Microsoft Outlook Add-in Stolen 4,000 Microsoft account
Security researchers have documented the first real-world deployment of a malicious Microsoft Outlook add-in actively targeting users. A compromised meeting scheduler named AgreeTo was used to steal...
Security researchers have documented the first real-world deployment of a malicious Microsoft Outlook add-in actively targeting users.
A compromised meeting scheduler named AgreeTo was used to steal over 4,000 Microsoft account credentials, credit card numbers, and answers to banking security questions.
AgreeTo began as a legitimate open-source project published to the Microsoft Office Add-in Store in December 2022.
It was a functional meeting tool with positive reviews. However, the developer eventually abandoned the project and deleted the associated Vercel deployment.
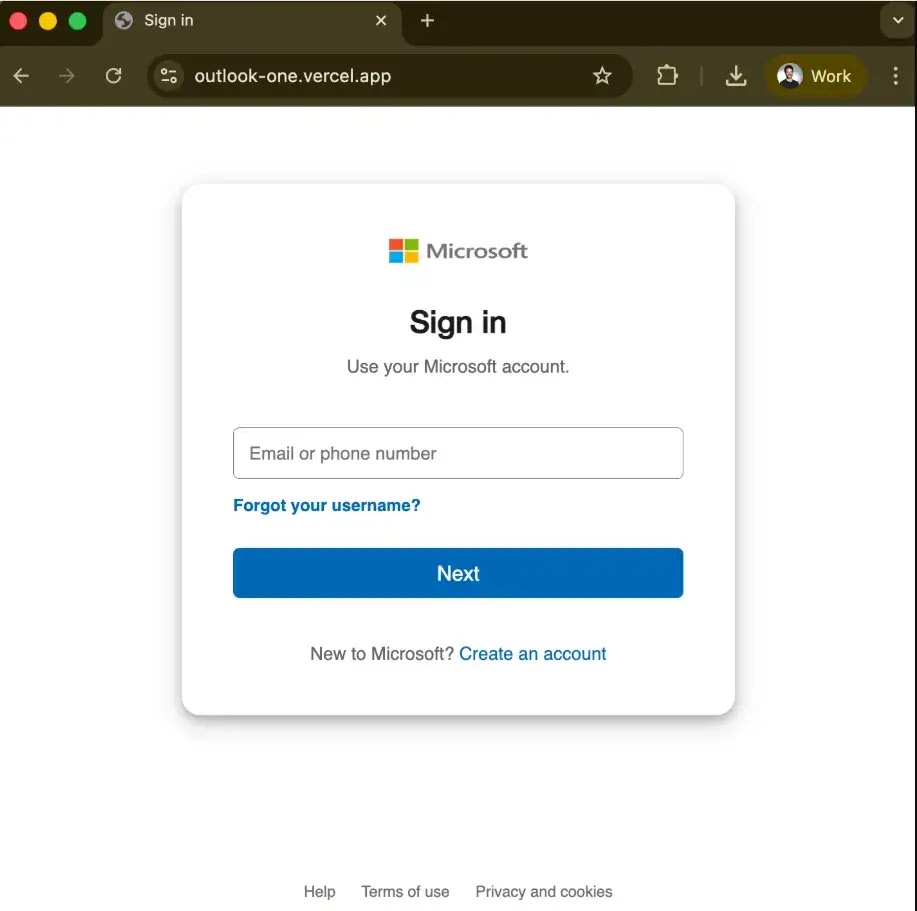
This left the add-in’s hosting URL (outlook-one.vercel.app) orphaned and available for registration. An attacker claimed the available URL and deployed a phishing kit.
