MuddyWater Uses Russian MaaS in New ChainShell Campaign
Iranian state-backed hacking group MuddyWater has pivoted its operations, now leveraging a Russian-built Malware-as-a-Service (MaaS) platform. This significant change powers a new campaign directed...
Iranian state-backed hacking group MuddyWater has pivoted its operations, now leveraging a Russian-built Malware-as-a-Service (MaaS) platform. This significant change powers a new campaign directed against Israeli targets.
The operation, built around a previously unknown tool called ChainShell, marks a clear departure from the group’s earlier reliance on custom-developed tools, and raises fresh concerns for organisations in critical sectors worldwide.
MuddyWater — also known as Seedworm, Mango Sandstorm, TA450, and Static Kitten — operates under Iran’s Ministry of Intelligence and Security (MOIS).
Active since at least 2017, the group has targeted government agencies, defence organizations, telecommunications firms, and energy companies across the Middle East and parts of the West, including the United States and United Kingdom.
Where earlier campaigns leaned on PowerShell backdoors and legitimate remote monitoring tools to carry out espionage, this campaign shows MuddyWater now purchasing ready-made offensive capabilities from a criminal marketplace.
The platform behind these capabilities belongs to TAG-150, a Russian-speaking cybercriminal group running a modular, multi-tenant service called CastleRAT.
Analysts at JumpSEC traced the link to this Russian platform through a misconfigured C2 server, 15 malware samples, and a novel Windows executable payload.
On the exposed server at IP address 157.20.182.49, researchers found Farsi-language code comments alongside Israeli IP range lists — clear evidence of Iranian operators targeting Israeli systems.
The timeline of activity reveals just how persistent this campaign has been. In early March 2026, researchers at Ctrl-Alt-Intel first identified the exposed server.
Rather than pulling back, MuddyWater pushed forward — new delivery installers were compiled on March 11th, updated JavaScript malware appeared on March 16th, and a fresh macro-based lure was spotted contacting MuddyWater infrastructure on March 20th, confirming the group remained active well past the point of detection.
The broader impact of this shift is serious. Organisations in the defence, aerospace, energy, and government sectors now face a threat that combines state-level targeting with commercially developed offensive tools.
By adopting CastleRAT and ChainShell, MuddyWater has gained capabilities it previously lacked — including hidden VNC sessions that let attackers control a machine invisibly, Chrome cookie decryption, and a blockchain-resistant communication channel that resists traditional takedown efforts.
ChainShell’s Infection Mechanism and Evasion Design
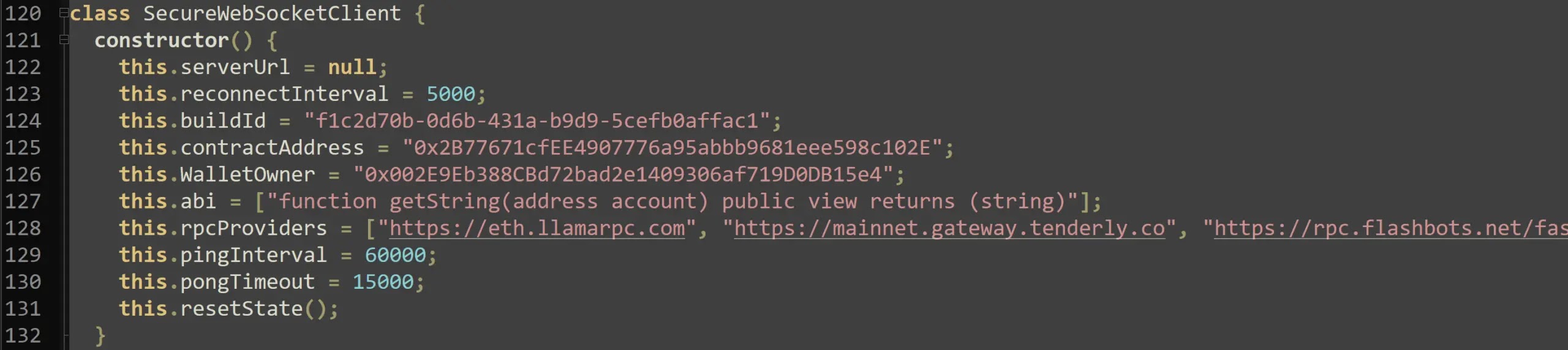
The most technically distinct element of this campaign is ChainShell, a Node.js-based agent that resolves its command-and-control address directly from an Ethereum smart contract via 10 RPC providers.
