Hackers Leverage Browser-in-the-browser Tactic to Trick Facebook
A sophisticated new phishing technique, dubbed ‘Browser-in-the-browser’ (BitB) phishing, is increasingly targeting Facebook users and effectively bypassing conventional security measures....
A sophisticated new phishing technique, dubbed ‘Browser-in-the-browser’ (BitB) phishing, is increasingly targeting Facebook users and effectively bypassing conventional security measures. This deceptive tactic involves creating convincing fake browser windows directly within a legitimate web page. Attackers leverage BitB to trick individuals into divulging sensitive credentials, proving particularly effective against platforms like Facebook and other major services.
With over three billion active users on the platform, Facebook represents an attractive target for attackers seeking to compromise accounts and harvest personal credentials.
The primary objective of these attacks remains clear: steal login credentials to hijack accounts, spread fraudulent schemes, steal sensitive data, and commit identity fraud across victim networks.
In the second half of 2025, a noticeable surge in Facebook phishing campaigns emerged, employing various methods to deceive users.
Among these techniques, one method stands out for its technical sophistication and effectiveness.
The threat landscape has shifted dramatically, with attackers moving beyond simple malicious links toward more advanced approaches that exploit user trust and familiarity with legitimate login processes.
Trellix analysts identified and documented this emerging threat after observing increased phishing activity targeting the platform.
The researchers noted that attackers were implementing advanced social engineering tactics combined with technical evasion measures to maximize their success rates.
This observation marks an important evolution in Facebook-targeted attacks, indicating that threat actors are investing in more refined methodologies to bypass traditional security awareness training.
Browser-in-the-Browser (BitB) technique
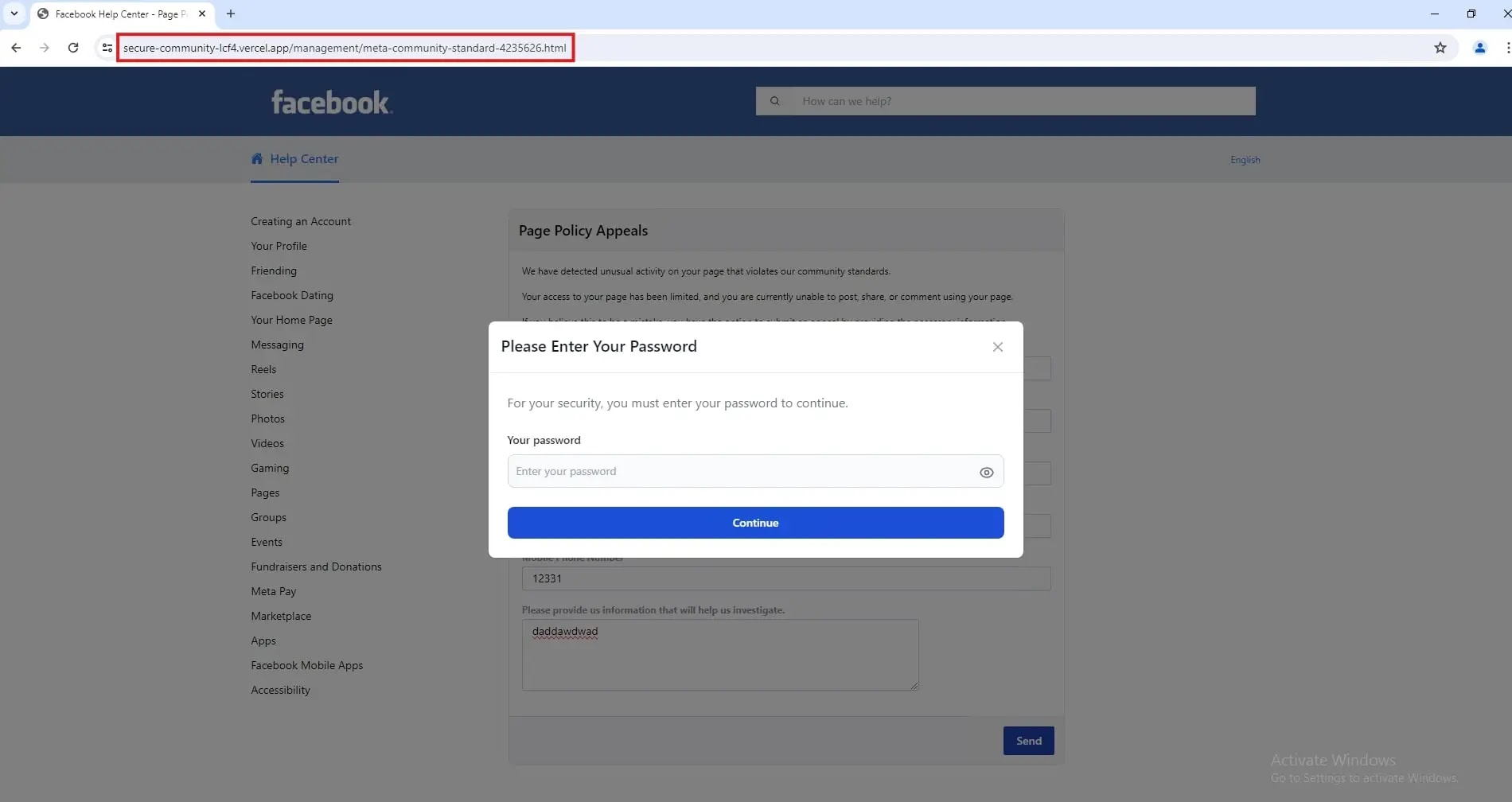
The Browser-in-the-Browser (BitB) technique represents the most notable innovation in these campaigns.