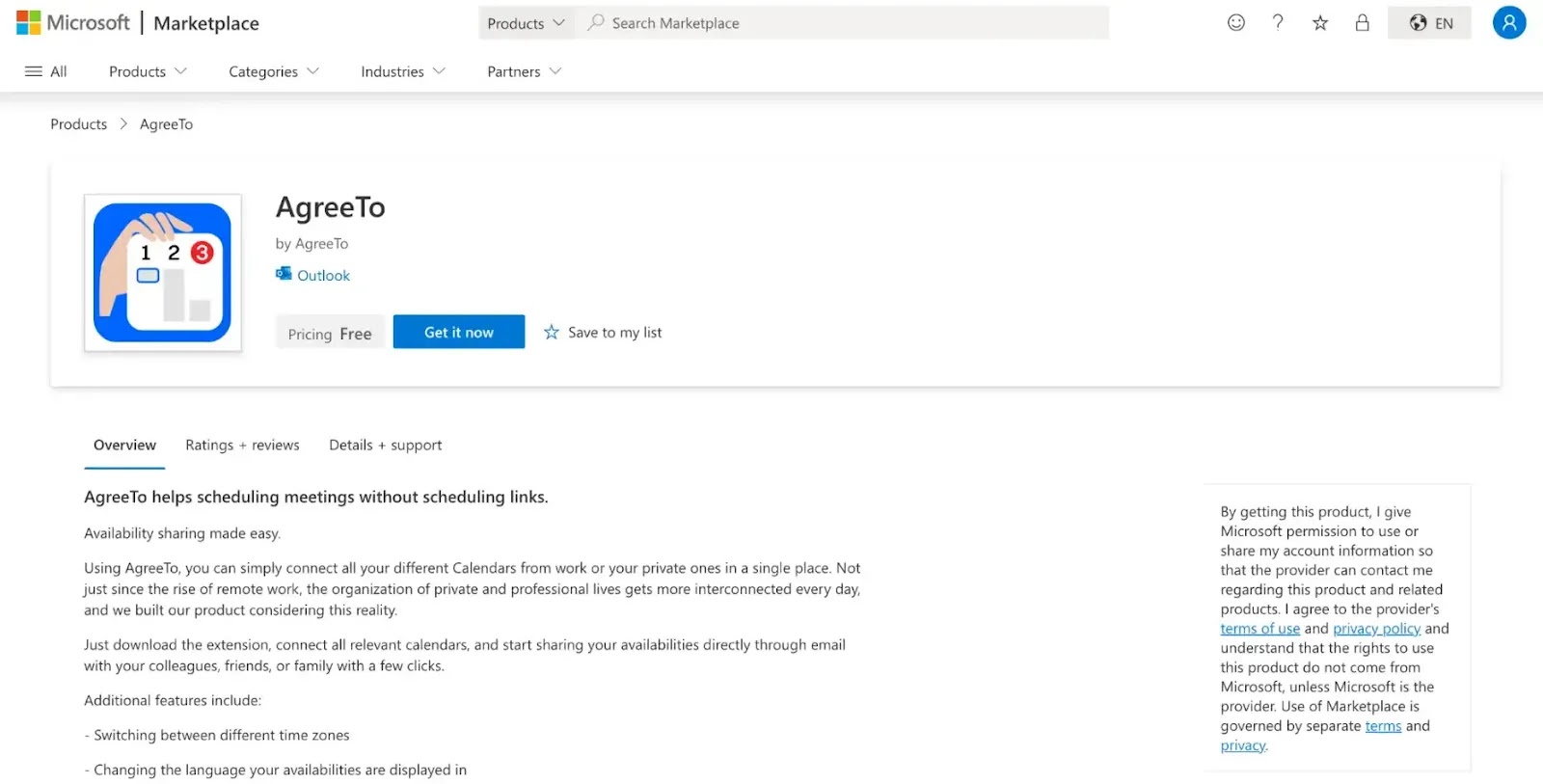
Because the add-in was never removed from Microsoft’s store, the attacker’s phishing page was served directly in the trusted Outlook sidebar to anyone who still had the add-in installed or had downloaded it fresh.
The Technical Flaw: Remote Dynamic Dependencies
The attack exploited the architecture of Office add-ins. Unlike traditional installed software, add-ins are “remote dynamic dependencies,” essentially XML manifests that load a URL in an iframe.
| Stage | Description |
|---|---|
| The Gap | Microsoft reviews the manifest only during the initial submission (2022 in this case). |
| The Exploit | Microsoft does not continuously verify the live content hosted at the approved URL. |
| The Result | The attacker swapped the scheduling tool with a fake Microsoft login page without triggering a new security review. |
When victims opened AgreeTo, they were prompted to log in. A script harvested their credentials and IP addresses, sending the data to the attacker via a Telegram bot.
