APT Hackers Attack Indian Govt with GOGITTER & Attacking Government
Advanced Persistent Threat (APT) actors operating from Pakistan have launched coordinated attacks against Indian government organizations, deploying newly discovered tools and malware specifically...
Advanced Persistent Threat (APT) actors operating from Pakistan have launched coordinated attacks against Indian government organizations, deploying newly discovered tools and malware specifically designed to bypass security defenses.
The campaign, identified as Gopher Strike, emerged in September 2025 and represents a significant escalation in targeted cyber operations against sensitive government infrastructure.
This coordinated assault demonstrates the growing sophistication of state-sponsored threat actors who continue refining their technical capabilities and operational procedures.
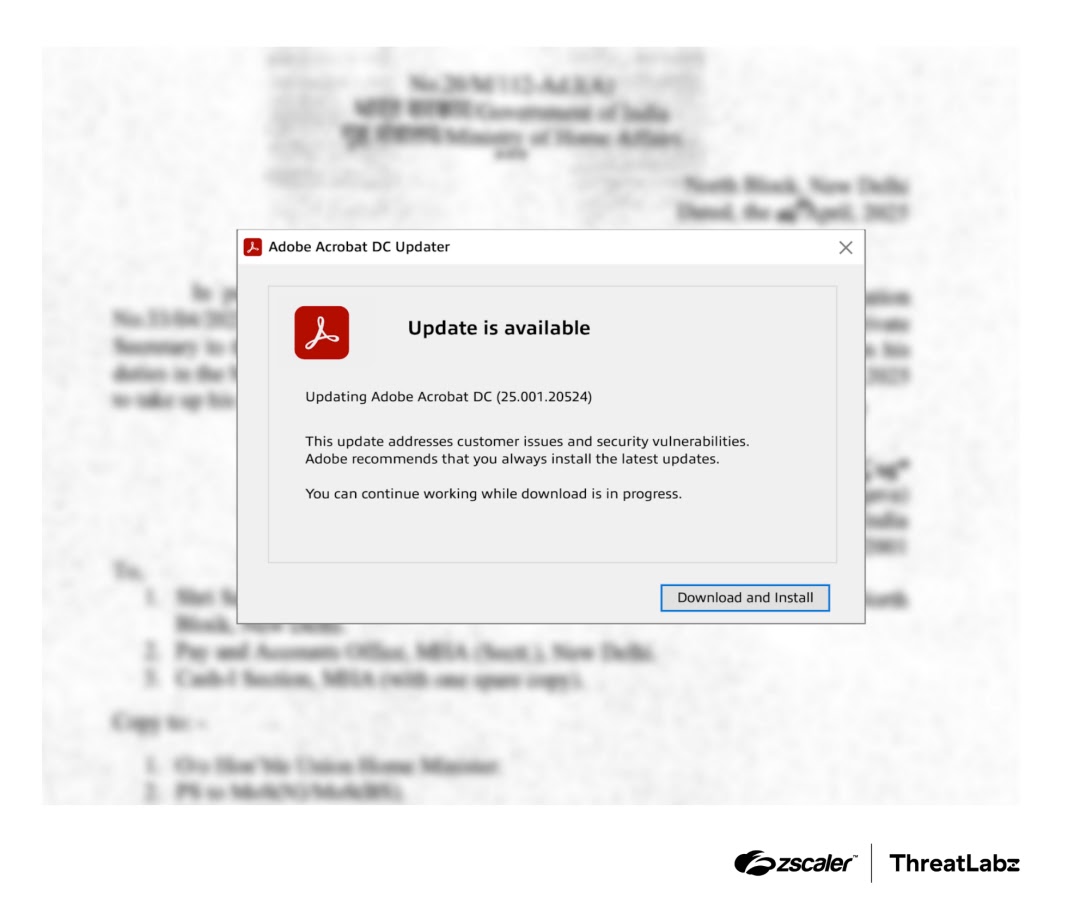
The attack chain begins with carefully crafted phishing emails containing deceptive PDF documents that impersonate legitimate government communications.
These PDFs display blurred images of official documents and use social engineering tactics to trick recipients into downloading an ISO file by clicking a button labeled “Download and Install,” which appears to request a fake Adobe Acrobat update.
