Lazarus Hackers Target European Drone Manufacturers Now
The sophisticated North Korean-aligned hacking group Lazarus, also known as HIDDEN COBRA, has initiated a new wave of targeted attacks against European drone manufacturers and defense contractors....
The sophisticated North Korean-aligned hacking group Lazarus, also known as HIDDEN COBRA, has initiated a new wave of targeted attacks against European drone manufacturers and defense contractors.
The campaign, tracked as Operation DreamJob, emerged in late March 2025 and specifically targets organizations developing unmanned aerial vehicle technology across Central and Southeastern Europe.
Researchers have identified this activity as part of a broader strategic effort by North Korea to accelerate its domestic drone program, particularly following increased investment in modern warfare capabilities observed in the Russia-Ukraine conflict.
The campaign represents a significant escalation in cyberespionage tactics aimed at stealing proprietary manufacturing information and intellectual property from the aerospace and defense sectors.
Three European companies have been confirmed as targets, with at least two heavily involved in designing advanced single-rotor drones and producing critical UAV components currently deployed in active conflict zones.
The timing of these attacks coincides with North Korea’s reported efforts to mass-produce combat and reconnaissance drones similar to Western models like the MQ-9 Reaper and RQ-4 Global Hawk.
Welivesecurity analysts and researchers noted that the malware infrastructure used in these attacks employs sophisticated delivery mechanisms designed to evade traditional security defenses.
The attack begins with social engineering, specifically using fake job offers for prestigious positions to trick employees into downloading trojanized documents.
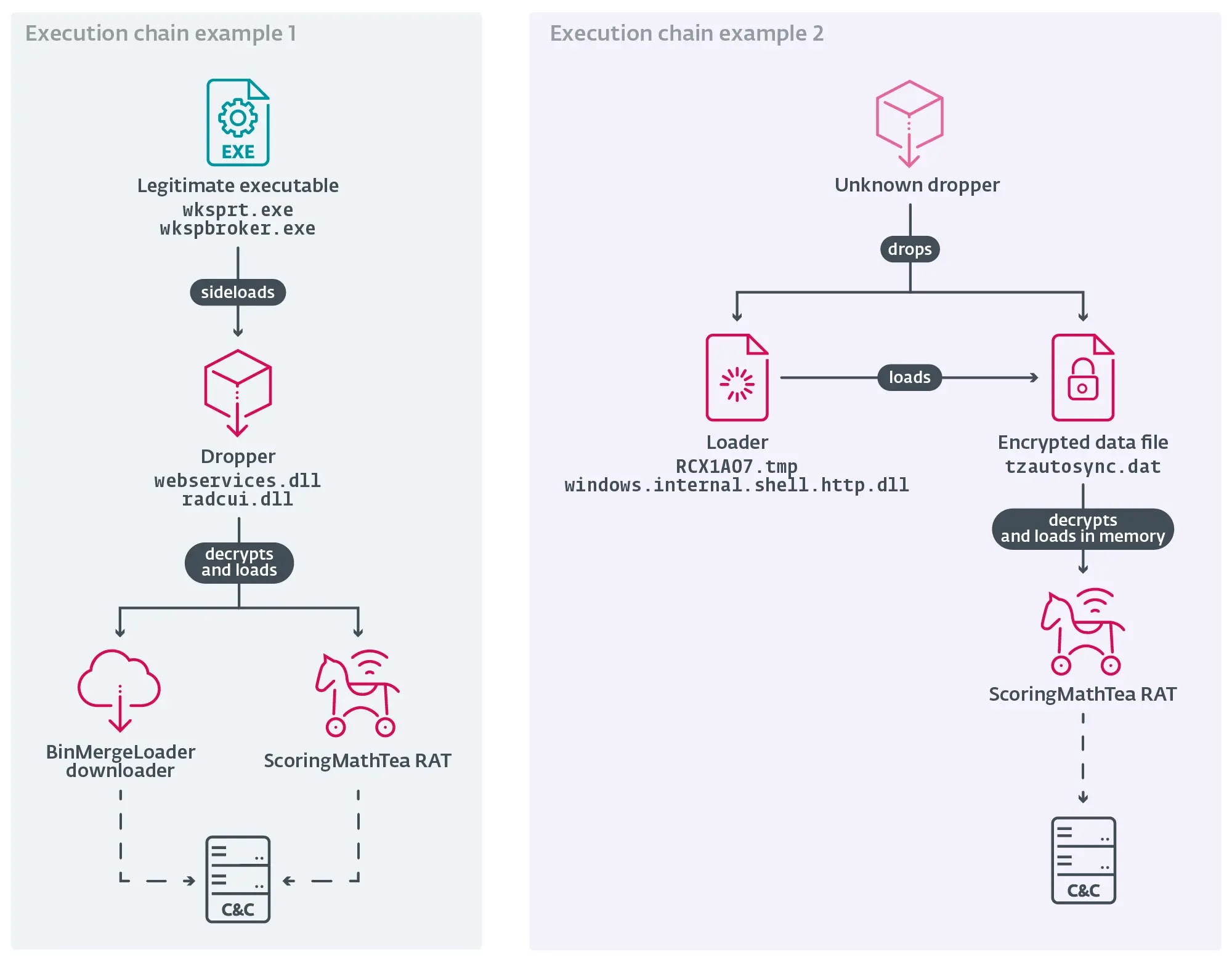
Once executed, the malware deploys a chain of specialized tools designed to maintain persistent access and avoid detection on compromised systems.
