MuddyWater Hackers Scan Systems, Hit MuddyWater-Style Before
A sophisticated cyber campaign, exhibiting strong operational similarities to the notorious MuddyWater threat group, has been identified conducting extensive reconnaissance. Threat actors behind this...
A sophisticated cyber campaign, exhibiting strong operational similarities to the notorious MuddyWater threat group, has been identified conducting extensive reconnaissance. Threat actors behind this operation
The attack unfolded through a structured, multi-stage process rather than a single opportunistic breach. Attackers began with wide-scale vulnerability reconnaissance and then pivoted to selective credential harvesting before ultimately reaching full data exfiltration.
To carry out the initial scanning phase, the threat actor weaponized at least five newly disclosed CVEs targeting a broad range of systems — from web applications and email servers to IT management platforms and workflow automation tools.
The five exploited vulnerabilities include CVE-2025-54068 (Laravel Livewire RCE), CVE-2025-52691 (SmarterMail RCE), CVE-2025-68613 (n8n RCE), CVE-2025-9316 (Unauthenticated Session ID Generation in RMM systems), and CVE-2025-34291 (Langflow RCE).
Oasis Security researchers identified and analyzed this campaign in detail, tracing attacker-controlled infrastructure back to a server located in the Netherlands with the IP address 157.20.182.49.
Analysts collected a large volume of server-side files from that infrastructure, uncovering modular C2 components, operational scripts, and evidence of coordinated scanning activity.
The timing of the campaign, beginning just weeks before heightened regional tensions, raises clear concerns about the strategic intent driving the operation.
With reconnaissance complete, the threat actor shifted focus toward credential-based intrusion. Attackers launched Outlook Web Access (OWA) brute-force attacks using custom tools including owa.py and multi-threaded attack software like Patator, running targeted username enumeration against specific organizations.
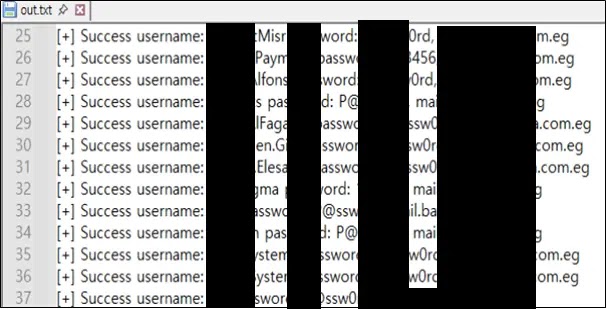
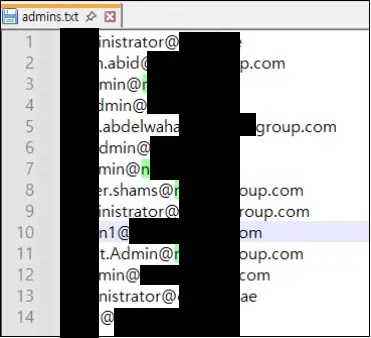
These efforts were concentrated on entities in Egypt, Israel, and the United Arab Emirates. In one confirmed case, an Egyptian firefighting enterprise had its employee credentials successfully stolen, while administrator account lists were also recovered from a targeted organization in the UAE.
The operation moved beyond access attempts into confirmed data exfiltration, specifically from an aviation organization based in Egypt.
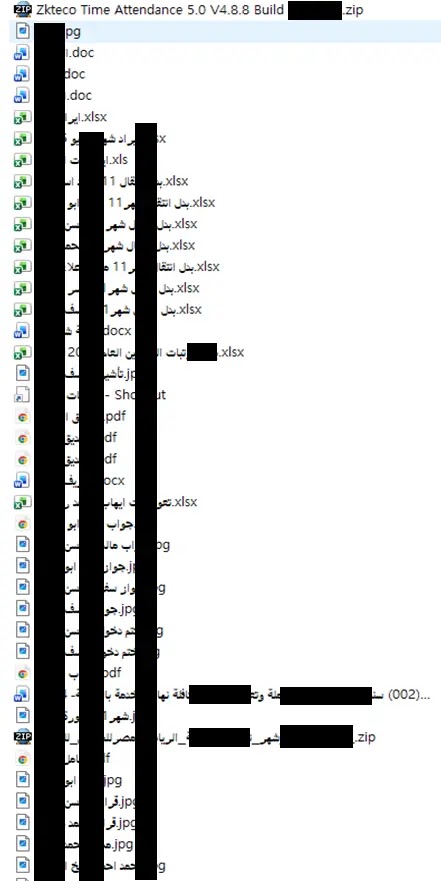
Roughly 200 staged files were discovered in attacker-controlled directories, containing passport and visa records, payroll and salary data, credit card details, and internal corporate documents.
Additional targeting was identified across entities in Portugal and India, indicating the campaign’s reach extended well beyond the Middle East.
Modular C2 Infrastructure Built for Resilient Control
Among the most technically significant discoveries in this campaign was the Command and Control (C2) architecture the attackers deployed to manage their compromised systems.
Oasis Security’s analysis revealed a multi-layered infrastructure built across different programming languages and communication protocols, deliberately designed to remain functional, adaptable, and difficult to disrupt even if parts of it were discovered by defenders.
![TCP-based C2 controller 'tcp_serv[.]py' using a custom BIIH header structure (Source - Oasis)](https://hackersradar.com/wp-content/uploads/2026/04/content_1776259856_1210.jpg)
The C2 setup included Python-based controllers — tcp_serv.py and udp_3.0.py — alongside Go-based binaries including server and client.exe.
The tcp_serv.py controller was configured to listen and accept inbound connections over TCP port 5009, while the UDP controller followed nearly identical structural patterns.
Both controllers used a distinct custom packet header format known as <BIIH, which appeared consistently across all controller variants identified in attacker-controlled directories.
More advanced HTTP-based controllers were also found, managing encrypted client sessions through API-style endpoints such as /command, /result, /signup, and /feed.
The Go-based ex-server binary handled AES (CTR mode)-encrypted data exchanges via the /signup and /feed endpoints, with cookie-based cid values used to identify and track individual infected hosts.
These communication patterns closely align with MuddyWater’s ArenaC2 framework, reinforcing the attribution assessment made by Oasis Security.
Organizations exposed to any of the five exploited CVEs should apply available patches without delay and review OWA access logs for signs of brute-force activity.
Security teams are advised to block outbound traffic on port 5009, monitor for encrypted HTTP connections to unrecognized endpoints, and audit internal file directories for bulk staging behaviors that may indicate active data collection ahead of exfiltration.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.