Hackers Breached Companies via Leaked Cloud Cred Threat Actors
A deceptively simple yet highly effective attack vector—stolen credentials harvested by infostealer malware—has led to breaches across dozens of major global enterprises. A threat actor operating...
A deceptively simple yet highly effective attack vector—stolen credentials harvested by infostealer malware—has led to breaches across dozens of major global enterprises.
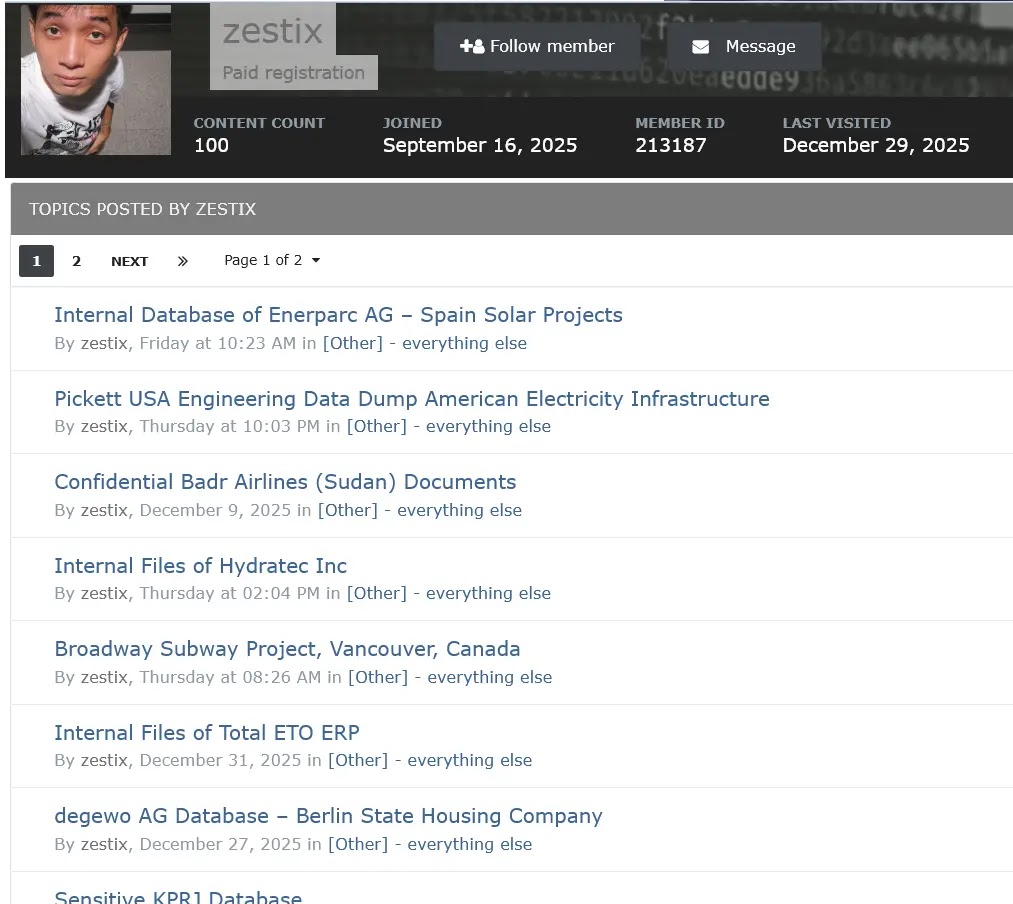
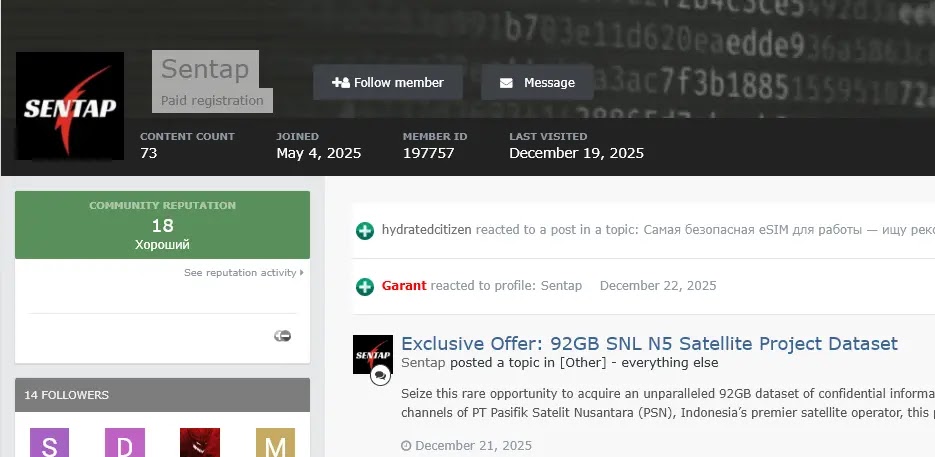
A threat actor operating under the nickname “Zestix” and his alias “Sentap” has been systematically accessing corporate cloud storage platforms, including ShareFile, Nextcloud, and OwnCloud, belonging to approximately 50 international organizations.