This method works by creating a completely custom-built fake window that exists entirely within the victim’s legitimate browser window, making it nearly impossible to distinguish from genuine authentication pop-ups.
The technique exploits users’ familiarity with login windows, capitalizing on their expectation to see such prompts when accessing the platform.
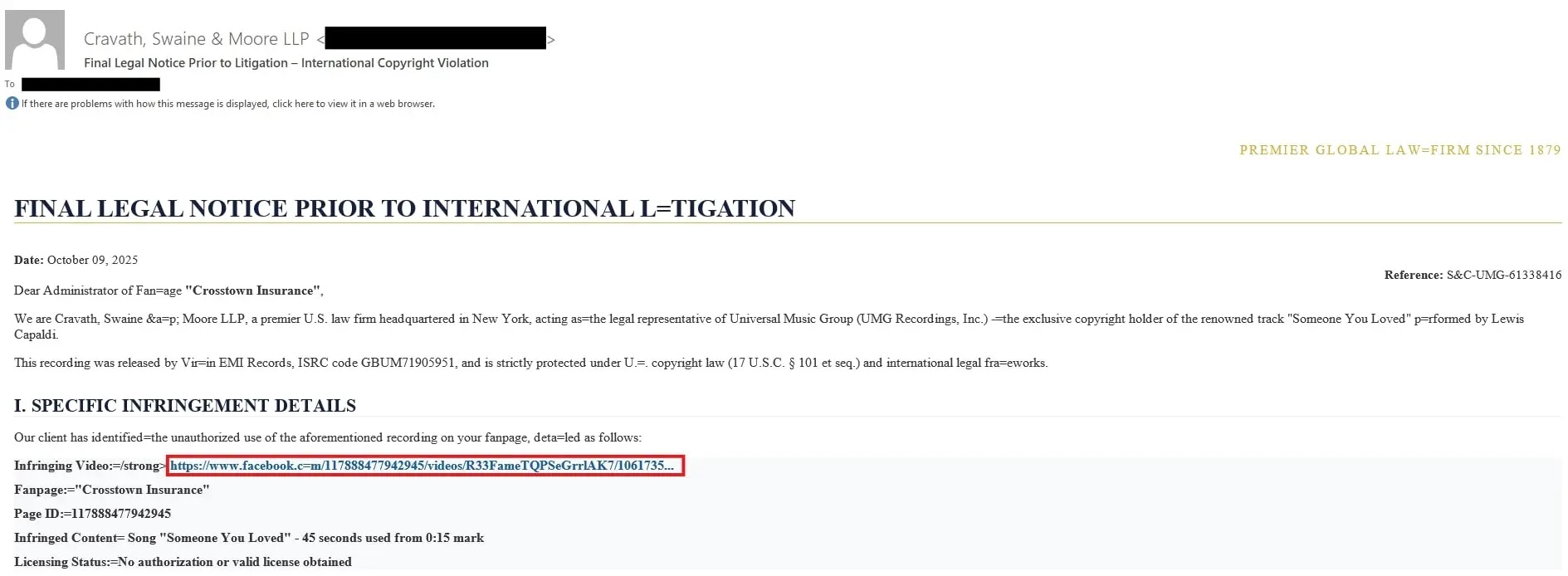
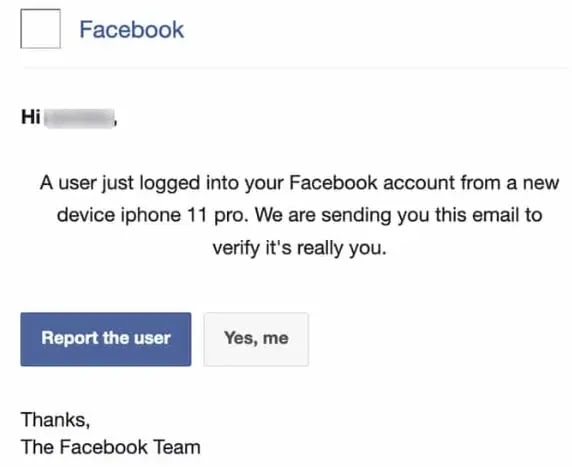
The attack sequence typically begins with a phishing email disguised as communication from a law firm, containing a fake legal notice about an infringing video and a Facebook login link.
