FUNNULL Triad Nexus Resurfaces with 1 FUNNULL-Linked Rotating
A cybercriminal group linked to the FUNNULL Content Delivery Network has resurfaced, deploying a significantly more sophisticated and evasive infrastructure. Known as Triad Nexus, the group has...
A cybercriminal group linked to the FUNNULL Content Delivery Network has resurfaced, deploying a significantly more sophisticated and evasive infrastructure.
Known as Triad Nexus, the group has rebuilt its global fraud operation following U.S. Treasury sanctions, deploying over 175 randomly rotating CNAME domains to power a sprawling network of scam portals that target victims across multiple countries.
Triad Nexus is not a new player in the threat landscape. The group is deeply rooted in organized criminal networks across Asia and has been actively running investment scams, money laundering operations, and illegal gambling platforms since at least 2022.
Its earlier campaigns relied heavily on the FUNNULL CDN as the primary backbone, enabling fast delivery of fraudulent websites designed to look exactly like trusted global brands.
What changed after the U.S. sanctions was not the group’s criminal intent — it was their method of concealment.
Following the May 2024 federal sanctions, the group rapidly pivoted to what researchers describe as “infrastructure laundering.”
Rather than relying solely on low-reputation servers, Triad Nexus began hijacking legitimate enterprise cloud accounts at major providers including Amazon Web Services, Cloudflare, Google, and Microsoft.
By routing malicious traffic through these trusted platforms, the group created an appearance of legitimacy that made its fake portals far harder to detect or block.
Silent Push analysts and researchers identified this tactical shift as a major evolution, noting that the group had abandoned stable CNAME domains in favor of a rotating pool of over 175 randomly generated CNAME domains — each one connecting clusters of fraudulent websites to stolen or illicitly acquired IP addresses.
The scale of the fraud is staggering. Triad Nexus has been linked to over one billion dollars in reported victim losses, with individual losses averaging around $47,000.
The group primarily runs “pig butchering” scams, where victims are manipulated over weeks or months into investing large sums into fake cryptocurrency platforms.
Their catalog of fraudulent portals includes pixel-perfect clones of luxury brands like Tiffany, Cartier, and Chanel, financial platforms like Western Union and MoneyGram, and banking portals falsely tied to Wells Fargo, Goldman Sachs, and Bank of America.
To avoid law enforcement attention after the sanctions, the group also launched a series of “clean” front companies — entities with professional branding and fabricated operating histories designed to manufacture trust among unsuspecting users.
One particularly revealing example is a fake CDN provider operating as cdnbl.com, which falsely claims to have served clients since 2007. Domain registration records confirm it was only created in March 2024, exposing the deception at its core.
Geographic Evasion and the Rotating CNAME Infrastructure
One technically alarming aspect of Triad Nexus’s rebuilt operation is its deliberate use of multi-layered CNAME chains to hide the true destination of its traffic.
A CNAME, or Canonical Name record, is a DNS entry that redirects one domain to another. Standard security tools typically only follow a single step in this chain, meaning the real final endpoint often goes completely undetected.
Triad Nexus actively exploits this blind spot. Its infrastructure routes traffic through multiple intermediate CNAME domains — sometimes three or four layers deep — before landing on a final IP address hosted on a reputable enterprise cloud platform.
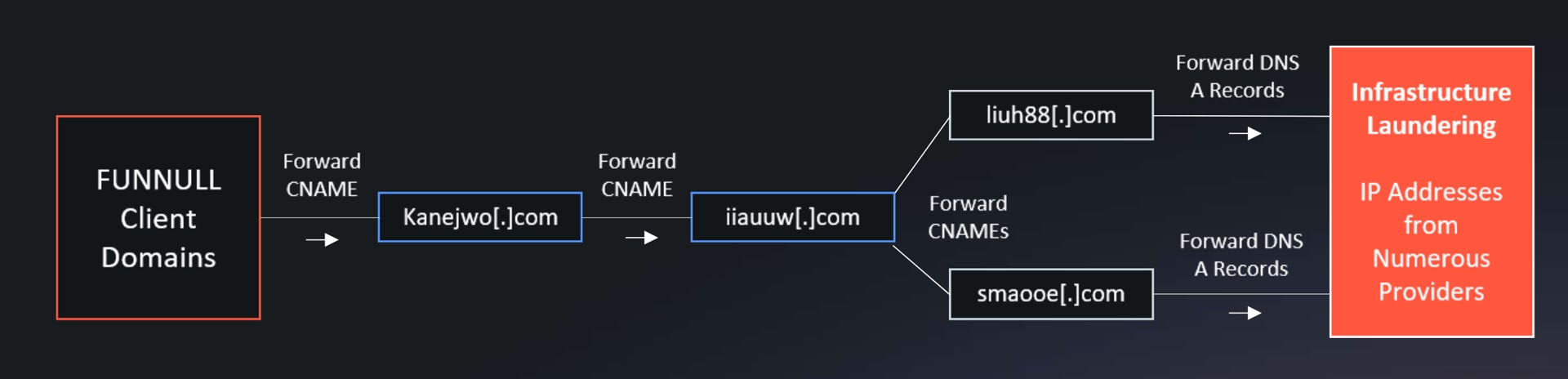
This multi-layered redirection makes it extremely difficult for automated detection tools to trace traffic back to its true origin.
To further avoid oversight, the group has placed a deliberate U.S. block across many of its portals, displaying an error that reads “The region has been denied” to American visitors, while simultaneously expanding its scam operations into Spanish, Vietnamese, and Indonesian markets to keep its fraud profits flowing.
Organizations are strongly advised to move beyond reactive security measures. Security teams should adopt CNAME chain analysis capabilities, monitor for newly registered lookalike domains, enforce strict DNS resolution policies, and maintain deep visibility across all network layers to detect and disrupt threats of this nature before they reach end users.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.