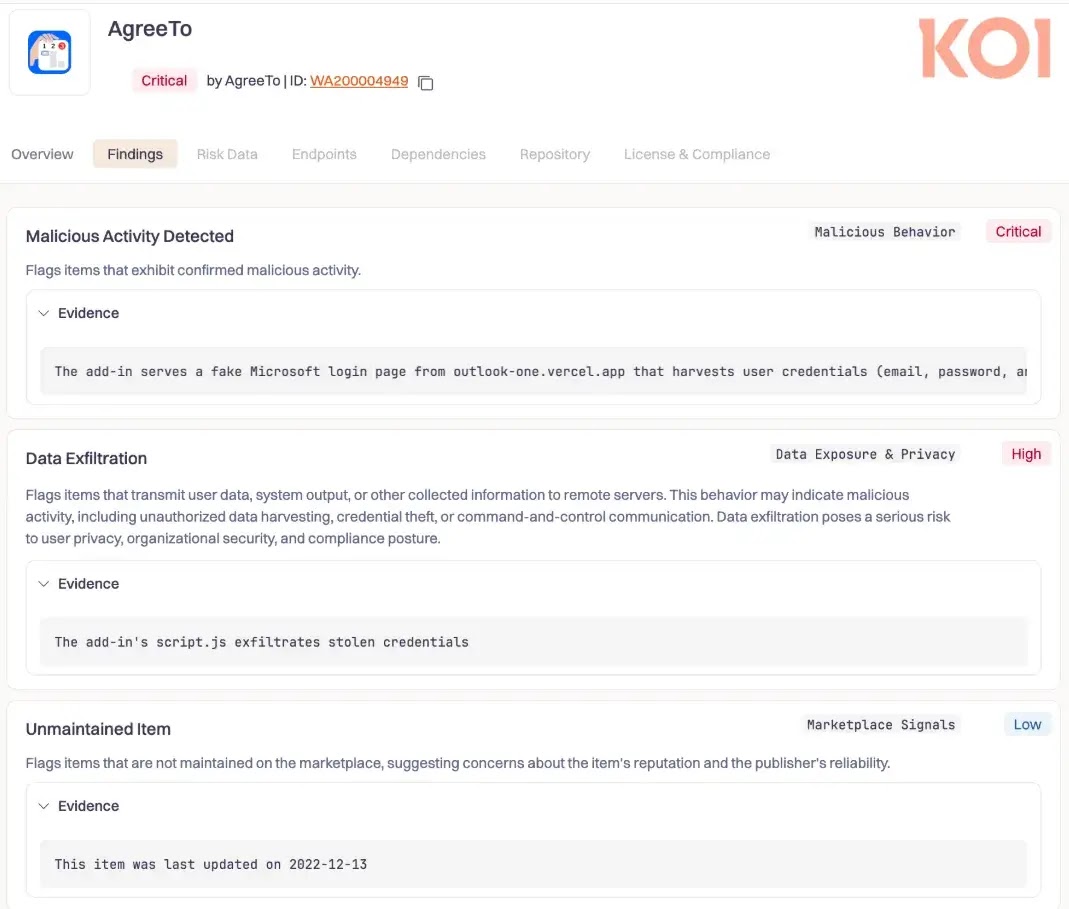
Koi Security discovered the campaign after identifying the attacker’s poorly secured exfiltration channel.
They recovered the full dataset of 4,000 victims, which included banking details and security answers targeting Canadian institutions.
The add-in had “ReadWriteItem” permissions, which technically allowed the attacker to read and modify users’ emails. However, the attack primarily focused on credential harvesting.
Microsoft has removed the add-in following the report. This incident highlights a critical supply chain risk: trusted software can silently become malicious years after approval if its infrastructure is abandoned.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.