Microsoft Defender Blocks Legitimate MAS During Script Hunt
Microsoft’s Windows Defender has begun blocking the popular open-source Microsoft Activation Scripts (MAS) tool. The security solution, while targeting fake impostors, is doing so without...
Microsoft’s Windows Defender has begun blocking the popular open-source Microsoft Activation Scripts (MAS) tool. The security solution, while targeting fake impostors, is doing so without verifying its impact on legitimate versions of the utility.
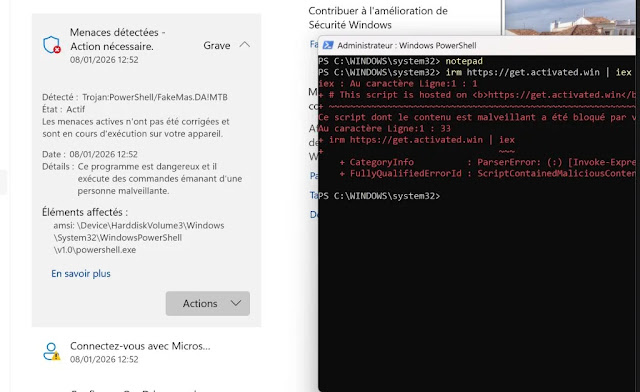
Users running the genuine PowerShell command now receive “Trojan:PowerShell/FakeMas.DA!MTB” alerts, prompting them to temporarily disable protections. This collateral damage highlights tensions between aggressive antivirus tactics and open-source utilities.
MAS, hosted on GitHub by the Massgrave team, lets users activate Windows and Office via scripts like irm https://get.activated.win | iex.
Recently, cybercriminals exploited its fame with typosquatted domains, such as get.activate.win (missing the ‘d’), to push malware-laden PowerShell payloads. Microsoft responded swiftly, updating Defender to automatically flag “FakeMas” threats.
False Positive Fallout
Defender’s filter, meant for fakes, now mistakenly hits the official get.activated.win domain due to a likely blacklist glitch.
Screenshots circulating online show French-localized alerts: “Trojan:PowerShell/FakeMas.DA!MTB” on legitimate fetches, with options to block or connect via Microsoft. Reddit users report quarantined MAS_AIO.cmd files, fixed only by renaming or exclusions.
Affected users add folder exclusions in Windows Security or submit false positives via Microsoft’s portal. The MAS team confirmed the issue on social media and urged vigilance across the domain to avoid malware.
Disabling Defender briefly works but exposes systems, ironically, as real threats could slip through if fake domains evade blocks.
Microsoft’s move underscores Defender’s AMSI integration, which scans PowerShell scripts in real time to thwart fileless attacks. Yet, it raises questions: Did hasty updates prioritize speed over precision? Past MAS flags were dismissed as false positives, but this ties directly to anti-malware efforts.
Cybersecurity experts note that such incidents erode trust in default protections, prompting users to adopt risky tweaks.
As of January 2026, no official Microsoft fix is available; users are monitoring for updates. This saga reminds the community: Even “smart” security can stumble in the typosquatting wars.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.