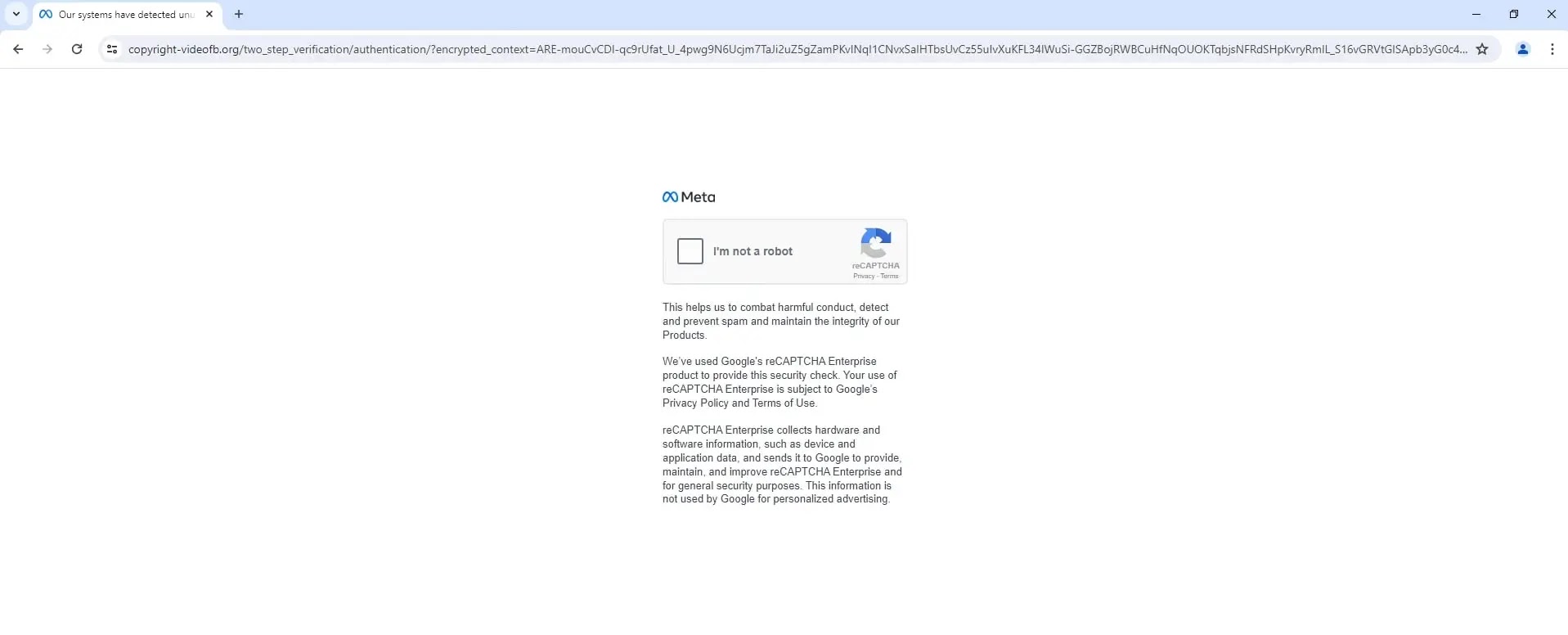
The hyperlink uses shortened URLs that redirect to fake Meta CAPTCHA pages, adding additional layers of deception.
When users interact with these pages, they encounter what appears to be a legitimate Facebook login pop-up window. However, examining the underlying code reveals the malicious nature of the attack.
The Facebook URL is hardcoded within the fake interface, creating an entirely fraudulent authentication environment.
The sophistication of this approach lies in how attackers abuse legitimate infrastructure. Threat actors host phishing pages on trusted cloud platforms like Netlify and Vercel, leveraging their reputation to bypass security filters.
URL shortening services mask the actual destination, providing additional anonymity.
This combination of technical sophistication and social engineering represents a significant escalation in Facebook phishing tactics, requiring users to maintain heightened vigilance beyond standard security practices.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.