needed.
Cyble’s telemetry found more than 1,500 samples in the wild over the past month, and many showed very low antivirus detection.
Infection mechanism
What makes the operation harder to stop is its layered design, which mixes native code, encrypted assets, dynamic DEX loading, and anti emulation checks to delay analysis.
Instead of exposing the final malware at once, each stage unlocks the next one only after earlier checks pass, reducing what static scanners can immediately see.
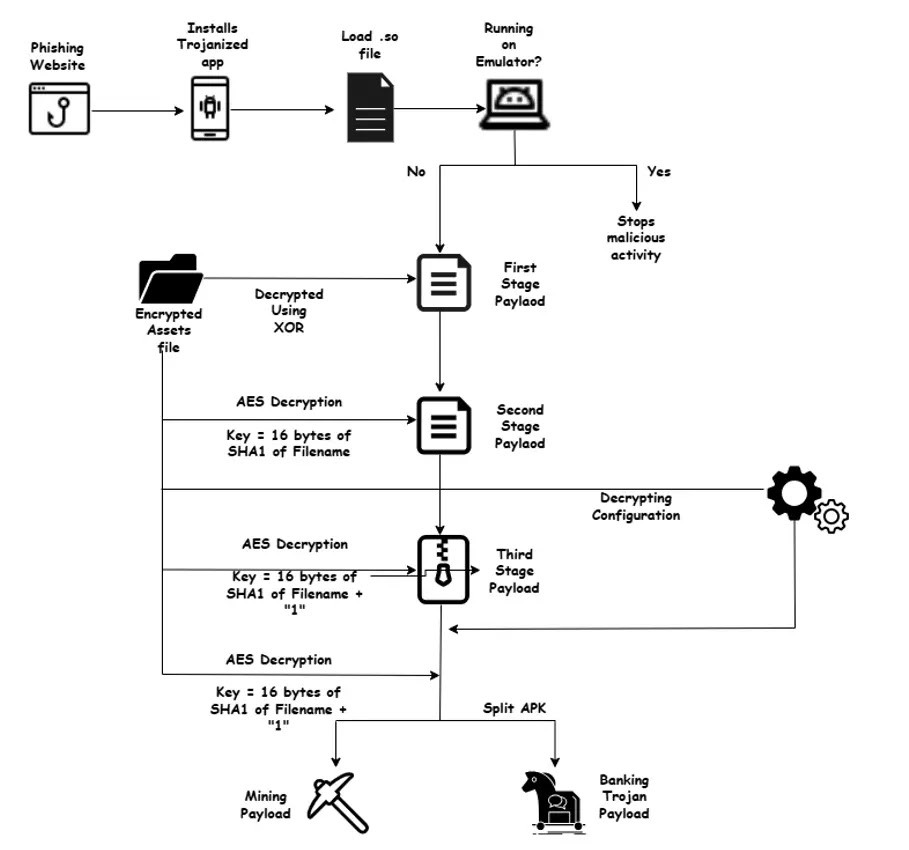
The chain starts with a trojanized version of the open source Android project LumoLight, where malicious actions are launched through the native library librequisitionerastomous.so.
