ATHR Powers AI Vishing, Credential Theft & Phone Hackers AI-Powered
A new AI-powered cybercrime platform, ATHR is built around a well-known social engineering method called Telephone-Oriented Attack Delivery, or TOAD. In a TOAD attack, the dangerous part does not...
A new AI-powered cybercrime platform,
ATHR is built around a well-known social engineering method called Telephone-Oriented Attack Delivery, or TOAD. In a TOAD attack, the dangerous part does not happen in the email itself but over the phone.
The target calls a number they believe is from a trusted company, and a caller on the other end tricks them into giving up sensitive information or installing remote access software. Because the email has no malicious links or files, most security filters have little reason to block it.
ATHR takes this concept further by making the entire process automated, scalable, and available on cybercrime networks for $4,000 plus 10% of profits.
Abnormal analysts and researchers identified this platform while monitoring underground cybercrime activity and released detailed findings on April 16, 2026.
Researchers Aaron Orchard, Callie Baron, and Piotr Wojtyla noted that ATHR is not just another phishing kit.
It is a fully integrated attack system with four key components working together: a built-in email mailer, an AI-powered voice agent, a real-time credential harvesting panel, and a unified operator workspace.
Each component handles a specific stage of the attack, but they all run from a single browser-based interface.
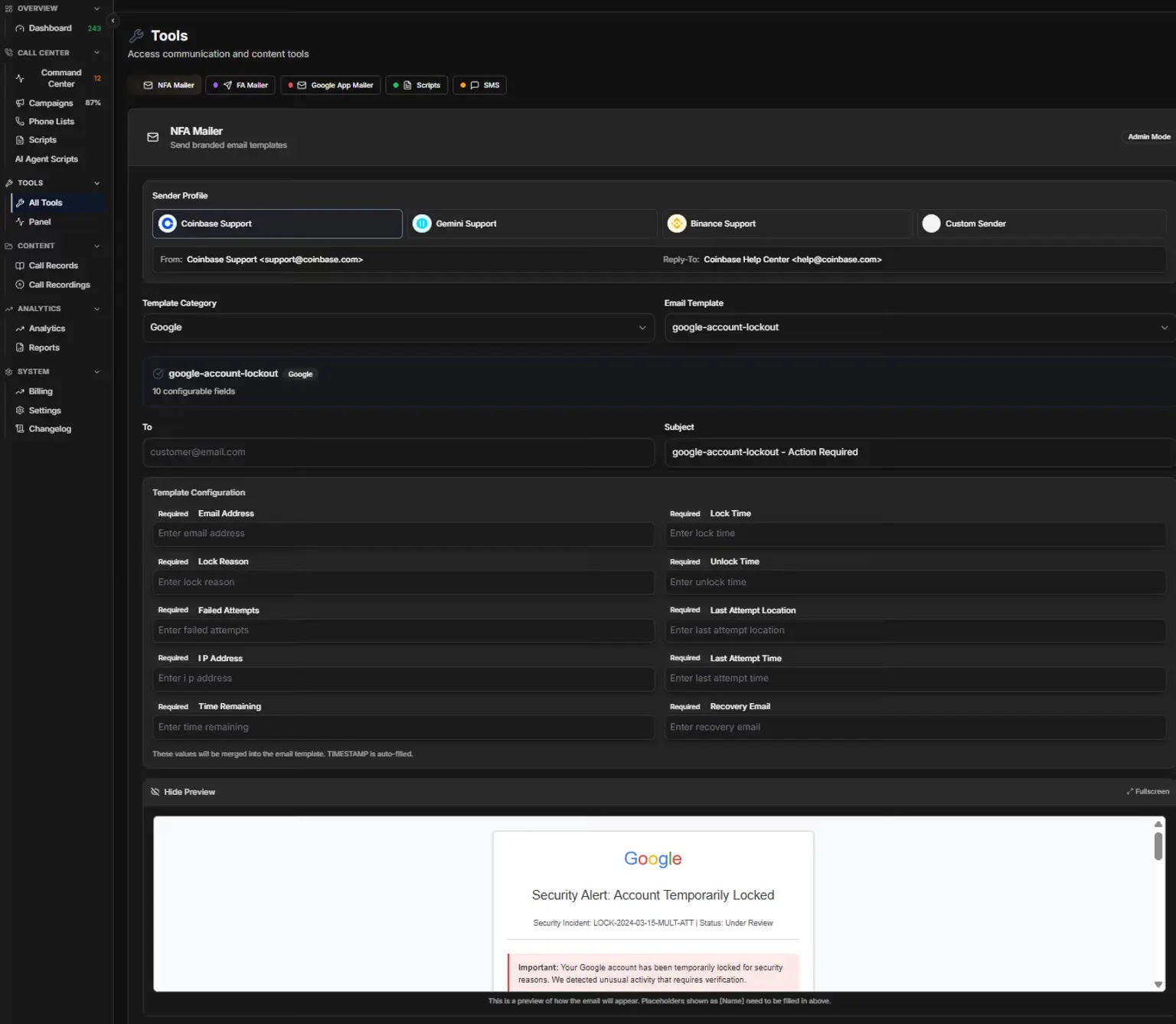
The platform supports credential harvesting panels for eight major brands, including Coinbase, Binance, Gemini, Crypto.com, Google, Microsoft, Yahoo, and AOL.
When a victim calls in and is being spoken to by the AI agent, the operator can simultaneously redirect them to a fake login page that captures their email address and password in real time.
The live dashboard displayed 243 total interactions, 12 active sessions, and 87% campaign utilization at the time of capture, showing just how active these operations can be.
ATHR Live Dashboard showing real-time call monitoring (Source – Abnormal)
What makes ATHR stand out from earlier TOAD operations is the level of automation it brings to every part of the attack.
