Popular Python Package ‘lightning’ Hacked in Supply Chain
A supply chain attack has targeted the popular PyTorch Lightning framework, resulting in the automatic execution of credential-stealing malware when imported. The incident also led to the compromise...
A supply chain attack has targeted the popular PyTorch Lightning framework, resulting in the automatic execution of credential-stealing malware when imported. The incident also led to the compromise of GitHub maintainer accounts.
Table Of Content
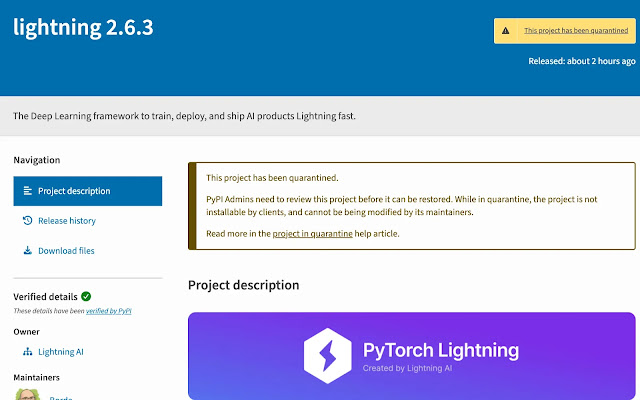
The popular PyPI package lightning — the deep learning framework used to train, deploy, and ship AI products has been compromised in an active supply chain attack.
Socket’s Research Team flagged versions 2.6.2 and 2.6.3 as malicious just 18 minutes after publication on April 30, 2026. Version 2.6.1, released on January 30, 2026, remains clean and is considered the last safe baseline.
With hundreds of thousands of daily downloads and millions of monthly installations on PyPI, lightning is a cornerstone of Python-based AI and machine learning workflows.
The attack directly targets developer machines, CI/CD pipelines, and cloud build environments. Any system that has installed and imported the compromised versions is considered at risk.
Hidden Malware Execution Chain
Socket’s analysis revealed a hidden _runtime directory embedded inside the malicious packages containing a multi-stage execution chain that activates automatically when the module is imported, requiring no additional user interaction. The components identified include:
start.py— Downloads and executes Bun, a JavaScript runtime, directly from GitHubrouter_runtime.js— An 11 MB heavily obfuscated JavaScript payload containing 703 references toprocessandenv, over 463 references to tokens and authentication material, and 336 references to repositories- Daemon thread execution — The malware runs silently with suppressed output, making detection extremely difficult
- Credential exfiltration — Targets GitHub tokens, NPM tokens, cloud credentials (AWS, GCP, Azure), environment variables, and other secrets
- GitHub API abuse — Uses stolen tokens to commit encoded data to attacker-controlled repositories
- NPM package infection — Capable of poisoning developer NPM package tarballs to extend persistence
The obfuscated router_runtime.js payload shares significant technical overlap with the Shai-Hulud attack campaign, including identical credential targeting patterns, token theft logic, and obfuscation techniques.
This is consistent with Team PCP’s escalating open-source supply chain campaign, which previously compromised LiteLLM (March 24, 2026), Telnyx (March 27, 2026), and Xinference in rapid succession.
During the incident response window, an attacker posted a Tor onion link in the Lightning-AI GitHub issue thread pointing to a Team PCP-branded site with a PGP-signed message claiming involvement of LAPSUS$ as “a good partner” throughout the operation.
Socket has not independently verified this attribution and is investigating whether the Team PCP branding reflects true attribution, opportunistic association, or a deliberate false-flag.
GitHub Maintainer Account Appears Compromised
Community member reports surfaced in Lightning-AI’s GitHub repository under issue #21689, titled “Possible supply chain attack on version 2.6.3.”
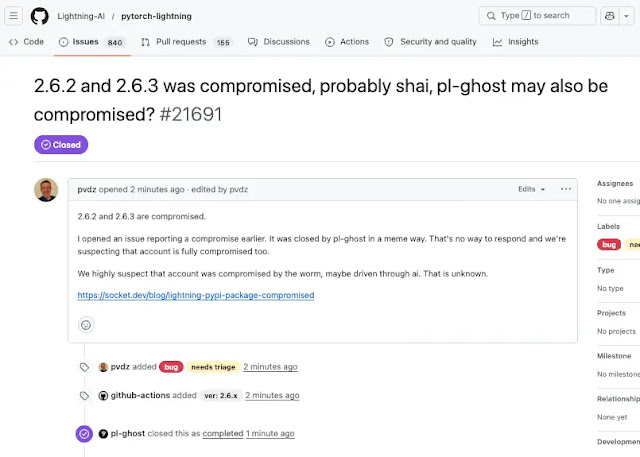
When Socket subsequently filed a follow-up warning in the pytorch-lightning repository, the issue was closed within one minute by the pl-ghost account, which then posted a “SILENCE DEVELOPER” meme — strongly indicating the project’s GitHub account has been taken over.
Mitigations
Security teams should treat any environment that is installed and imported lightning versions 2.6.2 or 2.6.3 are fully compromised and act immediately:
- Remove versions 2.6.2 and 2.6.3 from all affected systems
- Downgrade to version 2.6.1 or await official confirmation from maintainers
- Rotate all credentials — GitHub tokens, NPM tokens, cloud access keys (AWS, GCP, Azure), and any secrets stored in environment variables
- Audit GitHub repositories for unauthorized commits or suspicious encoded data
- Review CI/CD pipeline logs, developer workstations, and build systems where the package may have been imported
Socket is continuing its technical analysis and will publish a deeper investigation, including confirmed indicators of compromise (IOCs) and attribution findings, as the incident develops.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.