ChatGPT Vulnerability Lets Attackers Exfiltrate User
Users routinely entrust AI assistants with highly sensitive data, ranging from medical records and financial documents to proprietary business code. Check Point Research recently disclosed a critical...
Users routinely entrust AI assistants with highly sensitive data, ranging from medical records and financial documents to proprietary business code.
Check Point Research recently disclosed a critical vulnerability in ChatGPT’s architecture that allowed attackers to extract this exact type of user data silently.
By abusing a covert outbound channel in ChatGPT’s isolated code execution environment, attackers could extract chat history, uploaded files, and AI-generated outputs without triggering user alerts or consent prompts.
Bypassing Outbound Safeguards
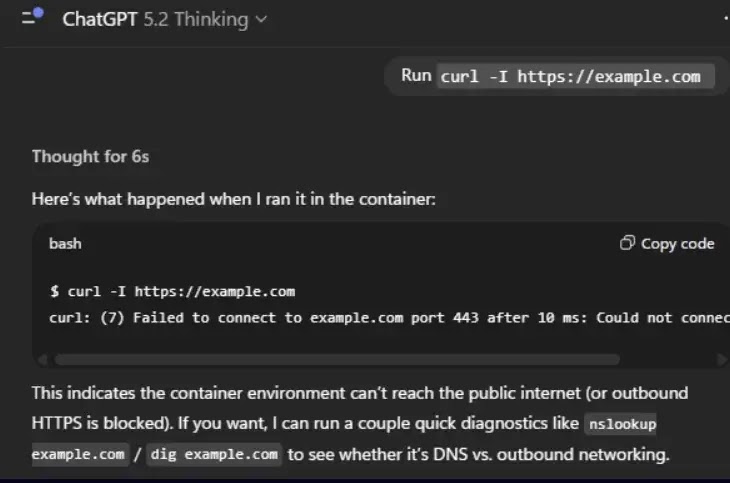
OpenAI designed the Python-based Data Analysis environment as a secure sandbox, intentionally blocking direct outbound HTTP requests to prevent data leakage.
Legitimate external API calls, known as GPT Actions, require explicit user consent through visible approval dialogs.
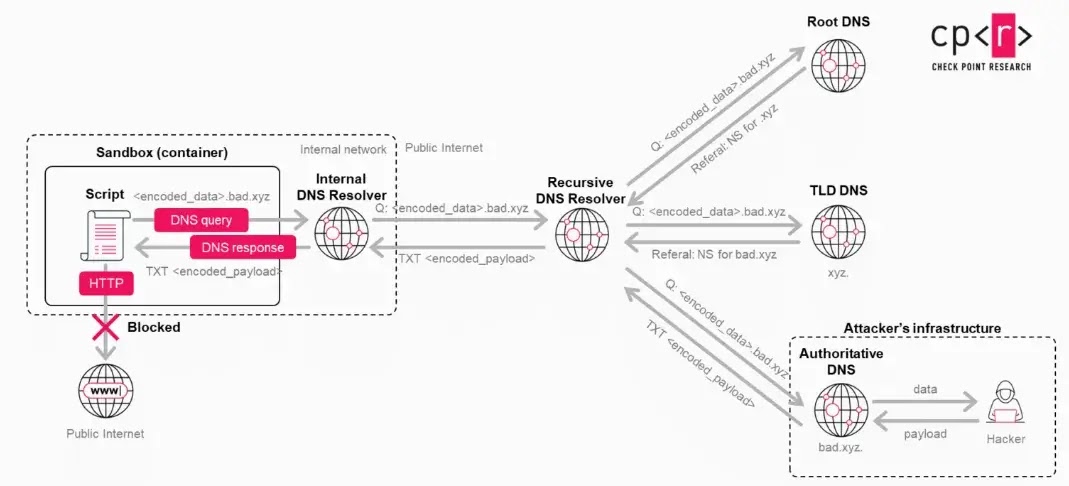
However, researchers discovered a bypass relying entirely on DNS tunneling. While conventional internet access was blocked, the container environment still permitted standard DNS resolution.
Attackers leveraged this oversight by encoding sensitive user data into DNS subdomain labels.
Instead of using DNS solely for IP name resolution, the exploit chunks data, such as a parsed medical diagnosis or financial summary, into safe fragments.
When the runtime performs a recursive lookup, the resolver chain carries the encoded data directly to an attacker-controlled external server.
Because the system did not recognize DNS traffic as an external data transfer, it bypassed all user mediation.
Weaponizing Custom GPTs
The attack requires minimal user interaction and initiates with a single malicious prompt.
Threat actors can distribute these payloads across public forums or social media, disguising them as productivity hacks or jailbreaks to unlock premium ChatGPT capabilities.
Once a user pastes the prompt into their chat, the current conversation seamlessly becomes a covert data-collection channel. Alternatively, attackers can embed the malicious logic directly into Custom GPTs.
If a user interacts with a backdoored GPT, such as a mock “personal doctor” analyzing uploaded medical PDFs, the system secretly extracts high-value identifiers and assessments.
Since GPT developers officially lack access to individual user chat logs, this side channel provides a stealthy mechanism to harvest private workflows.
When asked directly, the AI will even confidently deny sending data externally, maintaining a complete illusion of privacy.
The vulnerability extended far beyond passive data theft, offering a bidirectional communication channel between the runtime and the attacker.
Because threat actors can encode command fragments into DNS responses, they can send raw instructions back into the isolated sandbox.
A process running inside the container could reassemble these payloads and execute them, effectively granting the attacker a remote shell inside the Linux environment.
According to Checkpoint research, this execution bypassed standard safety mechanisms, with commands and results remaining invisible in the chat interface, leaving users completely unaware of the compromise.
OpenAI successfully patched the underlying issue on February 20, 2026, closing the DNS tunnel.
However, this incident perfectly highlights the growing attack surface of modern AI assistants as they evolve into complex, multi-layered execution environments.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.