Unlike conventional malware that relies on fixed domains or IP addresses, ChainShell’s C2 location lives on the blockchain, making sinkholing or IP blocking largely ineffective against it.
ChainShell arrives on a victim’s machine through reset.ps1, a PowerShell deployer found on the MuddyWater-attributed C2 server.
The script installs Node.js, AES-decrypts an embedded payload, and drops two files: sysuu2etiprun.js, the blockchain C2 agent, and VfZUSQi6oerKau.js, a dropper and installer component
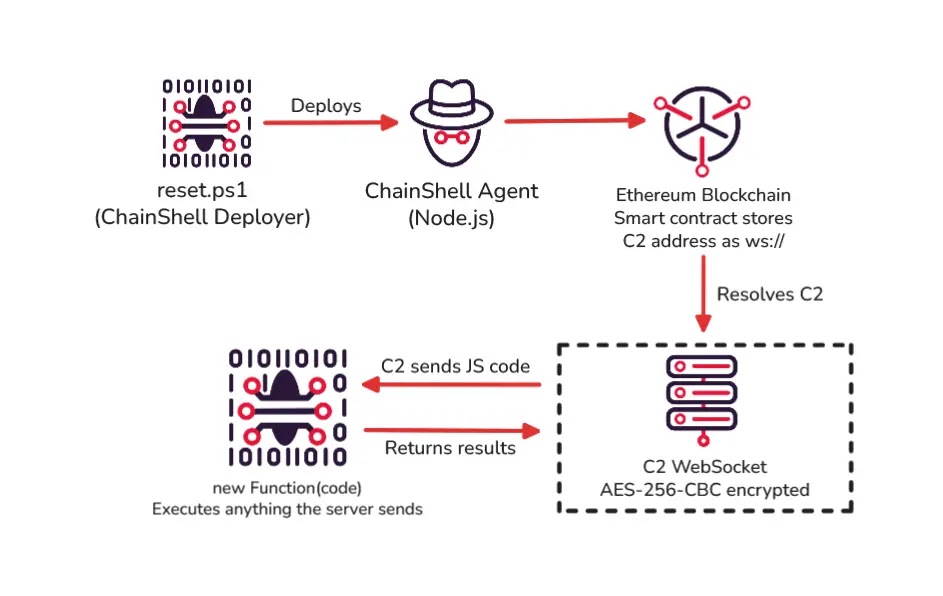
Once running, the agent communicates with the C2 through AES-256-CBC encrypted WebSocket messages, sending and receiving JavaScript that it executes locally through a new Function() call.
