Horabot Banking Trojan Attacks Mexico with Phishing & Email Worm
The well-known banking trojan Horabot has resurfaced, launching an active campaign that targets users across Mexico. Its attack leverages a multi-stage infection chain alongside an email worm. This...
The well-known banking trojan Horabot has resurfaced, launching an active campaign that targets users across Mexico. Its attack leverages a multi-stage infection chain alongside an email worm. This worm transforms every compromised machine into a phishing relay.
The threat bundles a Delphi-based banking trojan with a PowerShell-driven spreader, making it one of the more layered financially motivated threats seen in Latin America.
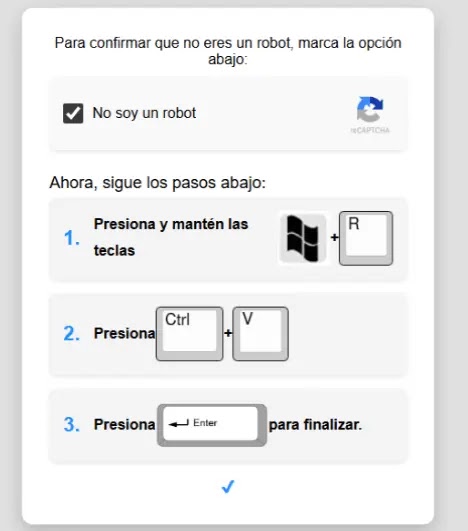
The attack begins with a fake CAPTCHA page that instructs victims to open the Windows Run dialog and paste a malicious command. Rather than exploiting a software flaw, attackers trick users into executing a malicious HTA file that silently launches the infection chain.
This method sidesteps many endpoint defenses by turning the victim into an unknowing participant in their own compromise.
Securelist analysts identified this campaign after a suspicious mshta execution alert triggered within a monitored customer environment.
The team traced the activity to a fake CAPTCHA page and mapped the full attack chain by probing the adversary’s infrastructure.
During that process, researchers found an exposed victim log on the attacker’s own server, revealing 5,384 infected machines — 5,030, or roughly 93%, located in Mexico. Records stretched back to May 2025, confirming the operation had been running for months before detection.
The threat actors show clear ties to Brazil. Comments inside the spreader’s PowerShell code were written in casual Brazilian Portuguese, and the encryption key used for resource decryption references the phrase “pega a visão,” meaning “get the picture” in Brazilian slang.
The phishing emails distributed by the worm are written in Spanish and crafted as fake invoices or confidential business documents targeting Mexican recipients.
The Delphi banking trojan — also tracked as Casbaneiro, Ponteiro, and Metamorfo — uses fake bank overlay pop-ups to steal login credentials during active banking sessions.
The email worm also harvests contact addresses from the victim’s inbox through the MAPI namespace and sends phishing emails to each one, carrying a malicious PDF that restarts the entire infection cycle.
Multi-Stage Infection Mechanism
What sets this campaign apart is not just its payload, but the elaborate delivery route. Each stage introduces a fresh layer of obfuscation before the final malware arrives.
After the HTA file executes, it fetches a JavaScript loader from an attacker-controlled domain, which then pulls and runs an obfuscated VBScript.
This VBScript uses server-side polymorphism — delivering a slightly different version of the code on every request to defeat signature-based detection.
A second, more complex VBScript of over 400 lines acts as the operation’s workhorse, collecting the victim’s IP address, hostname, username, and OS version before sending that data to a command-and-control server.
It drops AutoIT components to disk, plants a LNK shortcut in the Startup folder for persistence, and downloads the next stage.
The AutoIT script then decrypts an AES-192-encrypted blob using a key derived from the seed value 99521487 and loads the resulting DLL directly into memory — that DLL is the banking trojan.
It communicates with its C2 server over a custom TCP protocol, wrapping commands in structured tags, with all traffic encrypted through a stateful XOR cipher.
The output is framed between double "##" markers, a pattern rare enough in legitimate traffic to work as a reliable network detection signature.
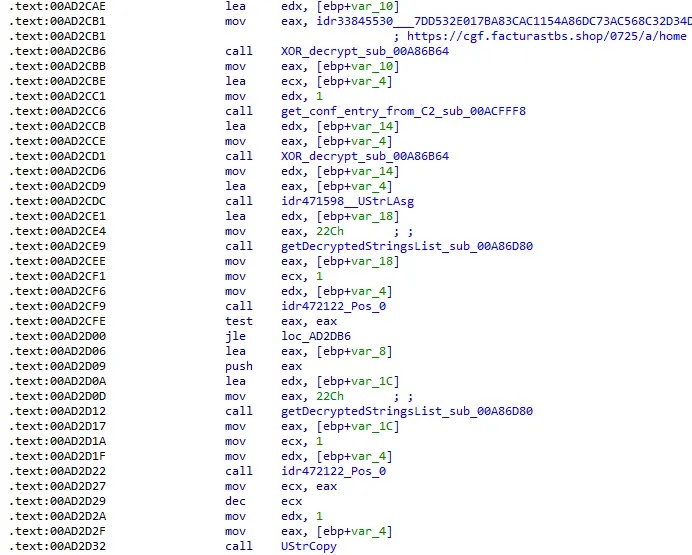
Analysts noted that the cipher’s rigid, repetitive structure actually makes it easier to catch with a standard IDS rule.
Security teams should block HTA file execution from untrusted sources and monitor closely for suspicious mshta activity.
Deploying the published YARA rules for both the Horabot Delphi trojan and AutoIT loader, together with the Suricata rule targeting the double "##" C2 traffic pattern, will help detect infections early.
All shared indicators of compromise — including the attacker-controlled domains and socket addresses — should be added to network blocklists without delay.
User awareness training on fake CAPTCHA lures and PDF attachments with embedded buttons remains a critical defense layer.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.