Hackers Deploy Android Malware via Fake ChatGPT Invites
Cybercriminals are targeting Android users with a sophisticated phishing scheme, deploying malicious applications disguised as beta-testing opportunities for popular AI tools like Following the iOS...
Cybercriminals are targeting Android users with a sophisticated phishing scheme, deploying malicious applications disguised as beta-testing opportunities for popular AI tools like
Since the email originates from a real Google service address, most recipients have no reason to question its legitimacy.
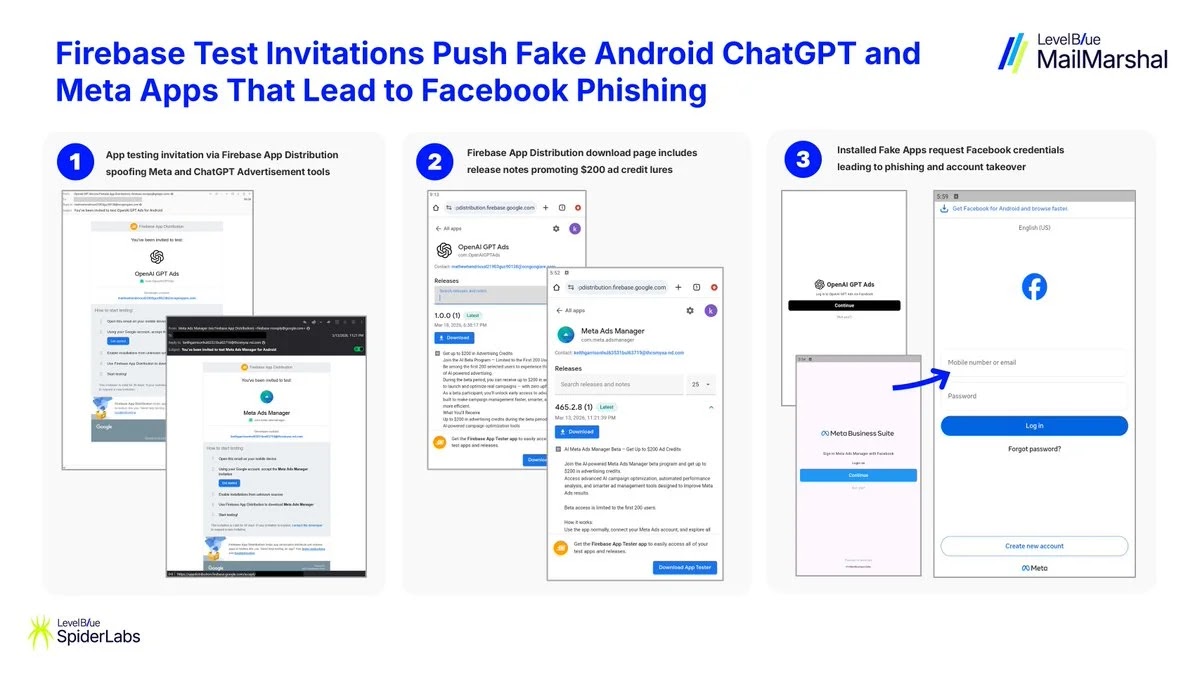
These messages ask users to test what appear to be early-access versions of ChatGPT and Meta advertising apps for Android, and clicking through leads to the installation of malicious APK files outside the official Play Store.
SpiderLabs analysts at LevelBlue identified this Android-targeting campaign as a direct continuation of an earlier phishing operation that had gone after iOS users.
In that prior campaign, attackers impersonated ChatGPT and Google Gemini to push fake applications onto Apple devices through the App Store.
With Android now firmly in the crosshairs, the threat actors appear to be running a coordinated, cross-platform operation designed to cast the widest possible net across the global mobile user base.
The campaign came to public attention in late March 2026, and the malicious package names tied to the operation include com.OpenAIGPTAds, com.opengpt.ads, and com.meta.adsmanager.
These package identifiers are built to resemble plausible names for AI-driven advertising tools, making them harder to question without a closer look.
Once installed, the apps present what appears to be a real Facebook login page, prompting the user to enter their credentials.
The final goal is account takeover, giving attackers access to Facebook business and advertising accounts that can be used for unauthorized ad campaigns or broader data theft.
How Firebase App Distribution Becomes the Attack Pipeline
The most technically striking aspect of this campaign is how it turns Firebase App Distribution into a delivery mechanism for malware.
Firebase App Distribution is a service by Google that lets developers send test builds of their apps to a small group of users ahead of a full public release.
People who regularly participate in app testing are conditioned to trust these invitation emails, and the attackers exploit precisely that habit.
The phishing emails look indistinguishable from a genuine developer invite, giving recipients no obvious visual clue that something is wrong.
By routing delivery through an established Google channel, attackers sidestep two red flags that careful users typically watch for: a suspicious sender address and an unofficial download link.
Since the email arrives from [email protected] and the app comes through Google’s own distribution infrastructure, neither the email client’s spam filter nor the user’s natural instincts are likely to raise an alarm.
The apps install outside the Play Store, bypassing Google’s review process entirely, which allows malicious behavior to reach the device unchecked.
SpiderLabs researchers further identified several malicious email domains actively supporting this campaign, including thcsmyxa-nd[.]com, moitasec[.]com, tourmini[.]site, ocngongiare[.]com, disanviet[.]homes, and itrekker[.]space.
Security teams and individuals should treat these as active indicators of compromise and block them at the network level without delay.
Android users should treat any unsolicited app-testing invitation with real caution, even those that appear to come from Google addresses. Applications should only be downloaded from the official Google Play Store.
Users should never enter Facebook credentials inside an app that was not downloaded through a trusted, verified channel.
Network administrators and security teams are advised to block the identified malicious domains immediately, and organizations should ensure their staff members are well informed about this specific and increasingly common form of social engineering.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.