Google Warns WinRAR Exploit Hijacks Windows Systems
A critical security flaw in WinRAR, one of the most widely used file compression tools for Windows, is being actively exploited by attackers. This vulnerability allows them to gain unauthorized...
A critical security flaw in WinRAR, one of the most widely used file compression tools for Windows, is being actively exploited by attackers. This vulnerability allows them to gain unauthorized access to computer systems.
The vulnerability, tracked as CVE-2025-8088, allows threat actors to place malicious files into sensitive system directories without user awareness, essentially handing over control of Windows machines.
First exploited in July 2025, this security gap continues to threaten millions of users despite a patch being available since July 30, 2025.
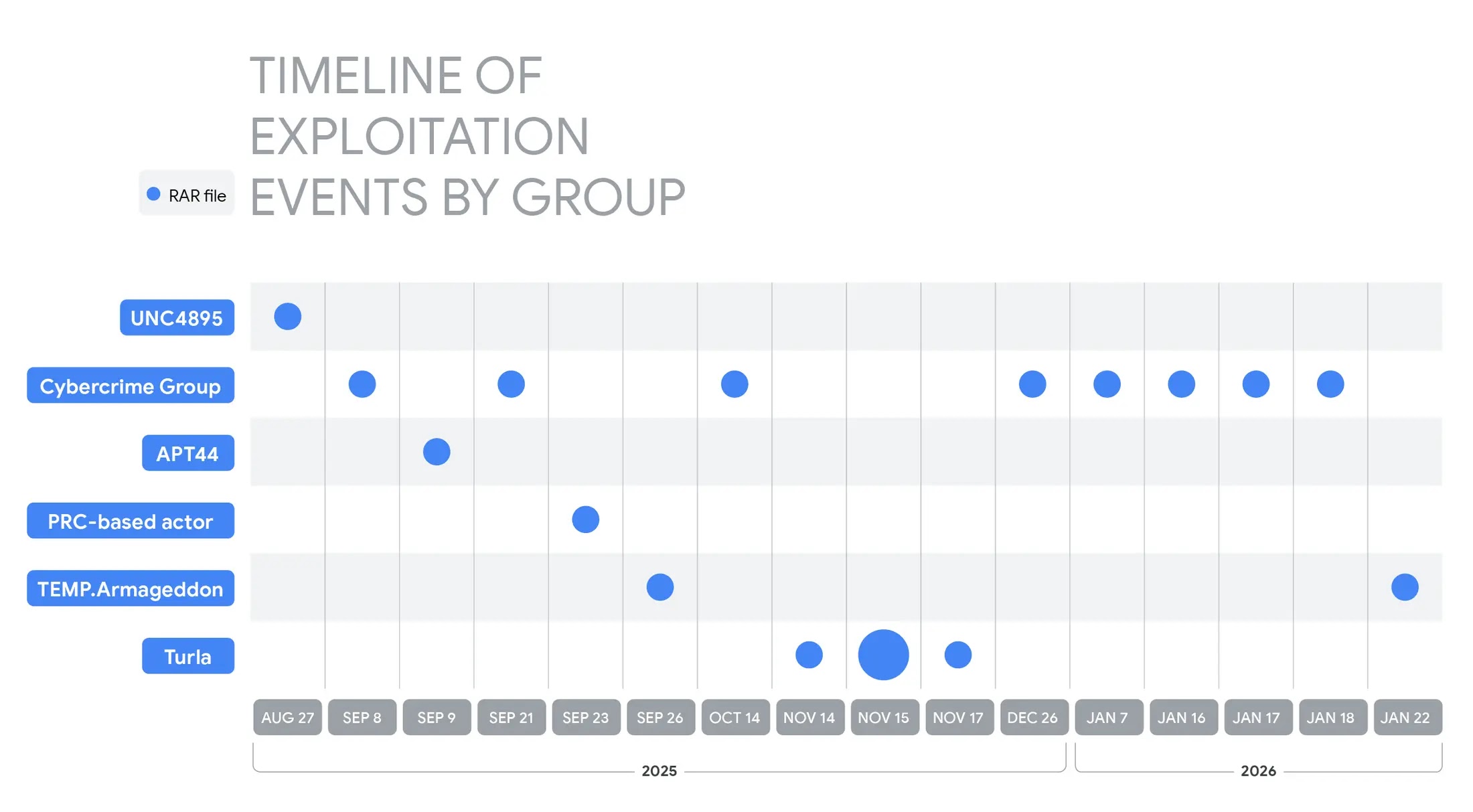
The flaw has attracted attention from diverse attacker groups ranging from government-backed espionage operations linked to Russia and China to financially motivated criminals targeting businesses worldwide.
These adversaries have weaponized the vulnerability to deliver malware, steal credentials, and establish persistent access to compromised systems.
The attack method involves crafting specially designed RAR archive files that exploit a path traversal weakness, allowing files to be written to arbitrary locations on victim computers.
Google Cloud researchers identified widespread exploitation of this vulnerability across multiple campaigns targeting Ukrainian military and government organizations, technology companies, and commercial sectors including hospitality and banking.
The researchers observed that attackers consistently leverage the flaw to drop malicious files directly into the Windows Startup folder, ensuring their malware automatically executes each time the victim logs into their system.
This technique mirrors the exploitation pattern seen with a previous WinRAR vulnerability (CVE-2023-38831) in 2023, demonstrating how attackers repeatedly capitalize on unpatched software.
Organizations and individual users remain vulnerable if they haven’t updated to WinRAR version 7.13 or later.
Security experts emphasize the importance of immediate patching, noting that attackers continue exploiting known vulnerabilities long after fixes become available.
Google recommends using Safe Browsing and Gmail security features, which actively block files containing the exploit.
How Attackers Exploit the Vulnerability
The exploitation technique centers on manipulating Alternate Data Streams (ADS), a Windows file system feature that attackers abuse to hide malicious content.
When victims open a weaponized RAR archive, they typically see an innocuous document like a PDF, while hidden malicious files are silently extracted to critical system locations.
The attackers craft file paths using directory traversal characters that navigate through folder structures to reach the Windows Startup directory.
For example, a malicious archive might contain a file named “innocuous.pdf:malicious.lnk” with a crafted path that writes directly to the Startup folder.
Once placed there, the malicious file automatically runs when the user next logs in, giving attackers persistent control without requiring further interaction.
This method has proven effective across campaigns by Russian groups like UNC4895 and APT44 targeting Ukraine, Chinese actors deploying POISONIVY malware, and cybercriminals distributing remote access tools and information stealers to victims in Indonesia, Latin America, and Brazil.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.