Attackers Hijack 200+ Sites via Magento Hijacked Websites
Exploiting a severe authentication flaw, threat actors have achieved complete system control over multiple Magento e-commerce platforms worldwide. This critical security breach has exposed numerous...
Exploiting a severe authentication flaw, threat actors have achieved complete system control over multiple Magento e-commerce platforms worldwide. This critical security breach has exposed numerous sites globally.
The attack campaign, identified in January 2026, represents one of the most significant waves of coordinated web server compromises in recent months, affecting hundreds of online stores across different regions and industries.
The vulnerability at the center of this attack is CVE-2025-54236, also known as SessionReaper, which allows unauthorized access by reusing session tokens that were not properly invalidated by the Magento application.
These session tokens function like digital keys that verify a user’s identity.

When Magento fails to destroy these keys after users log out, attackers can intercept and replay them to gain access as legitimate administrators, bypassing all password protections and security measures.
Oasis Security analysts identified multiple independent intrusion incidents where different threat actors exploited CVE-2025-54236 against Magento environments across various geographical regions, demonstrating widespread knowledge and weaponization of this flaw.
The research team discovered that attackers had scanned for vulnerable systems on a massive scale, identifying over 1,000 vulnerable Magento APIs and successfully compromising 200 websites with root-level administrative access.
Infection mechanism
The infection mechanism reveals how attackers systematically leveraged this vulnerability to establish complete control over victim infrastructure.
Once attackers gained initial access through session hijacking, they escalated their privileges to obtain root access, the highest level of system control on Linux servers.
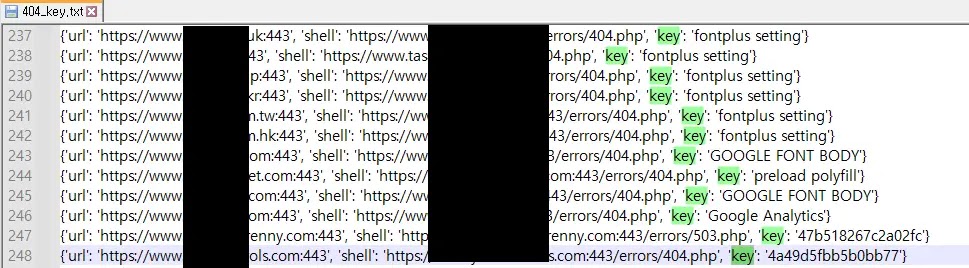
This persistence tactic allowed them to deploy web shells, which are small scripts that grant attackers remote command execution capabilities for ongoing system manipulation and data theft.
Evidence shows that compromised systems contained sensitive files displaying system user accounts and credentials, indicating thorough system exploration and potential data exfiltration.
The investigation uncovered command and control infrastructure operating from Finland and Hong Kong, with separate threat actors conducting web shell deployment operations specifically targeting Magento sites in Canada and Japan.
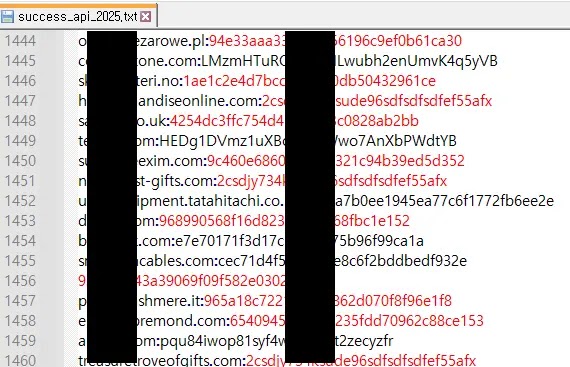
The attackers maintained detailed logs of compromised websites and deployed shell paths, demonstrating organized operational security and systematic targeting strategies.
Organizations running Magento must immediately patch this vulnerability and audit their server logs for suspicious session token usage.
The widespread nature of this campaign underscores the critical importance of timely security updates and continuous monitoring of e-commerce platforms hosting valuable customer data and payment information.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.