Infection mechanism
The primary infection mechanism relies on DLL side-loading, a technique where legitimate Windows applications are exploited to load malicious libraries without triggering security alerts.
The attackers have incorporated their malware into trojanized versions of popular open-source software, including TightVNC Viewer, MuPDF reader, and WinMerge plugins.
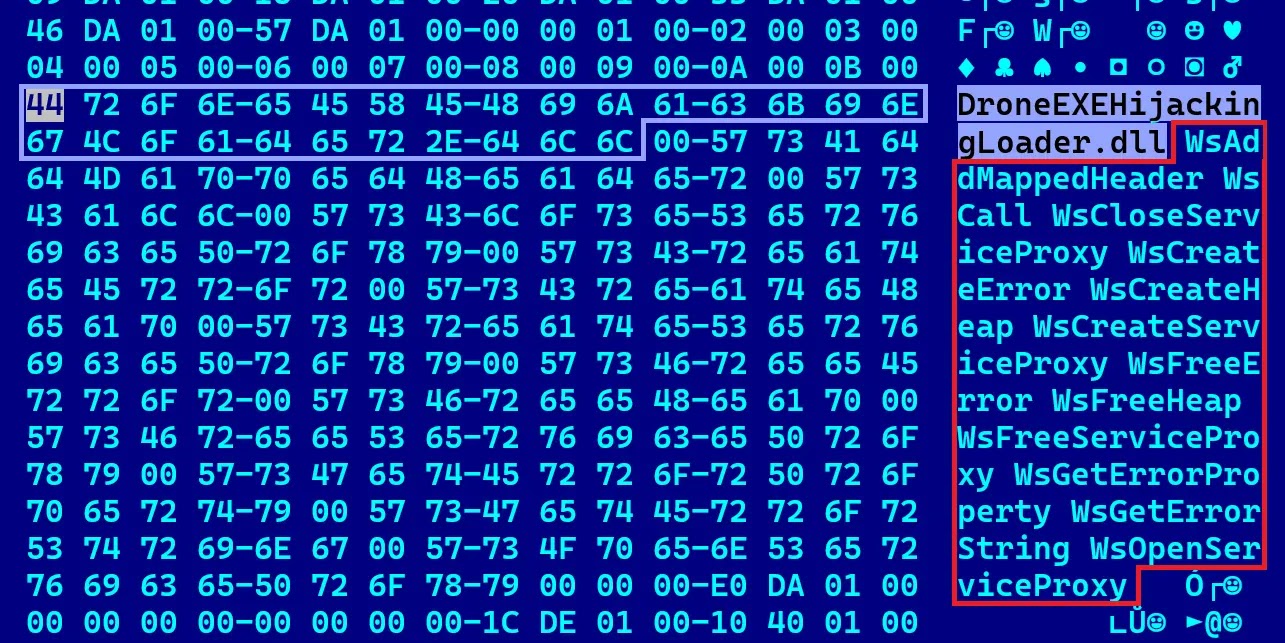
One particularly revealing dropper contained the internal filename DroneEXEHijackingLoader.dll, directly referencing the attackers’ campaign focus on drone technology.
The main payload deployed across all incidents is ScoringMathTea, a remote access trojan that provides attackers complete control over compromised machines.
This sophisticated malware offers approximately 40 different commands for system manipulation, file exfiltration, and further payload deployment.
What makes ScoringMathTea particularly dangerous is its ability to remain completely encrypted on disk, only decrypting in memory during execution, making traditional file-based detection nearly impossible without advanced behavioral monitoring.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.