DarkSpectre Malware Infected 8.8M Hackers Million Chrome
Malware Infected 8.8M Hackers Million Chrome
Okay, so here’s something pretty wild. Researchers have just uncovered a major player called DarkSpectre – they’re a well-funded Chinese threat actor, and get this, they’ve been behind a massive operation for seven years straight. We’re talking about highly coordinated malware campaigns that managed to infect over 8.8 million users across Chrome, Edge, and Firefox browsers.
The discovery reveals a level of operational sophistication rarely seen in the threat landscape, with the group running multiple distinct campaigns simultaneously, each targeting different objectives ranging from consumer fraud to corporate espionage.
The operation consists of three major campaigns: ShadyPanda affecting 5.6 million users, the newly discovered Zoom Stealer campaign targeting 2.2 million users, and GhostPoster impacting 1.05 million users.
Rather than operating as separate threat actors, investigators confirmed these represent a single, highly organized criminal organization with substantial resources and strategic planning capabilities.
The group demonstrates remarkable patience, maintaining legitimate-appearing browser extensions for five or more years before weaponizing them with malicious payloads.
Koi analysts identified the connection between these campaigns while analyzing infrastructure linked to ShadyPanda.
They discovered that while the group used two legitimate domains—infinitynewtab.com and infinitytab.com—to power actual extension features like weather widgets and new tab pages, these same domains connected to entirely different malicious command-and-control infrastructure.
This clever technique of embedding legitimate functionality alongside hidden malicious code became the thread linking all three operations together.
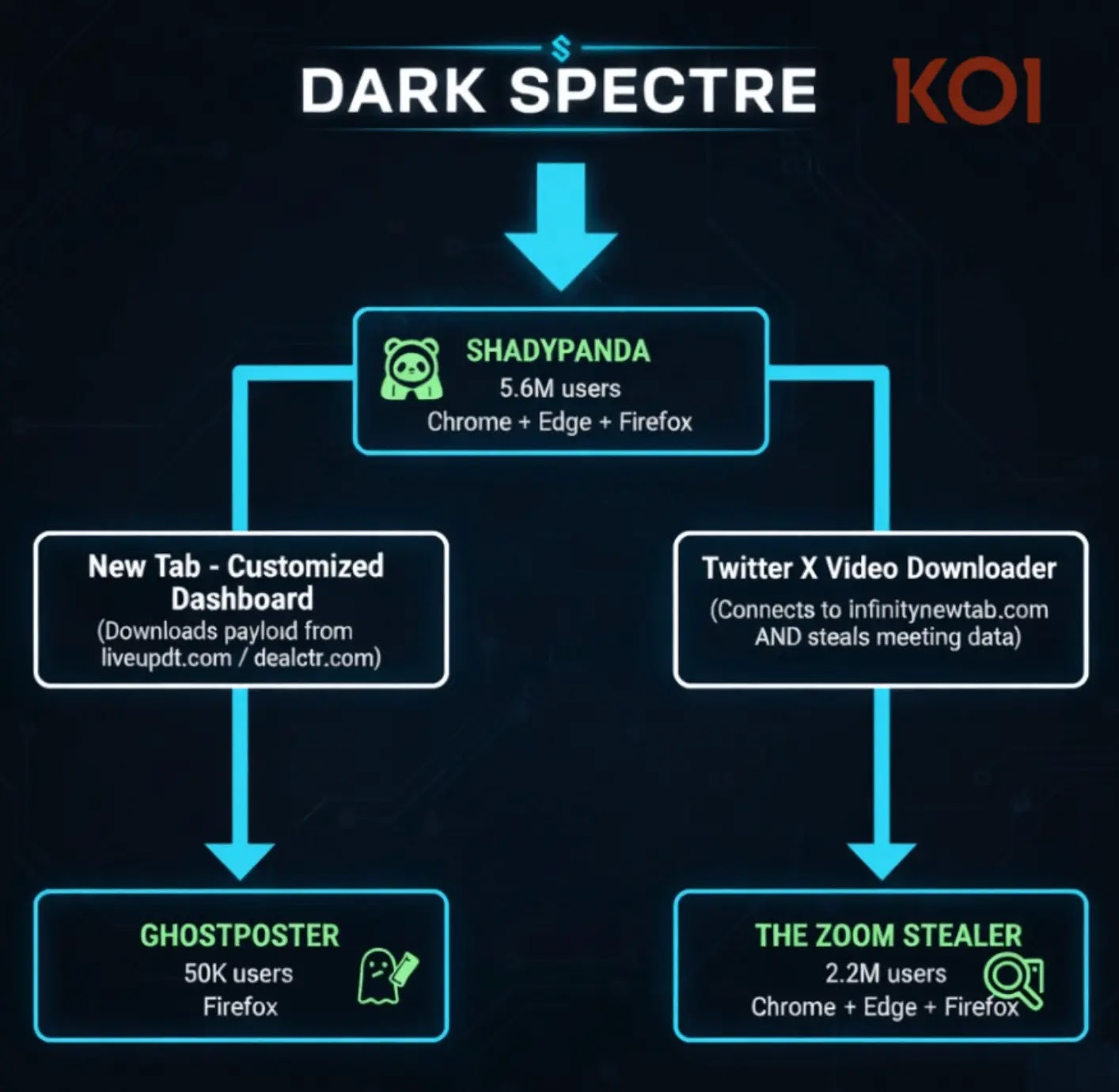
The discovery process resembled following a complex web. One domain led to extensions, which revealed new domains, which connected to additional extensions operated by publishers with dozens of other malicious tools.
The expansion eventually uncovered over 100 connected extensions across multiple browser marketplaces.
As researchers investigated further, they noticed that certain newly discovered extensions communicated with domains already flagged in previous investigations, confirming that ShadyPanda, GhostPoster, and Zoom Stealer represented a single actor operating at nation-state scale.
Time-Bomb Activation and Evasion Tactics
The most alarming aspect of DarkSpectre’s methodology lies in their sophisticated persistence and detection-evasion techniques.
The group employs what researchers term “time-bomb” extensions—malicious tools that remain dormant for extended periods before activating their payload.
One extension called “New Tab – Customized Dashboard” demonstrates this approach by waiting three days after installation before connecting to command-and-control servers to download its actual malicious code.
During the review process when marketplaces evaluate extensions for safety, this extension appears completely legitimate. Browser reviewers cannot detect the malicious behavior because it simply does not activate during testing.
The extension only begins its malicious activities after passing all security checks and reaching a real user’s browser.
To further evade detection, the malware only activates on approximately ten percent of page loads, making it exponentially harder to identify during routine testing or analysis.
The payload delivery itself showcases advanced obfuscation techniques. DarkSpectre disguises malicious code as PNG image files, a method known as steganography.
The extension loads its own logo, extracts the hidden JavaScript code embedded within the image file, and executes it silently in the background.
The JavaScript is wrapped in multiple layers of protection including custom encoding, XOR encryption, and packed code designed specifically to defeat automated detection tools.
Once activated, the extension downloads approximately sixty-seven kilobytes of additional encoded JavaScript from the operators’ servers, giving the threat actors complete control over what executes in the user’s browser without requiring an extension update that would again trigger the review process.
This configuration-based approach represents the true innovation in DarkSpectre’s operation. Instead of pushing updates to change functionality—which would alert reviewers and users—the operators simply modify what their servers return when extensions phone home.
Defenders cannot combat the threat by blocking a single malicious update because the threat actor changes the payload on their backend servers dynamically, maintaining complete operational flexibility.









No Comment! Be the first one.