Cursor AI Extension Exposes Dev Tokens, Full Cred Access Developer
A critical access-control vulnerability (CVSS 8.2) has been identified in Cursor, a widely used AI-powered coding environment. This high-severity flaw potentially exposes developer tokens and grants...
A critical access-control vulnerability (CVSS 8.2) has been identified in Cursor, a widely used AI-powered coding environment. This high-severity flaw potentially exposes developer tokens and grants full credential access to affected users.
The flaw uncovered by LayerX has allowed any installed extension to access a developer’s API keys and session tokens secretly.
This results in total credential compromise without triggering any alerts or requiring user interaction.
Unlike secure applications that store sensitive secrets in protected operating system keychains, Cursor saves these credentials in an unprotected, local SQLite database.
The database is located at ~/Library/Application Support/Cursor/User/globalStorage/state.vscdb.
Because Cursor lacks access control boundaries between its extensions and this database, any installed extension can read the file.
No special privileges are required, meaning any rogue add-on can extract the plaintext data stored inside.
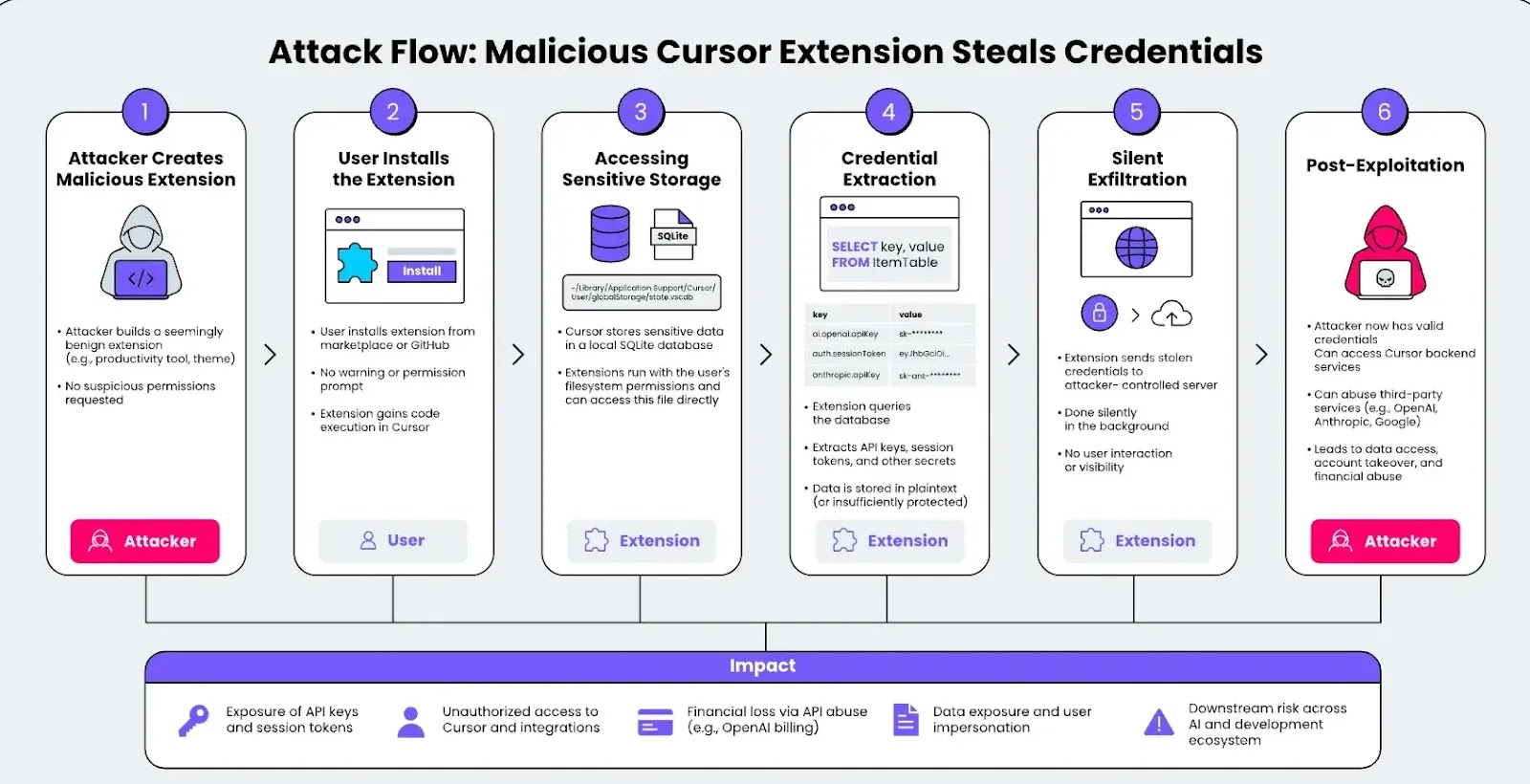
The exploitation process is simple and requires low attack complexity. A realistic attack scenario involves the following steps:
- An attacker publishes a normal-looking extension, such as a custom theme or productivity tool.
- A developer installs the extension without receiving any permission warnings regarding credential access.
- The malicious extension quietly queries the local SQLite database to find API keys and session tokens.
- The stolen data is silently sent to a remote server owned by the attacker without any visible user interface changes.
Since many developers use third-party AI services within Cursor, the fallout from this vulnerability can be severe.
Stolen credentials create a direct path to the following risks:
- Total exposure of session tokens and backend service access.
- Compromise of linked AI accounts such as OpenAI, Google, or Anthropic.
- Massive financial losses if attackers rack up automated usage charges on stolen API keys.
- Unauthorized access to private data, previous chat prompts, and sensitive code metadata.
Vendor Response and Status
LayerX originally reported this issue to Cursor on February 1, 2026. Cursor’s security team acknowledged the report on February 5.
However, it stated that extensions operate within the same local trust boundary as the user.
They argued that any local application with file system access could potentially read this data.
As of April 28, 2026, the vulnerability remains unfixed. The vendor maintains that it is the user’s responsibility only to install trusted extensions.
To properly secure user data, security experts strongly advise Cursor to implement strict isolation boundaries between extensions.
Sensitive credentials must be moved to encrypted, system-level storage, such as the Windows Credential Manager or macOS Keychain.
Until a structural fix is released, developers should rigorously audit their installed extensions and avoid downloading unverified tools from the marketplace.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.