Microsoft Suspends Dev Accounts of High-Profile Developer Open-Source
Microsoft has suspended the Windows Hardware Program developer accounts for two critical open-source security projects, VeraCrypt and WireGuard. This action immediately blocked their ability to sign...
Microsoft has suspended the Windows Hardware Program developer accounts for two critical open-source security projects, VeraCrypt and WireGuard. This action immediately blocked their ability to sign drivers and distribute updates to millions of Windows users. Developers confirmed they received no prior warning or explanation for the suspension.
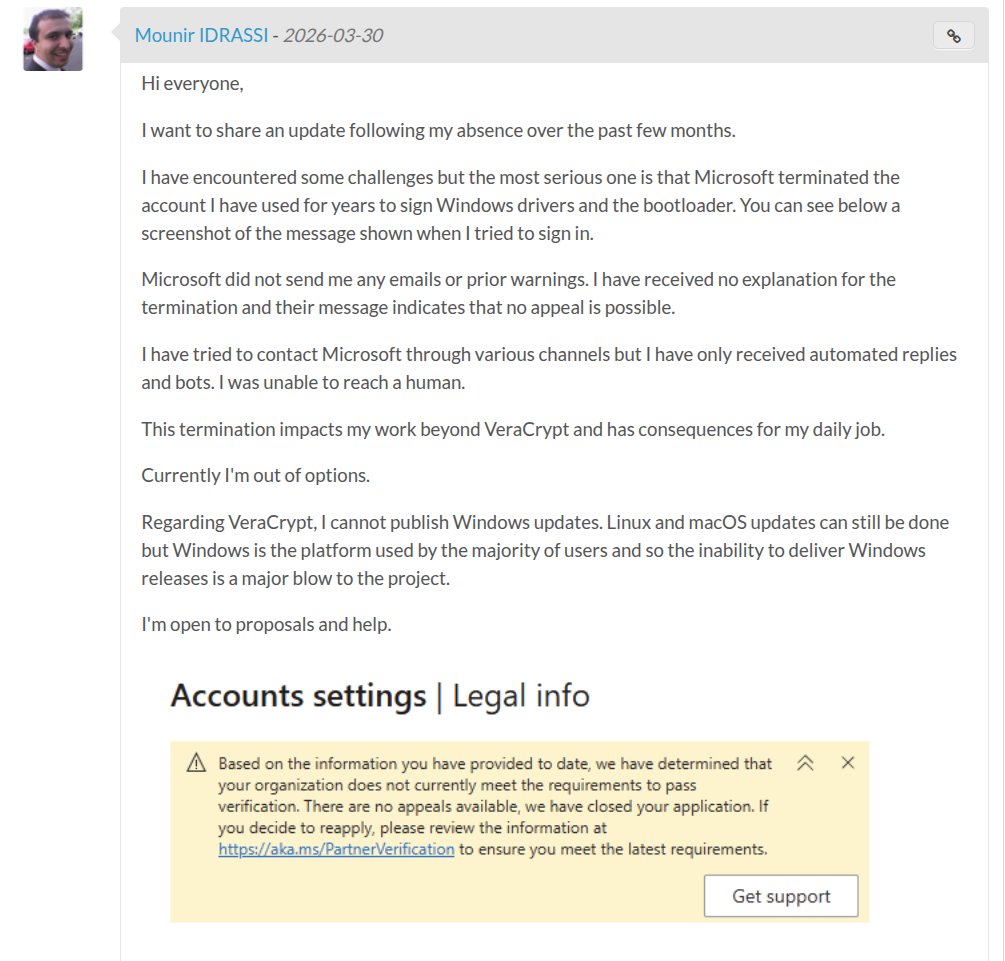
Mounir Idrassi, the lead developer of VeraCrypt, revealed in a March 30 post on SourceForge that Microsoft had abruptly terminated the account he had relied on for years to sign Windows drivers and the bootloader.
“I didn’t receive any emails from Microsoft nor any prior warnings,” Idrassi told 404 Media. Days later, Jason Donenfeld, creator of the widely used WireGuard VPN protocol, disclosed that he had faced an identical lockout without any notification from Microsoft about a new identity verification requirement. VPN provider Windscribe also reported a similar account suspension, suggesting a broader enforcement sweep.
A Microsoft developer account is required to authenticate third-party drivers on Windows 10 and 11. Without a valid, signed driver, Windows marks it as unsigned and prevents it from loading at the kernel level, making new builds functionally undeliverable to end users.
Suspended Developer Accounts
The suspensions appear to stem from Microsoft’s tightening of identity verification policies under its Partner Center program. Microsoft began enforcing stricter MFA and identity verification requirements beginning October 2025, with full API enforcement kicking in on April 1, 2026.
The new policy requires developers to undergo re-verification through trusted third-party identity verification vendors (IDVs) using government-issued ID documents. Accounts where identity verification is rejected and no “Fix now” option is presented are automatically suspended with no further recourse.
Neither Idrassi nor Donenfeld appears to have been notified that re-verification was required, leaving both developers effectively caught off guard.
The impact extends far beyond a bureaucratic inconvenience. VeraCrypt is one of the most trusted open-source disk encryption tools for Windows, relied upon by privacy-conscious individuals, journalists, and enterprises worldwide.
Idrassi has warned that if the issue remains unresolved, Secure Boot will refuse to allow VeraCrypt to encrypt system drives as of June 2026, describing the situation as a potential “death sentence for VeraCrypt”.
For WireGuard, the suspension means Donenfeld cannot ship updates to WireGuard for Windows, leaving users potentially exposed if a vulnerability is discovered in the interim.
The incident drew swift attention from inside Microsoft itself. Developer advocate Scott Hanselman stepped in, reaching out directly to both developers via email and pledging to expedite a resolution.
As of April 9, resolutions are expected shortly, though both developers are currently navigating a 60-day appeals process with no guaranteed outcome. The episode has reignited criticism over the fragility of critical open-source infrastructure when it depends on a single vendor’s gatekeeping mechanisms.
This incident underscores a systemic risk: open-source security projects that underpin global privacy infrastructure remain dangerously dependent on opaque, automated enforcement systems at large platforms.
When those systems misfire silently and without appeal pathways, the downstream consequences for end-user security can be severe and immediate.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.