New Malware Toolkit Redirects to Malicious Sites, Sends Users
Browser attacks have grown considerably more dangerous and organized. A new threat called Stanley, uncovered in January 2026, highlights the severity of this evolving landscape. This...
Browser attacks have grown considerably more dangerous and organized. A new threat called Stanley, uncovered in January 2026, highlights the severity of this evolving landscape.
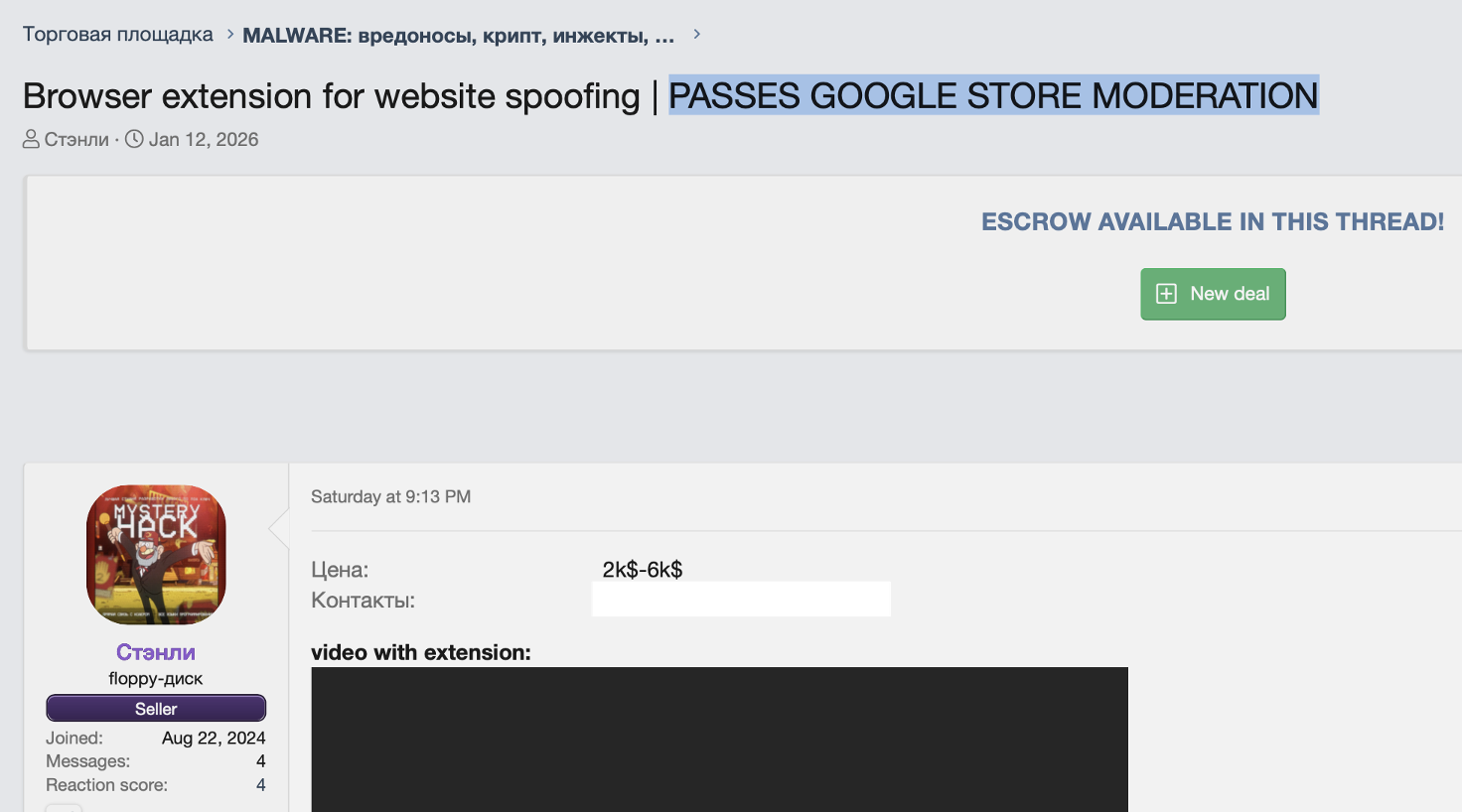
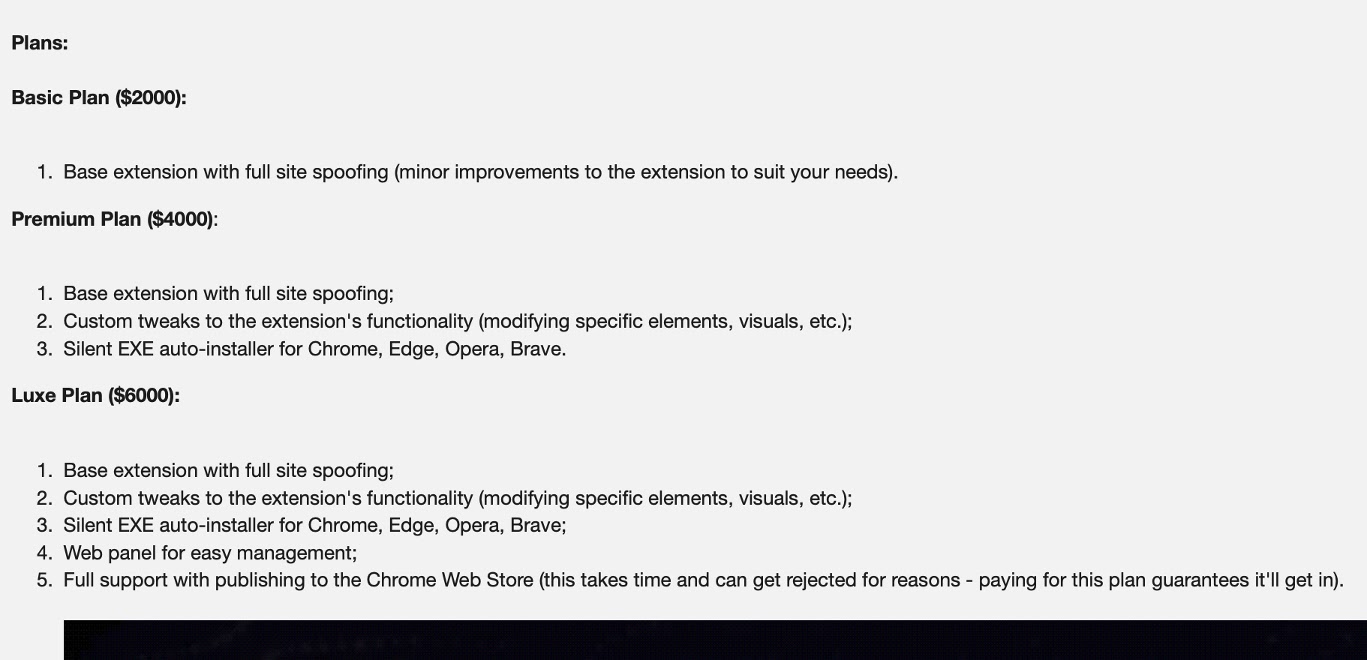
This malware-as-a-service toolkit, priced between $2,000 and $6,000, does something particularly deceptive: it displays fake websites to users while the URL bar keeps showing the legitimate address.
It’s designed to steal login credentials and financial information by tricking people into thinking they’re visiting real websites.
Stanley first appeared on January 12, 2026, on Russian-language cybercrime forums under the seller’s alias “Стэнли.”
What makes this toolkit especially concerning is that the seller promises guaranteed publication on the Chrome Web Store, meaning the malicious extension can be downloaded directly from Google’s official store.
The toolkit disguises itself as “Notely,” a notes and bookmarks application, giving it legitimate cover while performing website spoofing attacks.
Varonis researchers noted and identified the toolkit after analyzing its technical capabilities and distribution methods.
The security team discovered that Stanley functions through a web-based control panel where attackers select individual victims and configure website hijacking rules.
Once a target is chosen, operators set up a source URL (the legitimate site to hijack) and a target URL (the attacker’s phishing page).
The extension then intercepts when the victim visits the real website and overlays a full-screen iframe containing the fake version, all while the browser’s address bar displays the legitimate domain.
How Stanley Infects and Controls Victims
The infection mechanism relies on browser extension permissions that grant near-complete control over user browsing activity.
Once installed, Stanley’s code runs at the earliest possible moment during page loading, before any legitimate content appears.
The extension uses the victim’s IP address as a unique identifier, enabling attackers to target specific people and even correlate users across multiple browsers and devices.
Every ten seconds, the extension communicates with the attacker’s command and control server to receive updated hijacking instructions.
Stanley implements backup domain rotation to ensure survival even when authorities take down the primary server.
This means the extension automatically cycles through fallback domains to maintain operational control.
The toolkit has already compromised thousands of users, with the command and control panel displaying victim IP addresses, online status, and last activity timestamps.
Enterprises should consider strict extension allowlisting policies, while individual users need to reduce their installed extensions and scrutinize permission requests carefully.
The deeper problem remains that browser extension marketplaces approve extensions once and allow updates anytime, meaning malicious updates can slip through after initial review.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.