DPRK’s Remote Workers Generating $600M Using Identity Theft to
In recent years, the cybersecurity landscape has fundamentally shifted, driven by the evolving definition of insider threats. For decades, organizations focused their security efforts on detecting...
In recent years, the cybersecurity landscape has fundamentally shifted, driven by the evolving definition of insider threats.
For decades, organizations focused their security efforts on detecting disgruntled employees or negligent contractors who might compromise sensitive data.
Today, the most dangerous insider threat is often an operative hired under false pretenses, working to siphon company funds, steal intellectual property, and establish backdoors for state-sponsored actors.
This transformation reflects the changing nature of cyber operations, particularly those orchestrated by the Democratic People’s Republic of Korea.
The DPRK operates a sophisticated remote worker program that UN experts and law enforcement agencies estimate generates approximately $600 million annually for the North Korean regime.
These operatives use advanced identity theft techniques to secure high-paying remote positions at Western enterprises. Silent Push analysts and researchers identified that the DPRK typically employs two distinct operational variants to infiltrate organizations.
The first variant involves placing long-term infiltrators who secure legitimate IT roles, sometimes working normally for months while establishing persistent access and generating revenue.
The second variant uses fake front companies that mimic legitimate software firms to lure skilled professionals into interviews designed to compromise their security through malicious code execution.
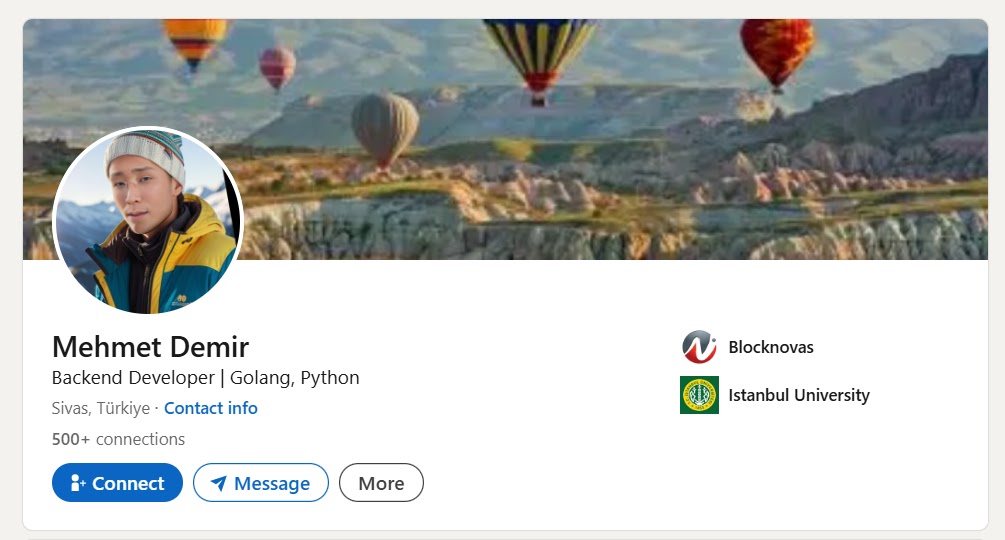
The Identity Verification Trap represents a critical vulnerability in corporate hiring processes. Traditional security systems verify identities based on credentials alone.
AI-driven deepfake technology
When candidates provide valid Social Security Numbers, pass third-party background checks, and clear video interviews using AI-driven deepfake technology, they gain system access.
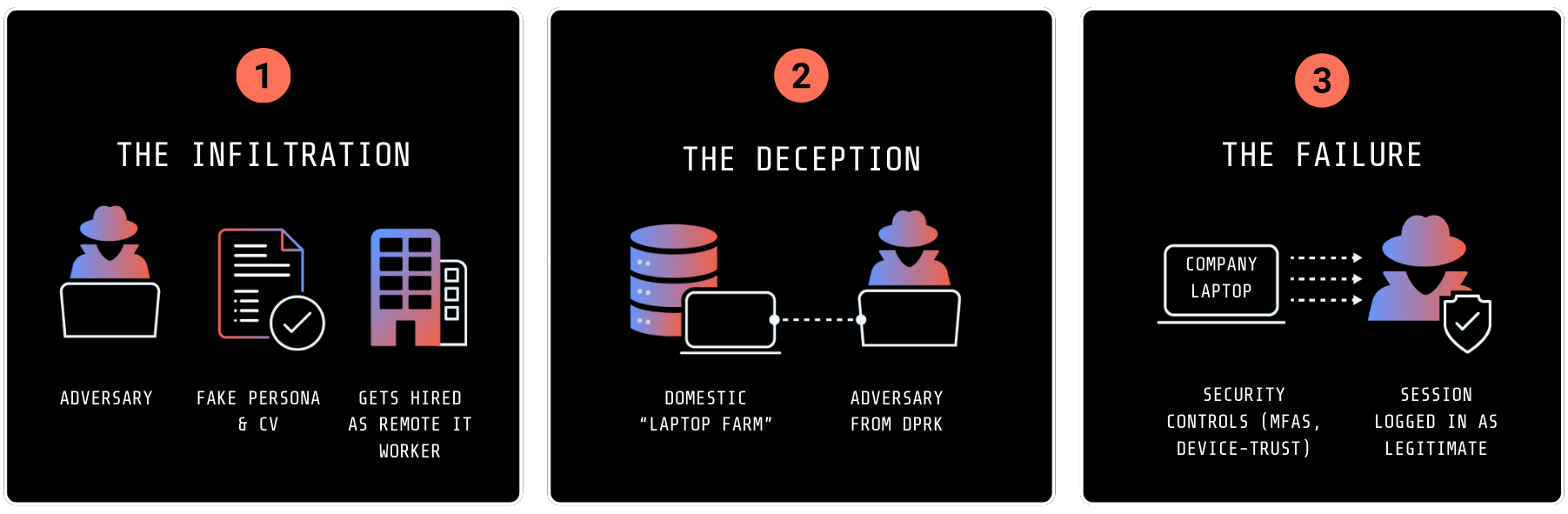
However, once onboarded, these operatives create a false local employee footprint using Western residential IP addresses to appear as legitimate remote workers from suburban locations.
Security teams commonly rely on IP geolocation and geofencing to detect suspicious activities. However, DPRK operatives bypass these controls through multi-layered proxy chains that route traffic through physical devices located within the United States.
This sophisticated approach creates three critical visibility gaps: the residential IP fallacy that makes datacenter traffic appear legitimate, the background check gap where verification targets stolen identities rather than the actual person, and the hardware authenticity trap where real laptop farms pass MAC address checks and device security assessments that virtual systems cannot.
The consequences of hiring DPRK operatives extend beyond immediate security concerns.
Organizations face potential OFAC sanctions violations, irreversible intellectual property loss, and costly incident response operations requiring complete infrastructure audits.
Protecting against these threats requires organizations to move beyond traditional background checks and verify that remote employees are physically located where they claim to be, implementing advanced network traffic analysis to identify suspicious connection patterns before threats gain access to sensitive systems.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.