FortiClient EMS Exposed: RCE Vulnerability Explo Instances Online
The Shadowserver Foundation has issued an urgent warning for FortiClient Enterprise Management Server (EMS) administrators. This alert follows the identification of over 2,000 publicly accessible EMS...
The Shadowserver Foundation has issued an urgent warning for FortiClient Enterprise Management Server (EMS) administrators. This alert follows the identification of over 2,000 publicly accessible EMS instances globally, with two now confirmed as actively exploited. These attacks leverage critical unauthenticated remote code execution (RCE) vulnerabilities.
Two vulnerabilities, CVE-2026-35616 and CVE-2026-21643, both classified as unauthenticated RCE flaws, were exploited in the wild, affecting Fortinet’s FortiClient EMS platform.
CVE-2026-35616 is a newly disclosed vulnerability, while CVE-2026-21643 has been under scrutiny in recent weeks. Critically, both are now confirmed as exploited in the wild, meaning threat actors are actively leveraging them against unpatched deployments without requiring any credentials.
Unauthenticated RCE vulnerabilities are among the most severe classes of security flaws. An attacker can remotely execute arbitrary code on a vulnerable server without needing a username or password, potentially gaining full control over the affected system and the endpoints it manages.
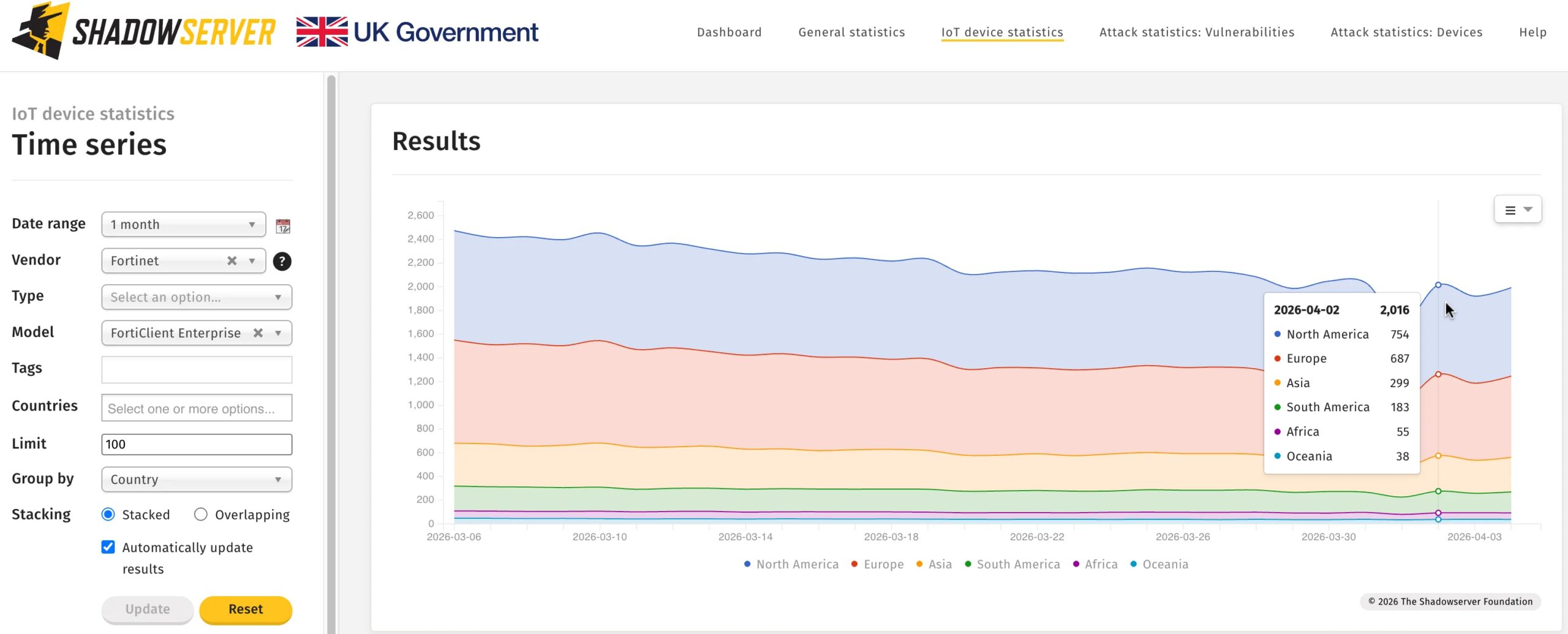
Scale of Exposure: 2,000 Instances Globally
Using its global sensor network, Shadowserver fingerprinted approximately 2,000 FortiClient EMS instances exposed to the public internet. The United States and Germany top the list of affected countries, according to Shadowserver’s public dashboard data.
Given that FortiClient EMS is an enterprise endpoint management solution used to centrally manage Fortinet VPN clients and security policies across large organizations, this exposure carries significant implications for corporate networks.
A compromised EMS server could allow attackers to manipulate endpoint configurations, push malicious policy updates, harvest VPN credentials, and establish persistent footholds across an organization’s entire endpoint fleet.
This latest alert is consistent with a broader trend of threat actors targeting Fortinet infrastructure. Fortinet products have repeatedly appeared in CISA’s Known Exploited Vulnerabilities (KEV) catalog, and nation-state groups alongside ransomware operators have historically prioritized Fortinet flaws for initial access into enterprise environments.
Mitigations
Organizations running FortiClient EMS should take the following steps immediately:
- Apply patches released by Fortinet addressing CVE-2026-35616 and CVE-2026-21643 without delay
- Restrict internet-facing access to the EMS management interface using firewall rules or VPN-gated access
- Review logs for anomalous activity, unauthorized configuration changes, or unexpected outbound connections
- Monitor Shadowserver’s dashboard for ongoing exposure intelligence related to your network ranges
- Enable threat detection alerts through your SIEM or EDR platform for indicators associated with these CVEs
Fortinet has urged customers to consult its official security advisories and upgrade to patched firmware versions immediately. Given confirmed in-the-wild exploitation, delayed remediation is not an option.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.