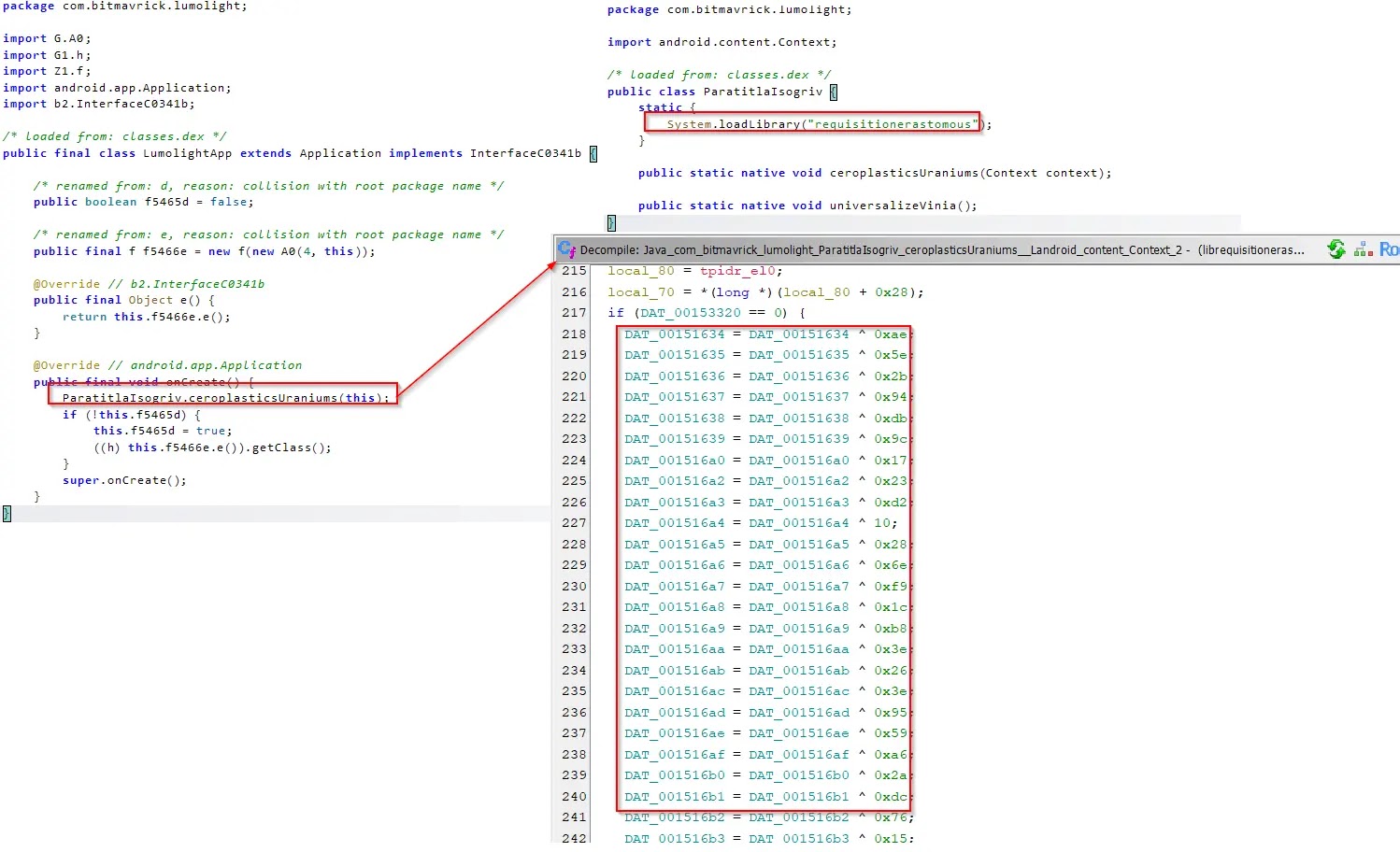
Inside that library, strings are hidden with XOR obfuscation and decrypted only at runtime, making the code harder to inspect and easier to keep below detection thresholds.
The same native component also checks platform details, system architecture, and device model information to decide whether it is running inside an emulator or rooted environment.
If the environment looks suspicious from the attacker’s view, the malware can stop its harmful activity, which helps it avoid sandboxes and automated analysis systems.
When those checks pass, the library decrypts an asset named x7bozjy2pg4ckfhn with a hardcoded XOR key, produces the first stage DEX payload, and loads it with DexClassLoader for further execution.
That first stage then decrypts a second stage file with AES, using key material derived from the filename, a choice that hides the key logic and complicates reverse engineering.
The second stage is the part most victims would notice because it can display a fake Google Play update screen, illustrated in Figure 10 Fake Google Play Update activity, to make the infection look routine.
Behind that screen, it decrypts more files, reads configuration data, and decides whether to activate a miner path or a user defined payload path for later installation.
In the user payload branch, the malware decrypts a ZIP archive and split components, rebuilds the final package, and installs a more capable threat such as BTMOB RAT through the third stage installer.
Cyble said that final payload can steal credentials through WebView injections, log keystrokes, exfiltrate data, abuse Accessibility Services, and support real time remote control, screen monitoring, file handling, audio recording, and command execution.
For defenders, the case shows how Android threats are moving toward reusable malware frameworks that separate delivery, deception, and monetization, allowing one campaign to shift quickly between banking theft, espionage style access, and silent mining without rebuilding the whole toolset.
Users can reduce risk by installing apps only from trusted stores, avoiding links received by SMS, email, or social media, checking permissions before install, keeping Android updated, using MFA for banking apps, and reporting suspicious financial activity quickly if compromise is suspected.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.