Exposed Ollama Hosts Allow Code Execution & System Access
A recent security discovery highlights a critical exposure: approximately 175,000 Ollama servers are publicly accessible across the internet. This poses a serious risk, enabling widespread code...
A recent security discovery highlights a critical exposure: approximately 175,000 Ollama servers are publicly accessible across the internet. This poses a serious risk, enabling widespread code execution and unauthorized access to external systems.
Ollama, an open-source framework designed to run artificial intelligence models locally, has become unexpectedly exposed due to simple configuration changes that administrators make without fully understanding the security implications.
Researchers have documented how these internet-facing servers can be manipulated to execute arbitrary code and interact with sensitive resources, fundamentally changing how organizations must think about AI infrastructure security.
The exposure stems from a critical oversight in deployment practices. By default, Ollama binds to a local-only address, making it inaccessible from the internet.
However, changing just a single configuration setting—binding the service to 0.0.0.0 or a public-facing interface—transforms these isolated systems into internet-accessible targets.
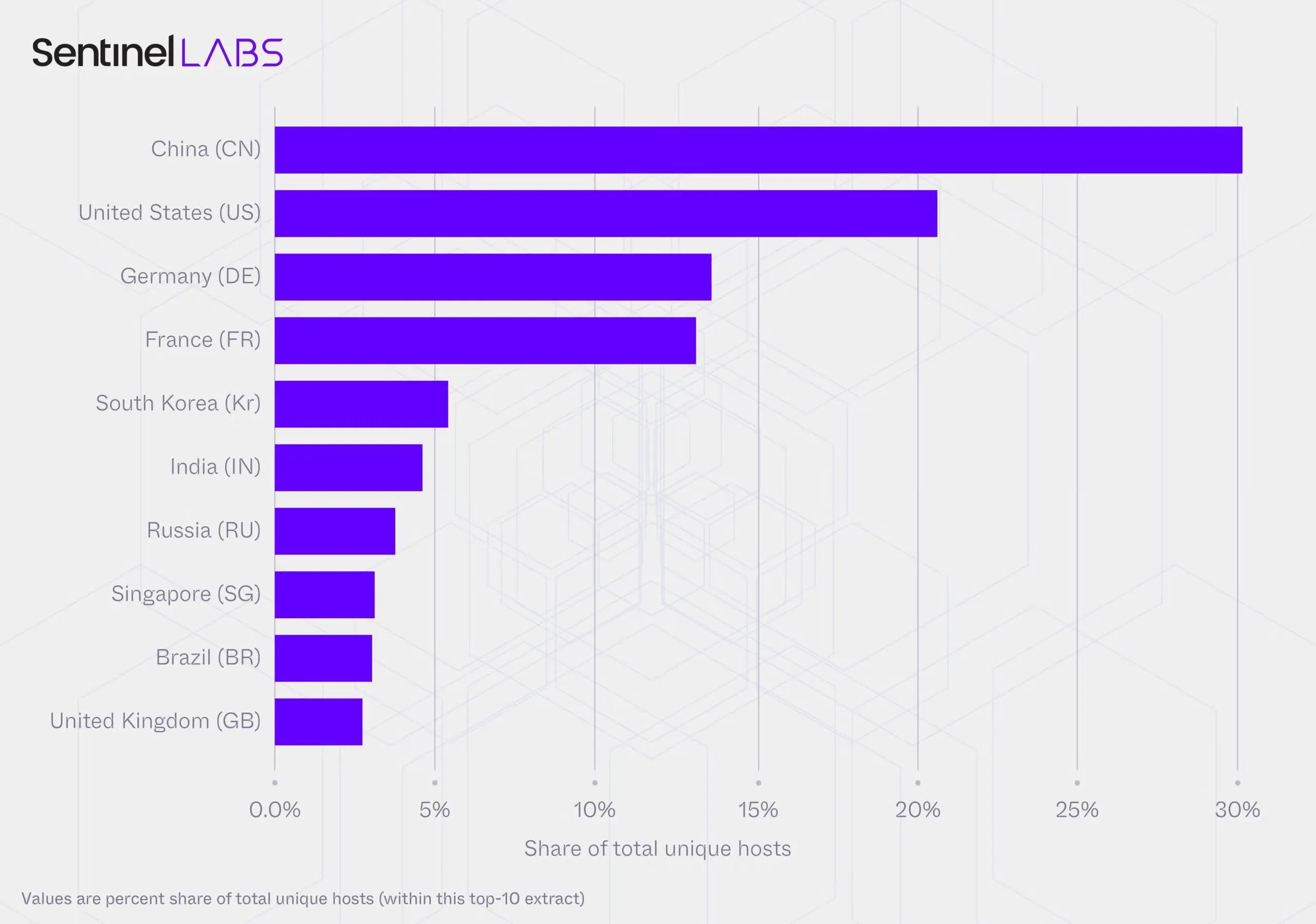
As open-source AI models became more widespread throughout 2025, this misconfiguration pattern emerged at massive scale, with deployments spanning 130 countries and 4,032 autonomous system networks.
SentinelLABS analysts identified the threat landscape through a comprehensive 293-day scanning operation conducted in partnership with Censys.
Their research uncovered 7.23 million observations from these exposed hosts, revealing both the scope of the vulnerability and its potential for exploitation.
The discovered infrastructure represents a critical weak point in how organizations deploy and manage artificial intelligence systems without adequate security controls.