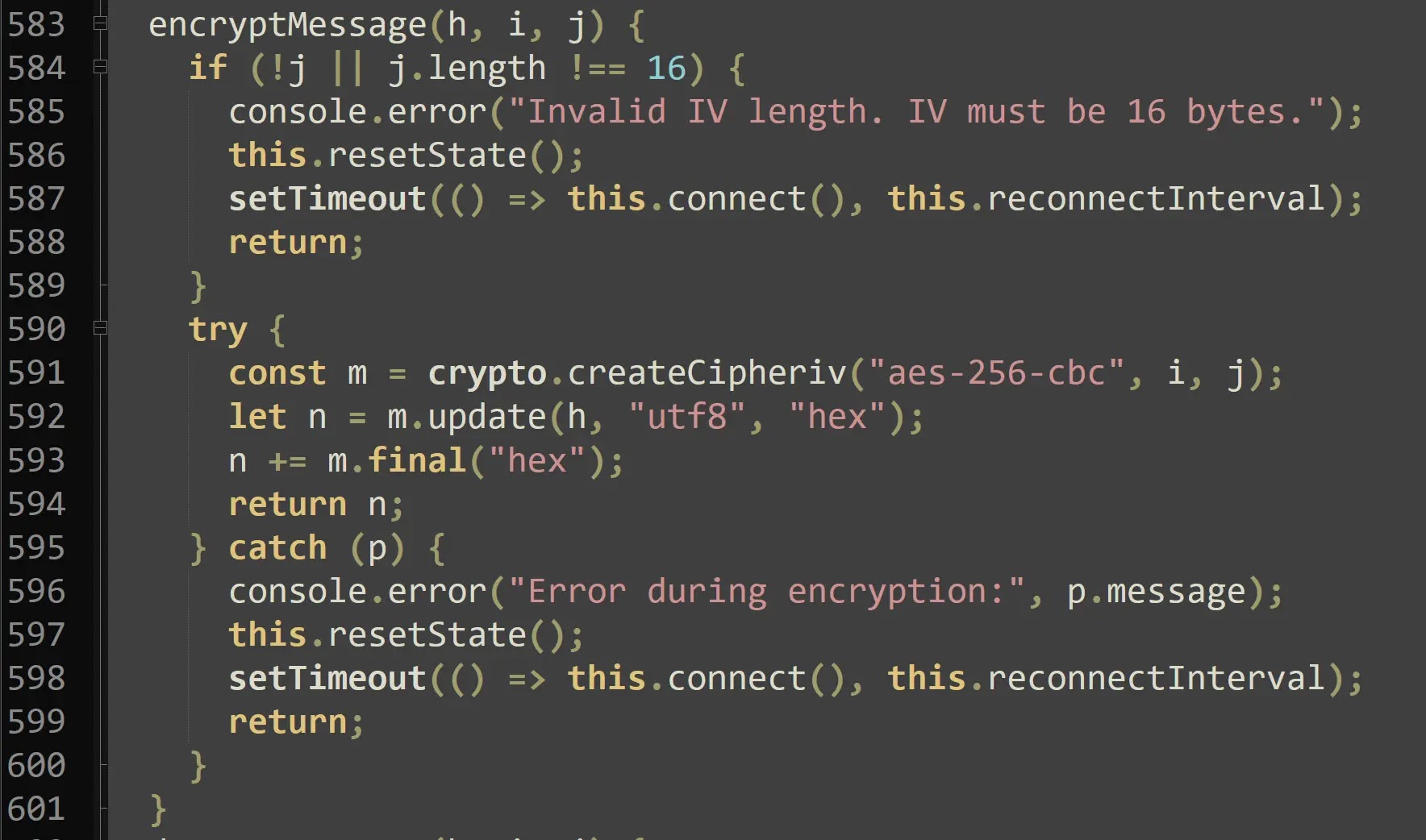
What makes ChainShell hard to detect is its thin shell design — the agent carries no built-in stealer, keylogger, or shell. All active capabilities are delivered from the server at runtime, so static analysis of the file reveals little about what it can actually do.
The agent also performs a locale check on startup and exits immediately on CIS country systems such as Russia and Ukraine, a developer safeguard researchers assess as genuine rather than a false flag.
Organisations exposed to this campaign should monitor for scheduled tasks matching the naming pattern Virtual{Campaign}Guy{N}, check for unexpected Node.js installations under %LOCALAPPDATA%Nodejs, and apply blocks on all documented network IOCs.
Security teams should also avoid defaulting to Russian cybercrime attribution when CastleRAT or ChainShell artefacts surface — further analysis of campaign configurations and C2 infrastructure may instead point to Iranian state-level operators.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.