Critical IDIS IP Camera Flaw: One-Click PC Cameras Vulnerability
A critical security vulnerability has been identified in IDIS IP cameras, allowing attackers to gain complete control over a victim’s computer with a single click. The vulnerability, tracked as...
A critical security vulnerability has been identified in IDIS IP cameras, allowing attackers to gain complete control over a victim’s computer with a single click.
The vulnerability, tracked as CVE-2025-12556, targets the IDIS Cloud Manager (ICM) Viewer, a Windows-based application used to monitor surveillance feeds from IDIS IP cameras deployed across enterprises, manufacturing facilities, and military installations worldwide.
With a CVSS score of 8.7, this flaw represents a critical threat that could transform routine surveillance systems into entry points for network-wide breaches.
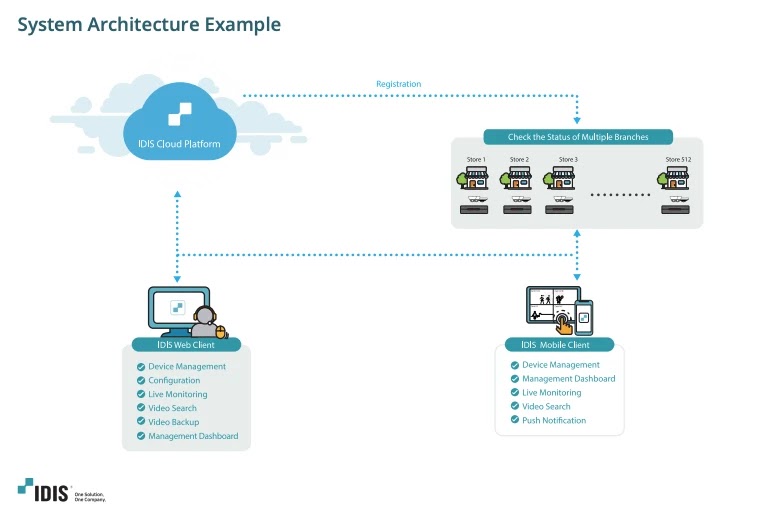
IDIS, a South Korea-based video surveillance manufacturer, provides an integrated cloud management solution that connects IP cameras, network video recorders, and video management software through its ICM platform.
The vulnerability enables threat actors to execute malicious code on the host machine by tricking victims into clicking on a specially crafted link.
While users are typically warned against clicking untrusted links, this security flaw escalates the danger significantly by breaking out of the browser’s protective sandbox and executing code directly on the Windows operating system.
After the second paragraph, Claroty researchers identified the weakness during their investigation into modern cloud-enabled surveillance ecosystems.
Their analysis revealed that the ICM Viewer’s architecture contains multiple security oversights that, when combined, create a dangerous attack pathway.
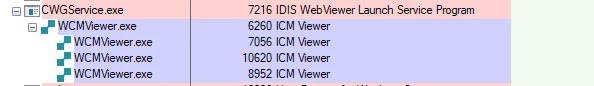
The flaw stems from a Windows service called CWGService.exe, which listens on local port 16140 and accepts commands to launch the ICM Viewer with specific parameters.
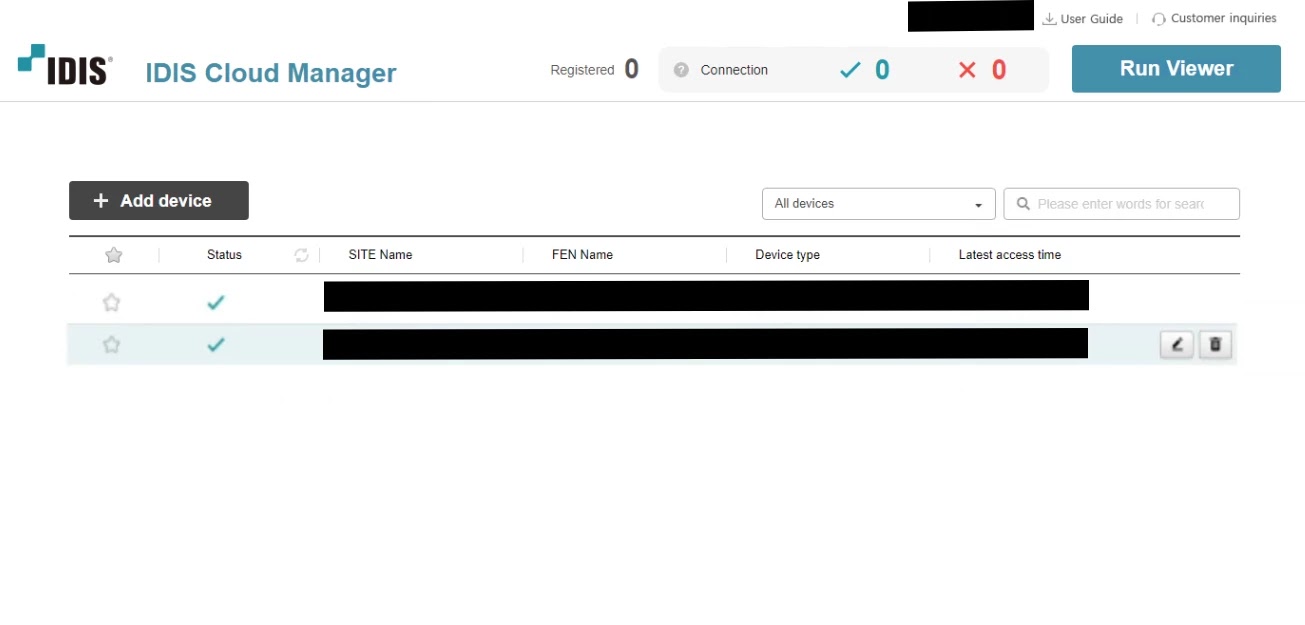
Because this service fails to validate the origin of incoming commands or sanitize input arguments, attackers can inject malicious instructions through a WebSocket connection initiated by JavaScript code on a malicious website.
Once exploited, the vulnerability grants attackers complete access to the compromised system, enabling them to steal sensitive data, install additional malware, or move laterally across the network to target other devices.
This presents a particularly alarming scenario for organizations relying on IDIS surveillance systems, as a single compromised workstation could serve as a springboard for attacks against the broader infrastructure, including surveillance cameras and critical business systems.
Attack Mechanism and Technical Exploitation
The exploitation process leverages a design flaw in how the ICM Viewer processes command-line arguments passed from the CWGService component.
The ICM Viewer is built on the Chromium Embedded Framework (CEF), which accepts various command-line flags to modify browser behavior.
Attackers discovered they could inject the --utility-cmd-prefix debugging flag into the execution chain, allowing them to wrap the viewer’s utility processes with arbitrary commands.
By hosting a malicious webpage containing JavaScript that connects to the local WebSocket service, attackers can send encrypted messages with injected arguments that trigger code execution when an unsuspecting user visits the page.
The attack requires no authentication beyond convincing the victim to click a link, making it particularly effective for spear-phishing campaigns.
Claroty researchers successfully demonstrated the exploit by injecting commands that launched Notepad, proving the concept’s viability for more malicious payloads.
CISA has issued an advisory urging all IDIS ICM Viewer users to immediately upgrade to version 1.7.1 or uninstall the software if not in use.
Organizations must act swiftly to patch their systems, as the combination of high severity and ease of exploitation makes this vulnerability an attractive target for threat actors seeking network access through IoT devices.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.