Hackers Abuse GitHub & GitLab for Malware & Ph Host Credential
Cybercriminals are exploiting GitHub and GitLab, two of the world’s most trusted developer platforms, to spread malware and steal login credentials from unsuspecting users. Since organizations...
Cybercriminals are exploiting GitHub and GitLab, two of the world’s most trusted developer platforms, to spread malware and steal login credentials from unsuspecting users.
Since organizations rely on these platforms daily, most security tools do not block their domains, giving attackers a clear path directly into corporate inboxes.
GitHub and GitLab sit at the core of modern software development. Developers use them to store, share, and manage code for projects of all sizes.
Since blocking these domains would disrupt business operations, most corporate security tools extend them a level of trust that threat actors have learned to exploit.
By uploading malicious files or fake login pages to public repositories, attackers generate links that look no different from legitimate developer content — helping phishing emails slip past secure email gateways (SEGs) without raising alerts.
The abuse of Git repository websites has grown every year since 2021. The year 2025 alone accounted for 45% of the total campaign volume recorded across the full period, showing how rapidly this attack method is scaling.
Researchers at Cofense Intelligence identified these trends while tracking phishing campaigns, noting that threat actors are no longer limiting themselves to a single objective — they are increasingly combining malware delivery and credential phishing in a single attack.
Of all the campaigns studied, 95% abused GitHub, while the remaining 5% targeted GitLab.
In terms of intent, 58% of campaigns focused on credential theft while 42% delivered malware. Most concerning is the rise of dual-threat attacks.
In one documented case tracked under ATR 383659, victims who opened what appeared to be a PDF reader unknowingly installed Muck Stealer, while a fraudulent DocuSign page simultaneously opened to steal account credentials.
The consequences extend well beyond individual users. Organizations across all industries face serious risks of data theft, unauthorized account access, and potential network-wide compromise — all triggered by a single click on what appears to be a routine, trusted GitHub or GitLab link.
How Attackers Deliver Their Payloads
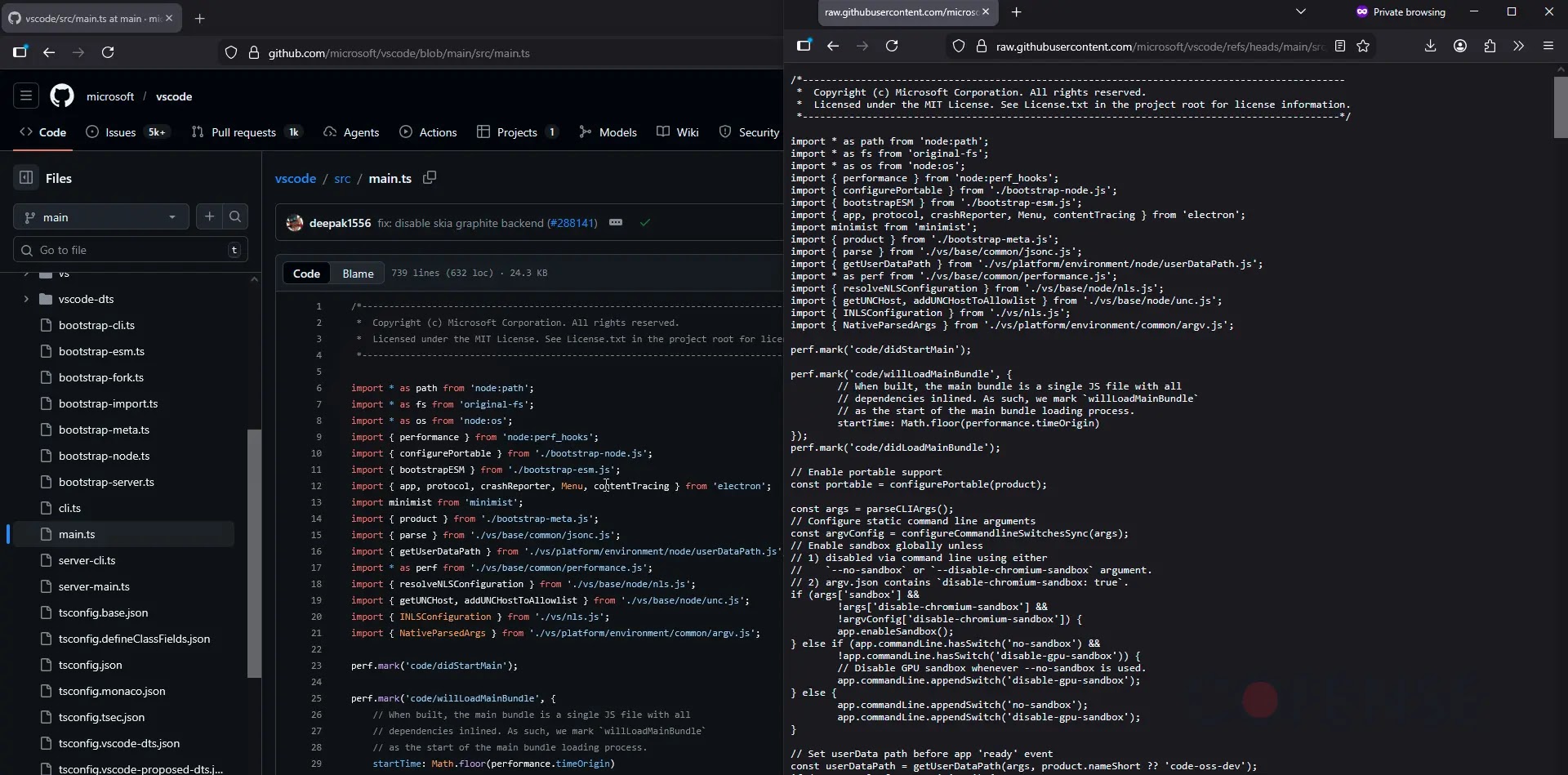
When threat actors abuse github.com or githubusercontent.com, they host malware directly inside repositories or attach malicious files to comments on legitimate projects.
Since github.com download links often redirect through raw.githubusercontent.com for direct file retrieval, malware can be fetched silently in the background without any visible user interaction.
This silent delivery method is commonly used to drop Remote Access Trojans (RATs) such as Remcos RAT, which leads all malware delivered via Git platforms at 21% of volume, followed by Byakugan at 9%, AsyncRAT at 7%, and DcRAT in fourth place.
To slip past antivirus scanning, threat actors routinely package their malware inside password-protected .zip or .7z archive files.
Since only the email recipient has the password — included in the phishing message — automated scanning by GitHub or GitLab cannot access or inspect the contents.
In a more advanced example documented in ATR 404322, attackers used GitLab combined with browser user agent detection to tailor the attack to each victim.
If the target was accessing the link from a Windows device, a GoTo RAT was delivered; if not, they were sent to a credential phishing page instead, ensuring the attack produced results regardless of the target’s device.
Users and security teams should treat any GitHub or GitLab link received in an unexpected email with caution, even if the domain looks legitimate.
Organizations should enforce multi-factor authentication (MFA) on all accounts to limit the impact of stolen credentials. Employees should avoid opening password-protected archive files sent via email.
Security teams are also advised to apply behavioral-based email analysis rather than trusting domain reputation alone, and to regularly conduct phishing simulation training to improve end-user awareness.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.