Malicious Party Invites Trick Users into Installing RATs
A new phishing campaign is luring users with deceptive party invitations designed to secretly install Remote Access Trojans (RATs) on Windows computers. The attack uses social engineering to deliver...
A new phishing campaign is luring users with deceptive party invitations designed to secretly install Remote Access Trojans (RATs) on Windows computers.
The attack uses social engineering to deliver ScreenConnect, a legitimate remote support tool, allowing threat actors to gain complete control of victim systems.
What appears to be a harmless invitation from a friend turns into a serious security breach that gives attackers unrestricted access to personal files, credentials, and sensitive data.
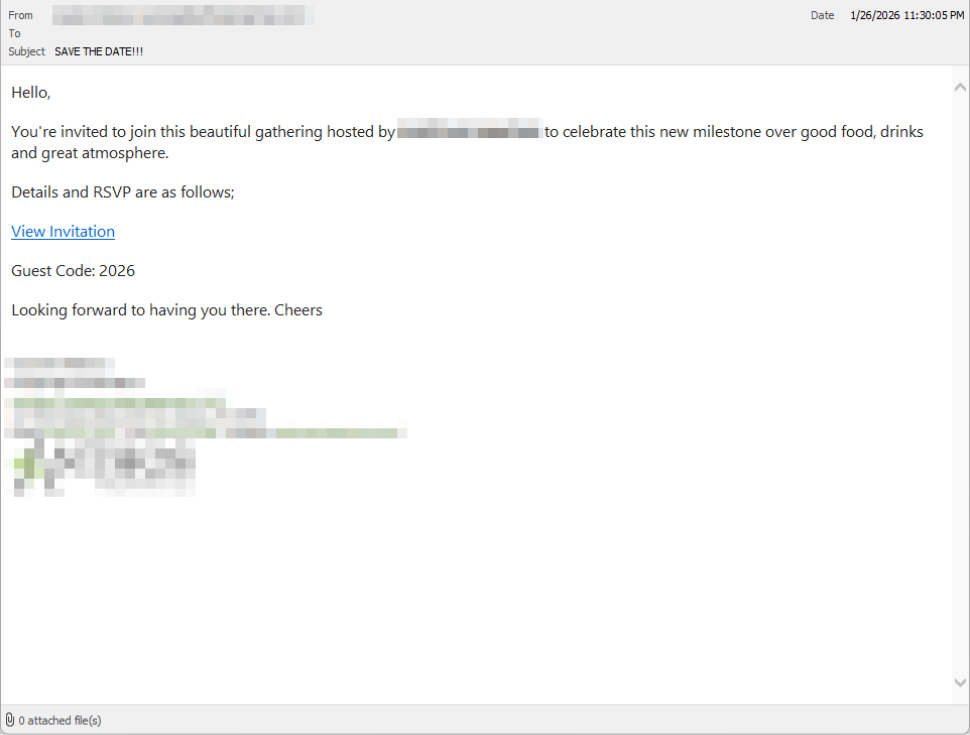
The campaign begins with emails designed to look like casual party invitations from trusted contacts.
These messages often come from compromised email accounts, making them appear authentic and familiar.
The informal tone and social context lower suspicion, encouraging recipients to click without hesitation.
Malwarebytes researchers identified this campaign primarily targeting users in the United Kingdom, though there are no technical barriers preventing its expansion to other regions.
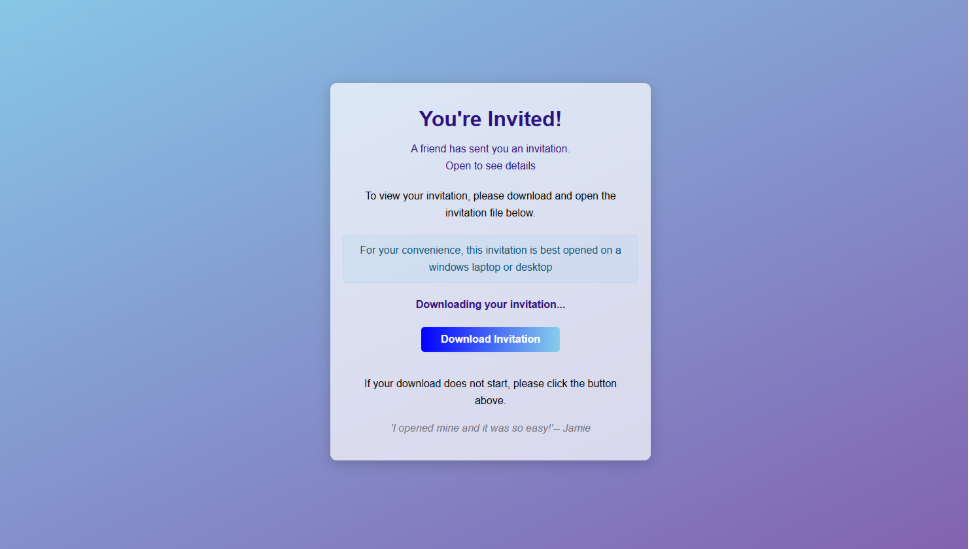
When victims click the link in the email, they land on a carefully crafted webpage that mimics a genuine event invitation.
The page displays a bold headline reading “You’re Invited!” along with messages suggesting a friend sent the invitation and that it should be viewed on a Windows device.
A countdown timer creates urgency by indicating the invitation is already downloading, while social proof statements like “I opened mine and it was so easy!” push users toward executing the file.
Within seconds, the browser automatically downloads a file named RSVPPartyInvitationCard.msi.
The downloaded MSI file is not an invitation at all but an installer that launches Windows Installer (msiexec.exe) to silently deploy ScreenConnect Client on the victim’s computer.
Malwarebytes analysts noted that the installation happens without clear user-facing notifications, making it difficult for victims to realize what is occurring.
The process installs ScreenConnect binaries under C:Program Files (x86)ScreenConnect Client and creates a persistent Windows service with randomized characters in its name, such as ScreenConnect Client 18d1648b87bb3023.
How the Remote Access Tool Establishes Control
Once ScreenConnect is installed, it initiates encrypted HTTPS connections to ScreenConnect relay servers using a uniquely assigned instance domain.
This connection grants attackers the same capabilities as a remote IT technician, including viewing the victim’s screen in real time, controlling the mouse and keyboard, uploading or downloading files, and maintaining access even after system restarts.
Since ScreenConnect is legitimate software commonly used for remote support, traditional security tools may not flag it as malicious.
The first signs of compromise often appear as behavioral anomalies, such as unexplained cursor movements, windows opening without user input, or unfamiliar processes running in the background that victims do not remember installing.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.