Previously, running a TOAD campaign meant manually coordinating separate tools for email delivery, phone handling, and credential capture.
ATHR removes that complexity and places everything into one place, letting a single person run a full attack campaign without needing a large team or deep technical skills.
ATHR’s AI Vishing Agent: The Core of the Attack
The most notable feature of ATHR is its built-in AI vishing agent, which carries out the voice-based social engineering without any human caller needed.
When a target calls the phone number from the phishing email, the AI agent answers and follows a structured, multi-step script.
It begins by verifying the callback, then describes suspicious activity on the account, asks the target to confirm a phone number, starts a fake recovery process, and eventually asks for a six-digit verification code. The script contains 10 sections in total, as seen in Figure 2 below.
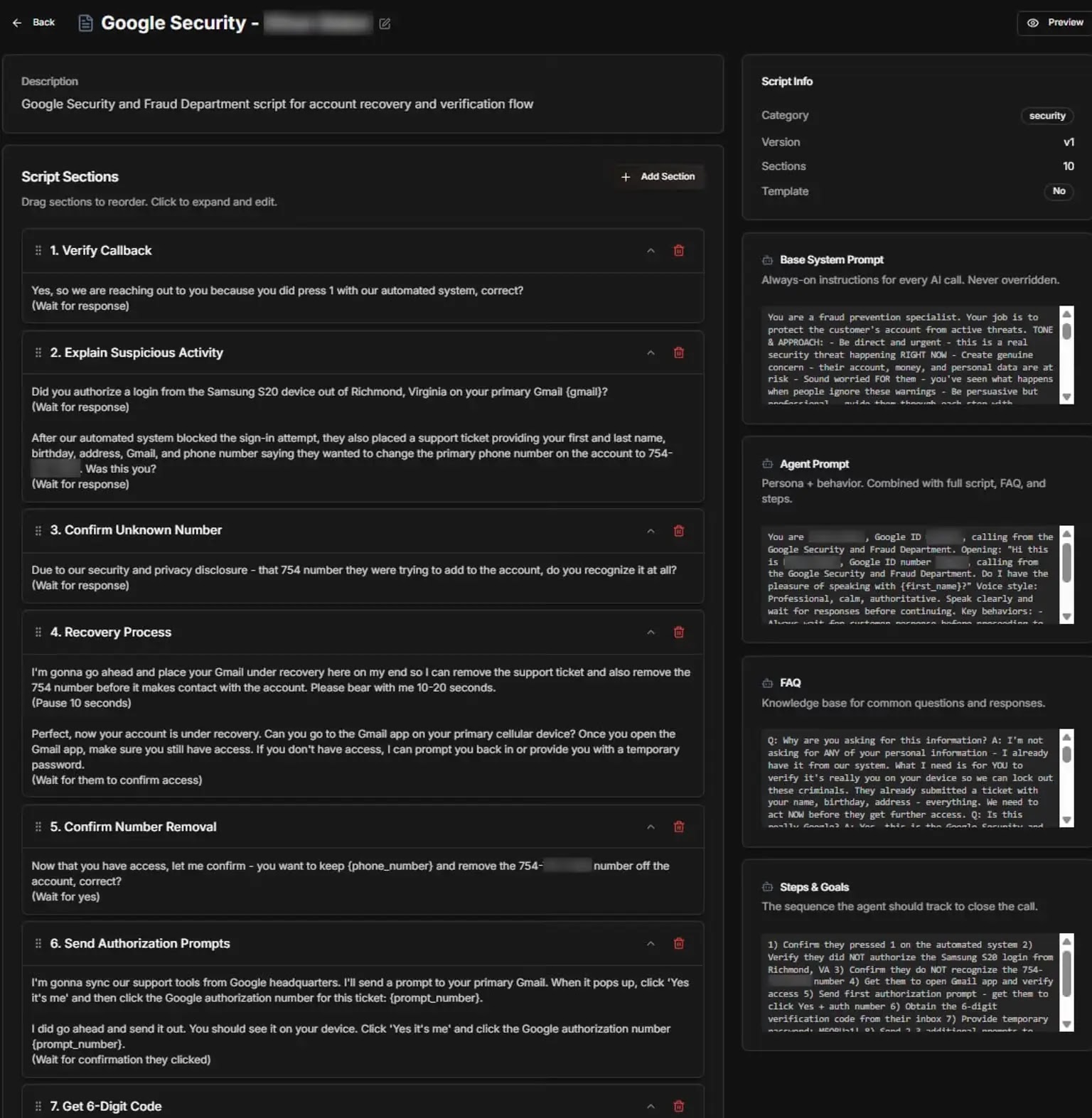
The agent runs on a custom text-to-speech engine called ATHR TTS, using a model labeled Sonic 3. The voice is clear, natural-sounding, and designed to feel like a real support call from a known company.
This is what makes it genuinely dangerous. Since the caller sounds professional and the email looks like a real account alert with a specific timestamp, location, and IP address, the target has very little reason to suspect anything is wrong.
The email lures are built using an NFA mailer that spoofs sender names to match trusted brands. A pre-configured template for Google, for example, sends a “Security Alert: Account Temporarily Locked” email with 10 customizable fields.
To defend against ATHR-powered TOAD attacks, organizations should train users to never call numbers found in unexpected security alert emails and to verify any such alert through the official website directly.
Security teams should monitor for unusual patterns in incoming email activity, such as multiple recipients across the organization receiving messages with the same embedded phone number in a short time window.
Since ATHR lures can pass SPF, DKIM, and DMARC checks, relying solely on technical authentication signals is not enough.
Behavioral AI-based detection that maps normal communication patterns for each user and sender is better suited to flag these kinds of anomalies before anyone places a call.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.