F5 BIG-IP APM Devices Exposed to Active R Online Amid
Active exploitation of a critical security flaw in F5’s BIG-IP Access Policy Manager (APM) now threatens thousands of enterprise networks. The vulnerability, officially tracked as...
Active exploitation of a critical security flaw in F5’s BIG-IP Access Policy Manager (APM) now threatens thousands of enterprise networks.
The vulnerability, officially tracked as CVE-2025-53521, has sparked urgent warnings across the cybersecurity community after its impact was upgraded from a standard Denial-of-Service (DoS) to a severe Remote Code Execution (RCE) flaw.
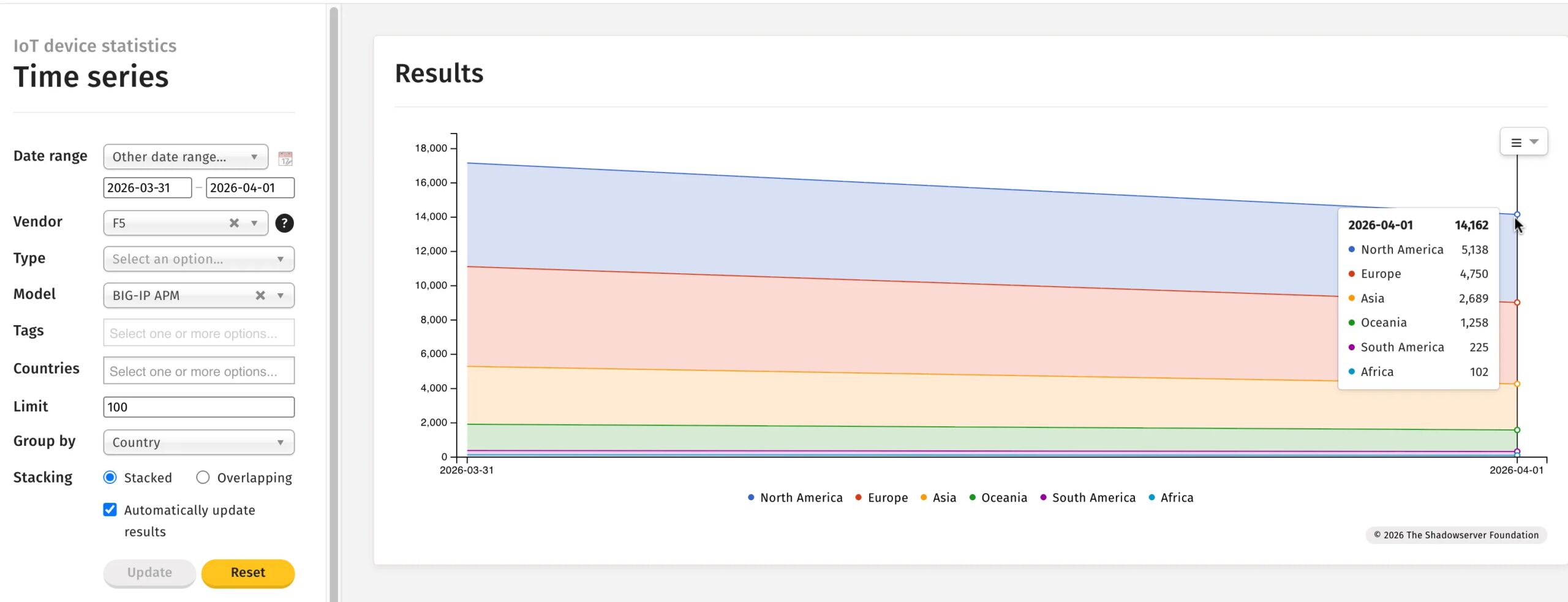
CISA added the flaw to its KEV catalog, requiring immediate action and urging others to follow. Telemetry data provided by The Shadowserver Foundation reveals a massive attack surface. On March 31, 2026, researchers fingerprinted over 17,100 exposed F5 BIG-IP APM instances globally.
While some organizations have begun applying fixes, more than 14,000 systems remain completely exposed to the public internet.
According to Shadowserver’s device identification mapping, the United States and Japan currently hold the highest concentration of vulnerable instances.
Because BIG-IP APM acts as a secure gateway for enterprise application access, a successful compromise allows attackers to bypass corporate perimeters and directly infiltrate internal networks.
The Danger of a Delayed Patch
The primary reason for such widespread exposure stems from the vulnerability’s initial classification.
When F5 first disclosed CVE-2025-53521, it was rated strictly as a DoS issue. In many enterprise environments, DoS vulnerabilities are assigned a lower priority during patch management cycles than direct intrusion threats.
Security researchers at VulnTracker noted that many IT teams likely skipped this patch the first time around to prioritize more critical alerts.
Now that threat actors have discovered how to weaponize the flaw to execute arbitrary remote code, those delayed patches have become a critical liability.
An attacker exploiting this RCE can take full control of the F5 appliance, leading to data theft, ransomware deployment, or deep network persistence.
Organizations running F5 BIG-IP APM services must treat this as a critical, “patch-now” event. Security teams should take the following steps:
- Apply Vendor Updates: Immediately review F5’s updated security advisory (K000156741) and upgrade all BIG-IP APM instances to the latest patched software versions.
- Assume Breach and Hunt: Because this vulnerability is actively exploited in the wild, simply patching the system is no longer enough. Administrators must thoroughly review system logs and actively hunt for indicators of compromise (IoCs).
- Audit External Assets: Use network monitoring tools to ensure all internet-facing APM interfaces are identified, secured, and properly configured.
The rapid escalation of CVE-2025-53521 from a manageable DoS to an actively exploited RCE serves as a stark reminder of how quickly the modern threat landscape can shift.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.