Chinese Hackers Use NFC Android Malware to Ste Deploy NFC-enabled
Chinese threat actors have launched a sophisticated campaign using NFC Android Malware called Ghost Tap to intercept and steal financial information from victims worldwide. The malware operates...
Chinese threat actors have launched a sophisticated campaign using NFC Android Malware called Ghost Tap to intercept and steal financial information from victims worldwide.
The malware operates through a deceptive distribution model, where attackers trick users into downloading seemingly legitimate applications via Telegram and other messaging platforms.
Once installed, Ghost Tap leverages Near Field Communication technology to read payment card data when victims unknowingly tap their cards against infected devices, silently capturing sensitive information without user awareness.
The attack chain relies heavily on social engineering tactics to maximize infection rates. Attackers craft convincing lures disguised as popular applications, gaming software, or utility tools to lower users’ guard and encourage downloads.
The malware then requests permission to access NFC functionality, which most users grant without understanding the security implications.
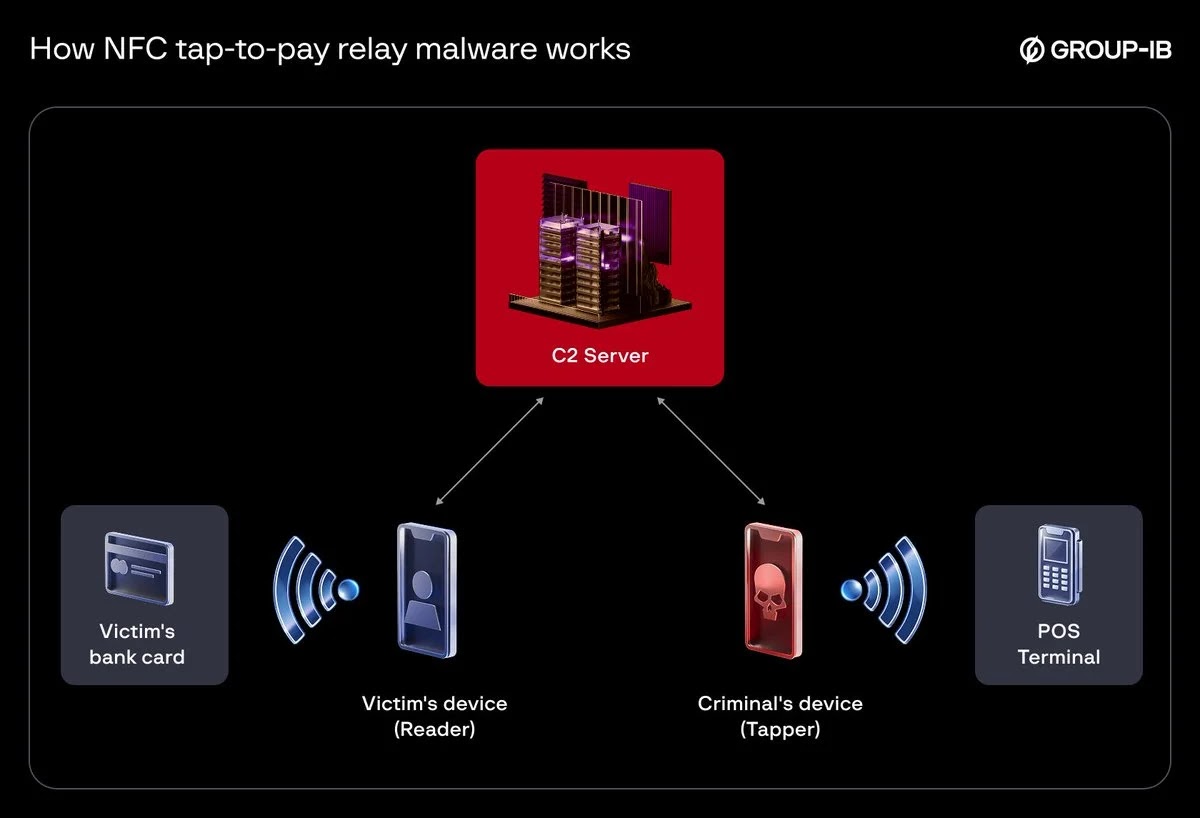
Once activated, Ghost Tap operates in the background, continuously monitoring for NFC card interactions and transmitting stolen data through remote servers controlled by the threat actors.
Group-IB Threat Intelligence researchers identified the campaign after tracking over 54 unique Ghost Tap samples circulating across multiple distribution channels.
The researchers noted that many variants impersonate legitimate applications from well-known companies, making detection more challenging for average users.
Their analysis revealed that fraudsters use the intercepted payment data to conduct unauthorized transactions through illicit point-of-sale terminals, with victims reporting financial losses across multiple countries.
Persistence mechanism
The malware’s persistence mechanism represents a particularly concerning technical aspect of this threat. Ghost Tap employs advanced evasion techniques to maintain its presence on infected devices even after users attempt to uninstall applications.
The malware registers itself as a system service and hooks into Android’s NFC framework at a deep level, allowing it to operate independently from the parent application.
When a user attempts deletion, Ghost Tap automatically reinstalls itself by leveraging compromised system processes, making removal extremely difficult without technical expertise or specialized security tools.
Security researchers recommend users exercise extreme caution when installing applications from untrusted sources and verify app authenticity through official application stores only.
Disabling NFC functionality when not in use provides additional protection against these attacks.
Organizations should implement mobile device management solutions to monitor and block suspicious applications, while users must remain vigilant about granting permissions to installed software.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.