The malicious ISO file remains dormant until activated, containing hidden malware designed to establish persistent access to compromised systems.
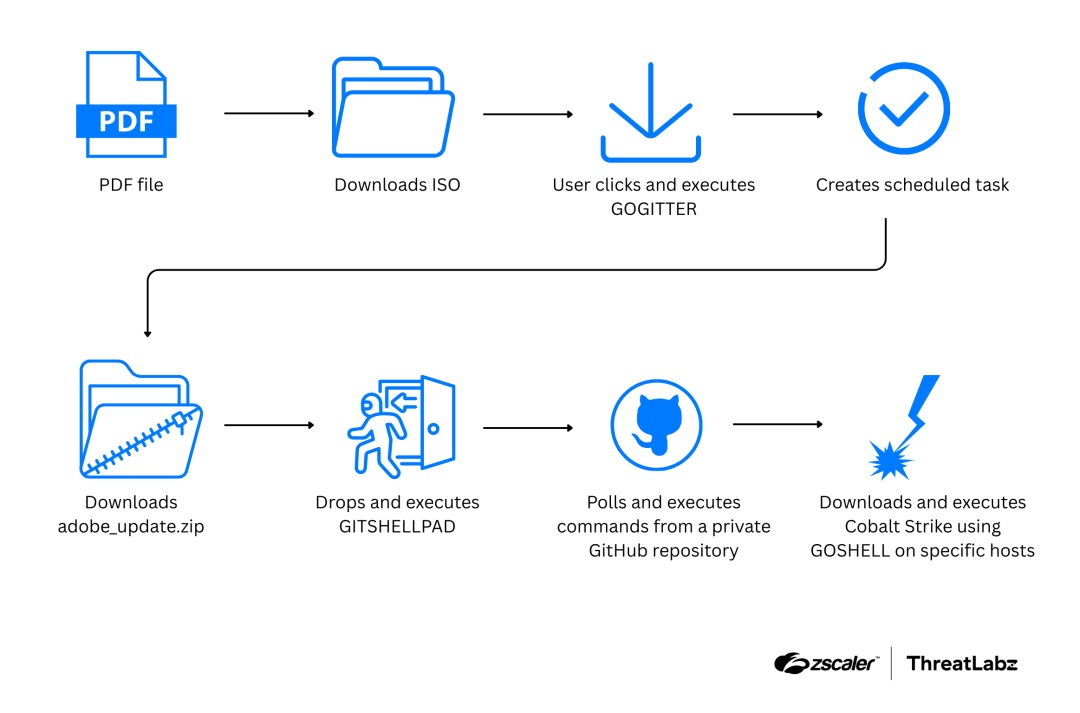
The infection mechanism relies on three custom-built tools written in Golang that work in concert to establish control over targeted machines.
Zscaler analysts and researchers identified GOGITTER as the initial downloader component that fetches additional payloads from threat actor-controlled GitHub repositories using embedded authentication tokens.
Once deployed, GOGITTER creates a VBScript file called windows_api.vbs that continuously polls command-and-control servers every 30 seconds, checking for new instructions to execute on the infected machine.
GITSHELLPAD’s Innovative GitHub-Based Persistence Mechanism
GITSHELLPAD represents the campaign’s most distinctive element, functioning as a lightweight backdoor that leverages private GitHub repositories for all command-and-control communication.
This approach allows the threat actor to hide malicious traffic within legitimate-looking GitHub activity, making detection significantly more difficult for security monitoring tools.
Upon infection, GITSHELLPAD registers the victim by creating a new directory in the threat actor’s private repository using the format SYSTEM-[hostname], then adds an info.txt file containing Base64-encoded system information about the compromised machine.
The backdoor polls GitHub’s API every 15 seconds for new instructions stored in a command.txt file, allowing operators to remotely execute reconnaissance commands, download additional tools, or stage further malware deployments.
This design proves particularly effective because it avoids traditional network indicators while maintaining reliable two-way communication through a service millions of organizations already trust and whitelist for legitimate development purposes.
The final stage involves deploying Cobalt Strike Beacon through GOSHELL, a custom shellcode loader that executes only on machines with specific hardcoded hostnames, further restricting the payload to intended targets.
Security researchers continue tracking this evolving threat to protect government networks against future attacks.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.