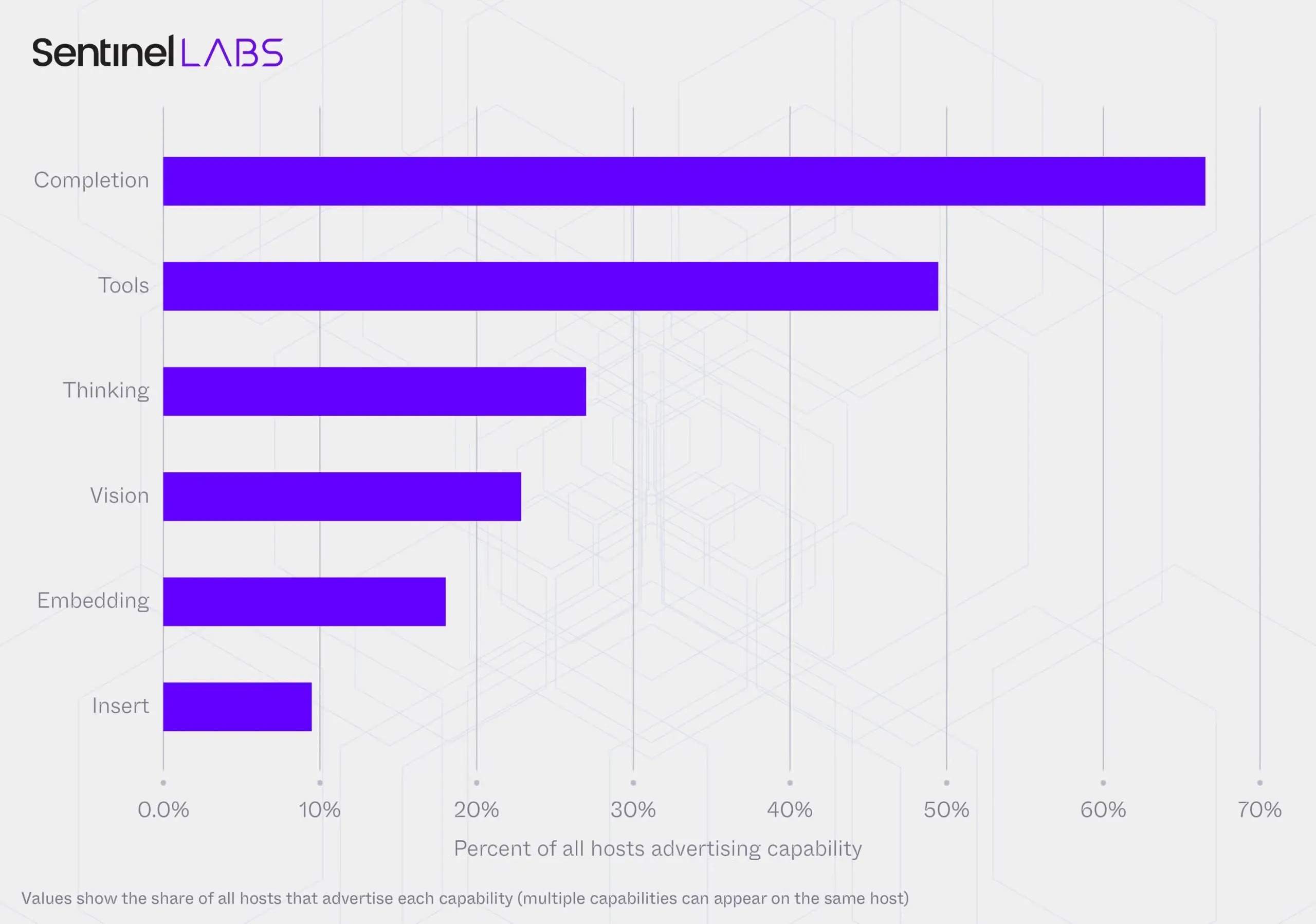
The most alarming finding involves tool-calling capabilities embedded in nearly half of all exposed hosts.
These capabilities allow the systems to execute code, access application programming interfaces, and interact with external infrastructure.
Approximately 38 percent of observed hosts display both text completion and tool-execution functions, essentially granting attackers the ability to run commands directly through the artificial intelligence interface.
When combined with insufficient authentication controls, this configuration creates a direct pathway for remote code execution.
Understanding Tool-Calling and Its Dangers
Tool-calling represents one of the most dangerous aspects of the exposed Ollama ecosystem. Unlike traditional text-generation endpoints that simply produce content, tool-enabled systems can perform actions.
An attacker can craft specific prompts designed to trick these artificial intelligence models into executing system commands or accessing files without the server owner’s knowledge.
This technique, called prompt injection, becomes particularly powerful when targeting systems running retrieval-augmented generation deployments, which search through databases and documentation to answer questions.
The security risk multiplies when considering that 22 percent of exposed hosts feature vision capabilities, allowing them to analyze images and documents.
An attacker could embed malicious instructions within image files, creating indirect prompt injection attacks that bypass traditional security defenses.
Combined with tool-calling functionality, an exposed Ollama instance becomes a versatile platform for executing virtually any malicious operation.
Furthermore, 26 percent of hosts run reasoning-optimized models that can break complex tasks into sequential steps, providing attackers with sophisticated planning capabilities for multi-stage attacks.
This convergence of capabilities transforms isolated configuration mistakes into a unified threat infrastructure that criminal organizations and state-sponsored actors can exploit at scale. The concentration risk extends beyond individual system compromise.
Approximately 48 percent of exposed hosts run identical quantization formats and model families, creating what researchers describe as a monoculture—a brittle ecosystem where a single vulnerability could simultaneously affect thousands of systems.
This structural weakness means defenders cannot rely on diversity to limit the blast radius of discovered exploits.
When a single implementation flaw exists in a widely deployed model format, the consequences ripple across the entire exposed ecosystem rather than remaining isolated incidents.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.