The breaches span critical sectors such as aviation, defense robotics, healthcare, finance, and government infrastructure, exposing terabytes of sensitive data.
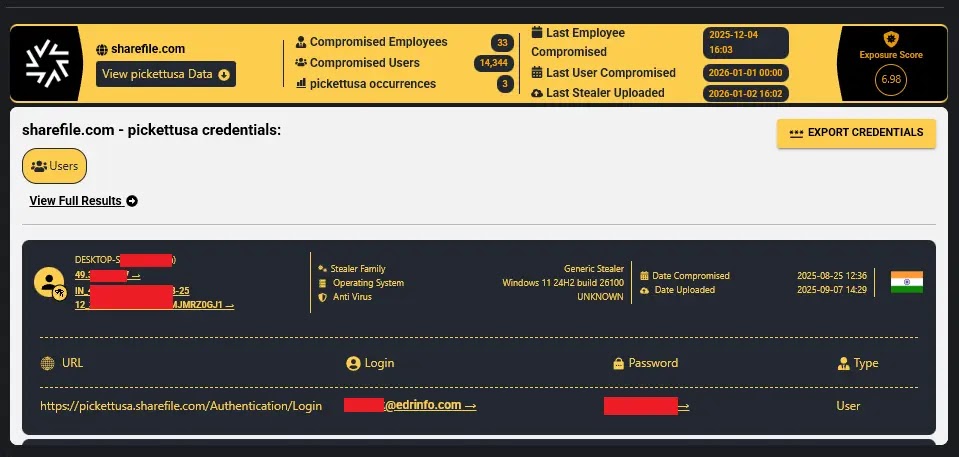
The attack chain reveals a troubling reality in modern cybersecurity. Employees inadvertently download malicious files that execute infostealers like RedLine, Lumma, and Vidar.
These malware variants silently harvest all saved credentials and browser history from infected devices. Once extracted, these logs are aggregated into massive databases on the dark web.
Zestix then searches through these repositories specifically looking for corporate cloud URLs and uses the stolen credentials to gain unauthorized access to enterprise systems.
InfoStealers analysts and researchers noted that the most critical vulnerability enabling these breaches was not a sophisticated zero-day exploit, but rather the fundamental absence of Multi-Factor Authentication (MFA).
Organizations failed to implement this standard security control, allowing attackers to walk through the front door using only a valid username and password.
Some credentials had been sitting in infostealer logs for years, creating a window of opportunity that organizations completely missed.
The scale of the compromises is alarming. Pickett and Associates, an engineering firm serving U.S. utility companies, lost 139.1 gigabytes including classified LiDAR files and transmission line maps.
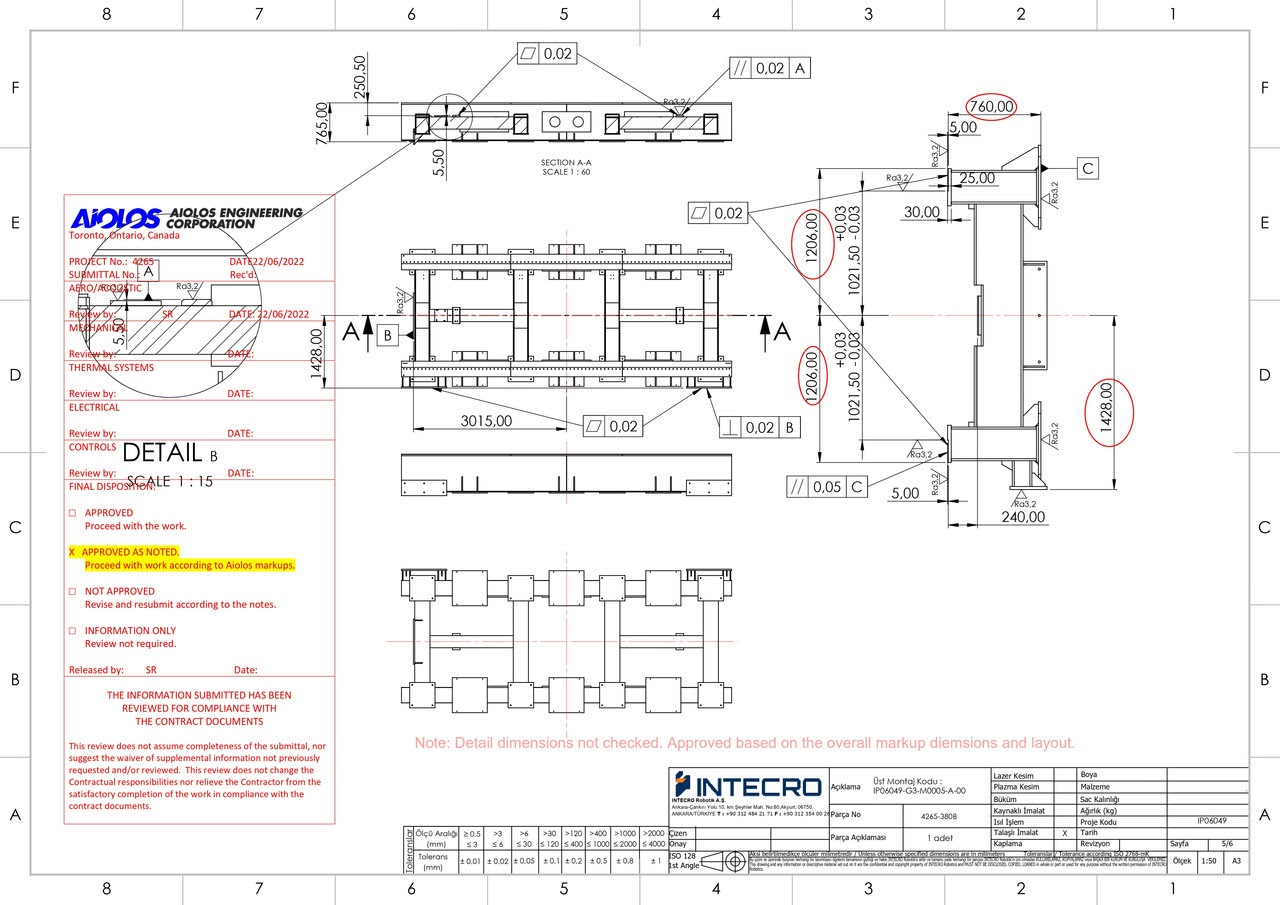
Intecro Robotics exposed 11.5 gigabytes of ITAR-controlled defense blueprints for military aircraft components. Iberia Airlines had 77 gigabytes leaked, containing aircraft maintenance programs and critical flight safety documentation.
Brazilian military police health records belonging to Maida Health—2.3 terabytes in total—were exposed, along with personal identification and medical information for active-duty personnel and their families.
The Credential Harvesting Mechanism
The infection cycle operates through a five-stage process that cybersecurity professionals must understand. First, an employee receives a seemingly legitimate file through email or downloads what appears to be standard software.
Second, the infostealer executes in memory, often avoiding detection by security tools because it operates within legitimate processes. Third, the malware enumerates browser storage, password managers, and cached credentials from applications like Outlook and Teams.
Fourth, all harvested data is encrypted and transmitted to command-and-control servers. Finally, threat actors parse through thousands of stolen credential databases, filtering specifically for corporate infrastructure like cloud file shares and ERP systems.
What makes this approach particularly dangerous is its scale and low cost. Zestix operates as an Initial Access Broker, selling corporate access credentials for Bitcoin or Monero on underground forums.
Organizations have failed not because they lack security awareness programs, but because they have not enforced mandatory multi-factor authentication across all critical systems.
The remedy is straightforward: immediate MFA deployment combined with monitoring for compromised credentials in infostealer logs before attackers exploit them.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.